Navigating the Maze: A Researcher's Guide to Solving Data Collection Challenges in Regulatory Frameworks
This article provides a comprehensive roadmap for researchers and drug development professionals grappling with data collection amidst complex and evolving regulatory landscapes.
Navigating the Maze: A Researcher's Guide to Solving Data Collection Challenges in Regulatory Frameworks
Abstract
This article provides a comprehensive roadmap for researchers and drug development professionals grappling with data collection amidst complex and evolving regulatory landscapes. It addresses the foundational challenges of regulatory divergence and data privacy laws, offers methodological strategies for ensuring data quality and ethical compliance, presents troubleshooting techniques for common pitfalls like data silos and bias, and explores validation frameworks for Automated Compliance Checking (ACC). The guide synthesizes practical steps to build robust, efficient, and compliant data collection processes that accelerate biomedical research and ensure regulatory adherence.
Understanding the 2025 Regulatory Landscape and Its Data Challenges
The Growing Challenge of Regulatory Divergence and Fragmentation
Technical Support Center
This support center provides troubleshooting guides and FAQs to help researchers, scientists, and drug development professionals navigate data collection challenges within complex and fragmented regulatory frameworks.
Frequently Asked Questions (FAQs)
1. What is regulatory divergence and how does it impact multi-jurisdictional clinical trials? Regulatory divergence refers to the growing phenomenon where different countries, states, or regions enact and enforce differing, sometimes conflicting, rules and standards [1]. For multi-jurisdictional clinical trials, this creates significant complexity. You may face incompatible requirements for data sharing, informed consent, and privacy protection between, for example, U.S. FDA guidelines and the European Medicines Agency (EMA) regulations [2]. This divergence can mandate complex study designs, increase compliance costs, and risk delays if not managed proactively.
2. Our data collection protocol was approved in the U.S.; why was it rejected for the same trial in Europe? Even if the core science is identical, regional regulatory frameworks have distinct requirements. A common point of failure is data privacy and sharing. Your protocol might comply with U.S. standards but fall short of the stricter informed consent mandates for data sharing required by some European authorities or institutional review boards [2]. Always investigate local data-sharing policies and consent requirements during the initial planning phase, not after a rejection.
3. How can we troubleshoot a clinical trial data-sharing plan that is being blocked by intellectual property concerns? Resistance from sponsors or investigators due to intellectual property (IP) and data exclusivity is a frequent challenge [2]. To troubleshoot:
- Root Cause Analysis: Determine if the concern is about sharing raw data, analyzed results, or both.
- Implement a Controlled-Access Model: Instead of open access, propose a managed system where data is shared under a strict data-sharing agreement that protects IP. Most clinical trial agencies (65%) mandate such agreements [2].
- Leverage Policy: Reference guidelines from international bodies like the International Committee of Medical Journal Editors, which often require data sharing as a condition of publication [2].
4. What is the best way to design a data collection strategy that remains compliant amid shifting state-level AI and privacy laws? With a general pullback of federal initiatives in some areas and more emphasis by states, you must build an agile strategy [1] [3].
- Define Clear Goals: Start by understanding the specific problem you are trying to solve and what data is most valuable to your stakeholders [4].
- Choose Flexible Methods: Utilize methods that can adapt to new consent or data anonymization requirements, such as surveys with configurable consent modules [4].
- Centralize Compliance Tracking: Replace siloed systems with a single source of truth that can track and apply regulatory changes from multiple states in real-time [5].
5. We are encountering inconsistent quality control results between our U.S. and Asian manufacturing sites. How should we investigate? Inconsistent quality results often stem from regulatory fragmentation in Good Manufacturing Practice (GMP) interpretation and enforcement.
- Initiate a Root Cause Analysis: Follow a structured approach to determine the "what, when, who, where, how, and why" of the quality defect [6].
- Standardize Analytical Methods: Ensure both sites use the same validated analytical techniques (e.g., SEM-EDX for inorganic contaminants, Raman spectroscopy for organic particles) and reference standards [6].
- Audit the Quality Management System: Investigate differences in local procedures, personnel training, equipment qualification, or raw material sourcing that may be influenced by local regulatory focus areas [6].
Troubleshooting Guides
Guide 1: Troubleshooting Data Sharing and Privacy Compliance
This guide helps resolve issues related to sharing clinical trial data across borders with different privacy laws.
- Problem: Inability to share or combine clinical trial data from different countries for a pooled analysis.
- Required Materials:
- Data Sharing Agreements (DSAs) from all relevant jurisdictions.
- Original informed consent forms from all trial participants.
- List of all data elements to be shared, with classification (e.g., anonymized, pseudonymized).
- Step-by-Step Resolution:
- Verify Participant Consent: Check if the original informed consent from all study sites explicitly permits the future sharing of anonymized data for secondary research. If not, this is a primary blocker [2].
- Anonymize Data: Apply a robust anonymization technique (e.g., removal of all 18 HIPAA identifiers) to create a dataset that is no longer considered personal data under stricter laws [2].
- Execute Data Sharing Agreements: Draft and execute DSAs with all involved parties. These agreements should outline the purpose of data use, security protocols, and prohibitions against re-identification [2].
- Submit to Review Committee: Prepare and submit a data-sharing proposal to the overseeing committee (e.g., an independent review board), which is required by 71% of clinical trial agencies [2].
Table: Key Elements of a Data-Sharing Agreement
| Element | Description | Function in Compliance |
|---|---|---|
| Data Use Purpose | Clearly defined research objectives for the shared data. | Limits data use to pre-approved purposes, aligning with consent and privacy laws. |
| Security Protocols | Encryption standards, access controls, and data storage specifications. | Ensures technical safeguards meet the requirements of all involved regulatory jurisdictions. |
| Publication Terms | Agreements on authorship, acknowledgment, and data citation. | Manages intellectual property concerns and promotes collaborative transparency. |
| Audit Rights | Provisions for verifying compliance with the DSA. | Provides a mechanism for regulators and sponsors to ensure ongoing adherence. |
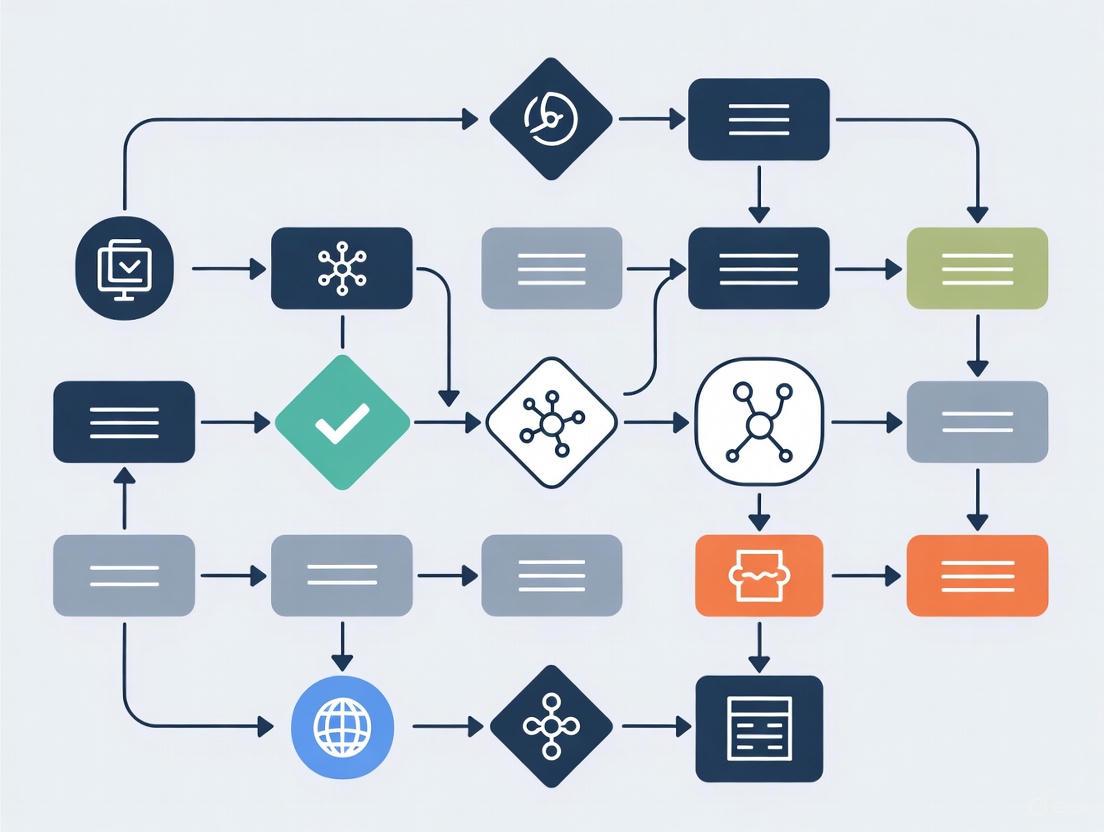
The following workflow diagram outlines the key stages of data collection and regulatory compliance verification in a multi-jurisdictional research project.
Guide 2: Troubleshooting Regulatory Fragmentation in Drug Development
This guide addresses operational challenges when regulatory requirements diverge during the drug development and manufacturing process.
- Problem: A quality control (QC) method validated for a drug product in one region is rejected by a regulatory agency in another region.
- Required Materials:
- Original validation protocol and report.
- Regulatory guidance documents (e.g., ICH, FDA, EMA) pertaining to analytical method validation from both regions.
- Complete data from the method validation study.
- Step-by-Step Resolution:
- Perform a Gap Analysis: Compare your current validation data against the specific requirements outlined in the guidelines of the rejecting agency. Pay close attention to acceptance criteria for parameters like specificity, accuracy, and precision [6].
- Identify Root Cause: The discrepancy is often due to differences in required validation parameters, sample matrix considerations, or acceptance criteria thresholds [1] [6].
- Design Bridging Studies: Develop a supplemental validation (or "bridging") study to generate data that specifically addresses the gaps identified. This may involve testing additional sample types or demonstrating robustness under different conditions [7].
- Compile and Submit: Integrate the new data from the bridging studies with your original validation report into a comprehensive submission for the reviewing agency [7].
Table: Research Reagent Solutions for Compliance and Quality Assurance
| Reagent/Solution | Function | Application in Troubleshooting |
|---|---|---|
| Positive Control Probes (e.g., PPIB, POLR2A) | Verify sample RNA integrity and assay performance. | Essential for qualifying sample quality in RNA-based assays, ensuring data reliability across different labs [8]. |
| Negative Control Probes (e.g., dapB) | Assess background noise and non-specific signal. | Critical for validating the specificity of your assay, a key parameter for regulatory acceptance [8]. |
| Reference Standards | Provide a benchmark for identifying and quantifying compounds. | Used to troubleshoot and validate analytical methods (e.g., HPLC, GC-MS) across different manufacturing sites to ensure consistency [6]. |
| Protease Solution | Permeabilizes tissue to allow probe access to RNA. | Requires precise optimization for different tissue types and fixation protocols to ensure consistent results, a common variable in multi-site studies [8]. |
The following diagram illustrates a systematic approach to troubleshooting quality defects in pharmaceutical manufacturing, a common challenge in a fragmented regulatory environment.
Troubleshooting Common Compliance Challenges
This guide addresses frequent technical and operational issues encountered when implementing key data privacy regulations in a research environment.
How do we resolve incomplete data subject rights handling under GDPR?
The Problem: Researchers cannot efficiently address requests from data subjects (e.g., EU research participants) for access, rectification, or erasure of their personal data, leading to non-compliance.
The Solution:
- Create a Clear DSAR Process: Establish a formal, documented workflow for receiving, tracking, and fulfilling Data Subject Access Requests (DSARs) within the GDPR-mandated timeline of one month [9].
- Implement Management Tools: Utilize specialized software to manage and document these requests, creating a verifiable audit trail [9].
- Map Data Flows: Develop and maintain a data processing register that details what personal data is collected, why it is processed, and where it is stored. This is essential for locating data to fulfill requests [10].
How can we manage third-party and vendor risks under GDPR and HIPAA?
The Problem: Research collaborators, cloud providers, or contract research organizations (CROs) that process personal data or protected health information (PHI) introduce compliance vulnerabilities.
The Solution:
- Perform Vendor Due Diligence: Conduct thorough risk assessments on all vendors before sharing data. For HIPAA, this involves sending vendors a security risk analysis and ensuring their security controls are adequate [11].
- Execute Compliant Agreements: Always have a signed Business Associate Agreement (BAA) in place for HIPAA compliance before sharing PHI [12] [11]. For GDPR, create detailed data processing agreements with vendors that outline their data protection responsibilities [9].
How do we address the failure to conduct a required Risk Analysis for HIPAA?
The Problem: An organization-wide security risk analysis, required annually or when operational changes occur, has not been performed, leaving Protected Health Information (PHI) vulnerable.
The Solution:
- Conduct an Enterprise-Wide Risk Analysis: Perform a formal risk analysis to identify and document vulnerabilities in your security practices related to electronic PHI (ePHI). This is not optional and is one of the most common violations penalized by regulators [12] [11].
- Implement a Risk Management Process: The risk analysis must be actionable. Identified risks must be prioritized and addressed in a reasonable time frame. Knowing about risks and failing to manage them is a major violation [12].
How do we fix inadequate access controls for sensitive data under HIPAA and SOX?
The Problem: Lack of proper controls allows unauthorized personnel to access sensitive financial data (SOX) or electronic Protected Health Information (HIPAA).
The Solution:
- Implement Strict Access Controls: Enforce role-based access controls to ensure individuals can only access data necessary for their job functions [11].
- Ensure Segregation of Duties (SoD): For SOX compliance, design controls so that no single individual has control over all aspects of a critical financial transaction, preventing fraud and errors [13].
- Apply Encryption: Encrypt ePHI on portable devices like laptops and USBs. If encryption is not used, an equivalent security measure must be implemented and documented [12].
How do we avoid delays in providing patients access to their health records under HIPAA?
The Problem: Research participants or patients are denied timely access to their medical records or are overcharged for copies, violating the HIPAA Right of Access rule.
The Solution:
- Adhere to the 30-Day Rule: Provide patients with access to their health records within 30 days of their request. The Office for Civil Rights (OCR) has made this a key enforcement priority [12].
- Avoid Overcharging: Fees for providing copies of records must be reasonable and based on permissible cost factors. Excessive charges are a common violation [12].
How do we prevent a "one-and-done" risk assessment approach under SOX?
The Problem: A single risk assessment is performed, but the internal controls are not updated to reflect business changes, new accounting guidance, or acquisitions.
The Solution:
- Conduct Annual Risk Assessments: Perform a formal risk assessment at least annually. For larger or more complex research organizations, supplement this with quarterly reviews [13].
- Adapt to Change: Continuously ask, "How do business changes affect our risk assessment?" This is critical when acquiring new entities, changing business operations, or experiencing significant staff turnover [13].
Frequently Asked Questions (FAQs)
Q1: What is the most common and costly mistake organizations make with GDPR compliance? A1: A frequent and complex challenge is underestimating the full scope of GDPR, particularly the difficulty of data discovery and mapping. Organizations often discover 3-5 times more third-party data processing relationships than initially documented and struggle with hidden data repositories and complex data flows, leading to a 50-70% scope underestimation [10].
Q2: We are a newly public company. What is a common SOX pitfall related to staff? A2: A major pitfall is gaps in headcount-related competencies. This occurs when staff overseeing key controls are spread too thin, lack specific training to understand the underlying risks, or when management fails to prioritize governance, leading the team to view compliance as a low priority [13].
Q3: What is a simple but critical control often missed for HIPAA compliance? A3: Failing to implement a robust data backup and disaster recovery plan is a common issue. With the rise of ransomware attacks in healthcare, HIPAA requires organizations to retain exact copies of PHI in both local and offsite locations to ensure data can be recovered and is accessible in an emergency [11].
Q4: How does the CCPA/CPRA impact research involving California residents? A4: These laws grant California residents the right to know, delete, and correct their personal information, and to opt-out of its "sale" or "sharing." Researchers must have mechanisms to honor these requests. Note that PHI collected by a HIPAA-covered entity may be exempt, but health data from other sources (e.g., wellness apps used in trials) likely falls under CCPA/CPRA [14].
Comparison of Key Regulatory Provisions
The table below summarizes the core requirements and penalties for the four regulations to aid in experimental design and compliance planning.
| Regulation | Primary Scope | Key Data Rights / Provisions | Penalties for Non-Compliance |
|---|---|---|---|
| GDPR [15] [14] | All organizations processing personal data of EU citizens. | Right to access, rectification, erasure ("right to be forgotten"), data portability, and object to processing. | Up to €20 million or 4% of annual global turnover, whichever is higher [14]. |
| CCPA/CPRA [15] [14] | For-profit businesses operating in California meeting specific revenue/data thresholds. | Right to know, delete, and correct personal information; right to opt-out of sale/sharing of data; non-discrimination. | Fines of up to $7,500 per intentional violation [14]. |
| HIPAA [15] [12] | Healthcare providers, health plans, healthcare clearinghouses, and their Business Associates. | Safeguards for Protected Health Information (PHI); patient rights to access and amend their health records; breach notification. | Fines range from $100 to $50,000 per violation, with an annual maximum of $1.5 million [12] [14]. |
| SOX [15] [14] | Publicly traded companies in the U.S. and their auditors. | Accuracy and reliability of corporate financial disclosures; secure storage of financial records for at least 5 years; internal controls over financial reporting. | Steep fines and potential imprisonment for executives [14]. |
Experimental Protocol: Conducting a Regulatory Risk Assessment
This protocol provides a methodology for identifying and mitigating data privacy risks within a research project, addressing core requirements of HIPAA and GDPR.
1. Objective: To systematically identify, assess, and document risks to the confidentiality, integrity, and availability of sensitive research data (e.g., PHI, personal data) and establish a treatment plan.
2. Materials:
- Risk Register Database: A centralized system (e.g., SQL database, specialized GRC software) for logging and tracking risks.
- Data Flow Mapping Tool: Software capable of creating visual data flow diagrams (e.g., Lucidchart, Draw.io) to identify all data touchpoints.
- Vendor Assessment Questionnaire: A standardized tool for evaluating third-party data processor security controls [11].
3. Methodology:
- Step 1: Scoping & Pre-planning. Define the boundaries of the assessment (e.g., a specific clinical trial, research department). Secure executive sponsorship to ensure resource allocation [10].
- Step 2: Data Discovery & Mapping. Identify all data repositories, including shadow IT and legacy systems. Document the flow of data from collection through analysis, storage, and sharing/disposal, noting all third-party transfers [10].
- Step 3: Threat & Vulnerability Identification. Using the data map, identify potential threats (e.g., unauthorized access, data corruption) and system vulnerabilities (e.g., lack of encryption, weak access controls) [12] [11].
- Step 4: Risk Analysis & Likelihood Impact Matrix. Analyze each risk by estimating its likelihood and potential impact on the research project and participants. Prioritize risks (e.g., High, Medium, Low) for treatment. This step is mandatory for HIPAA [12] [11].
- Step 5: Risk Treatment. Define action plans to mitigate, accept, avoid, or transfer each high-priority risk. Assign an owner and a deadline for each mitigation action.
- Step 6: Documentation & Reporting. Document the entire process, findings, and treatment plans. This documentation is critical evidence for auditors and regulators [12] [13].
- Step 7: Schedule Review. This is not a one-time activity. Schedule the next assessment, typically within one year or after any major change in the research process [13].
Compliance Workflow Diagram
Compliance Implementation Workflow
| Tool / Resource | Function in Compliance Process |
|---|---|
| Data Processing Register | A centralized record of all data processing activities, required under GDPR, to document what data is collected, why, and how it flows through the organization [9]. |
| Security Risk Analysis Software | Tools to systematically identify and assess risks to the confidentiality, integrity, and availability of sensitive data, fulfilling a core requirement of HIPAA and NIST [12] [15]. |
| Access Control Management System | Software that enforces role-based access to ensure only authorized personnel can access sensitive data, a key control for both HIPAA and SOX [11] [13]. |
| Business Associate Agreement (BAA) / Data Processing Agreement (DPA) | Legally required contracts under HIPAA and GDPR to ensure third-party vendors protect data to the required standard [12] [9]. |
| Data Subject Access Request (DSAR) Portal | A system to efficiently receive, track, and fulfill requests from individuals exercising their data rights under GDPR and CCPA [9]. |
Regulatory Intersection and Data Flow Logic
Data Type to Regulation Mapping
Technical Support Center: Troubleshooting Data Governance in Research
This support center provides practical guidance for researchers, scientists, and drug development professionals navigating data governance challenges at the intersection of AI, IoT, Cloud, and regulatory frameworks.
Troubleshooting Guides
Problem: AI Model Produces Biased or Inaccurate Results A machine learning model for patient stratification is showing signs of performance decay and potential bias, leading to unreliable predictions.
Diagnosis Checklist:
- Data Drift: Have the statistical properties of the live, incoming data changed compared to the model's original training data? [16]
- Bias in Training Data: Was the training dataset representative of the entire target population, including diverse racial, ethnic, and gender groups? [17]
- Poor Data Lineage: Can you trace the origin of the data and the transformations it underwent before training? A lack of lineage often makes bias untraceable. [17]
- Data Quality: Are there issues with the accuracy, completeness, or consistency of the input data? [18]
Resolution Protocol:
- Audit for Fairness: Use fairness audit tools to quantify bias across different demographic segments in your dataset. [17]
- Retrain with Representative Data: Curate a new, diverse, and representative training dataset. Apply pre-processing de-biasing techniques like reweighting or resampling. [17]
- Establish a Feedback Loop: Implement continuous monitoring to detect data and concept drift, triggering automatic model retraining. [16]
- Document with Model Cards: Create detailed documentation (model cards) that capture the model's intended use, training data, and known limitations to ensure transparency. [17]
Problem: Data Silos Impeding Cross-Functional Research Critical research data is trapped in isolated systems (e.g., separate CRMs, IoT sensor databases, lab systems), preventing a unified view.
Diagnosis Checklist:
Resolution Protocol:
- Implement a Centralized Architecture: Invest in a centralized data platform like a data lakehouse or fabric architecture to consolidate structured and unstructured data. [17]
- Use ETL/ELT Pipelines: Create automated pipelines to extract, transform, and load data from various sources into the centralized platform. [17]
- Appoint Data Stewards: Designate data stewards for cross-functional coordination and to enforce enterprise-wide governance policies on integrated sources. [17] [19]
- Deploy a Data Catalog: Use a data catalog to inventory all data assets, making them discoverable and understandable to authorized users across the organization. [19]
Problem: Ensuring Regulatory Compliance in a Multi-Cloud Environment A clinical trial spans multiple cloud regions, raising concerns about compliance with data sovereignty laws (like GDPR) and specific regulations (like ICH E6(R3) GCP).
Diagnosis Checklist:
- Unclear Data Residency: Do you know the physical geographic location of every server storing your regulated clinical data? [19]
- Lacking Data Lifecycle Policies: Are there no clear policies for data retention, archiving, and purging as required by regulations? [19]
- Inconsistent Access Controls: Are access controls weak or inconsistent across different cloud platforms, increasing the risk of data leakage? [19]
Resolution Protocol:
- Classify and Catalog Data: Use an automated data catalog to classify data assets, tagging sensitive and regulated data (e.g., patient PII). [19]
- Enforce Data Residency Policies: Configure cloud storage policies to automatically enforce data sovereignty rules, preventing data from being stored in non-compliant jurisdictions. [19]
- Automate Compliance Workflows: Implement automated workflows for managing data subject requests (e.g., right to be forgotten) and consent. [17]
- Maintain Audit Trails: Ensure your cloud governance tools provide detailed audit trails for all data access and modifications, which are essential for regulatory audits. [17] [19]
Frequently Asked Questions (FAQs)
Q1: What is the most critical first step in governing data for an AI-based research project? The most critical first step is data classification. Before using data to train any model, you must identify and tag sensitive elements like Personally Identifiable Information (PII), protected health information (PHI), and intellectual property. This process is foundational for applying appropriate security controls, ensuring compliance, and avoiding the use of copyrighted or harmful content in your training sets. [17] [19]
Q2: How does 'model drift' impact our research, and how can we monitor for it? Model drift occurs when an AI model's predictions become less accurate over time because the live data it processes has changed from the data it was trained on. [16] In research, this can lead to flawed conclusions, invalidated results, and compliance risks. Monitoring involves:
- Technical Monitoring: Continuously tracking performance metrics (accuracy, precision, recall) and using statistical techniques to detect data drift and concept drift. [16]
- Operational Monitoring: Setting up dashboards with alerts for when metrics deviate from predefined thresholds. [16]
Q3: Our research uses IoT medical sensors. How do we ensure the quality and trustworthiness of this streaming data? Governance for IoT data requires a focus on the entire data pipeline:
- At the Edge: Implement data validation checks where possible to filter out corrupt or anomalous readings at the source.
- In Transit: Ensure data is encrypted during transmission from the sensor to the cloud platform. [19]
- At Rest: Upon ingestion into your cloud data lake or platform, run automated data quality checks to profile, validate, and cleanse the data. Establish data quality metrics for accuracy and consistency and monitor them continuously. [19] [18]
Q4: We are preparing a Diversity Action Plan for an FDA submission. How can technology aid in governance here? Technology is crucial for executing and demonstrating the effectiveness of your Diversity Action Plan.
- Recruitment & Engagement: Use Clinical Trial Management Systems (CTMS) and participant engagement platforms to simplify recruitment and enrollment across diverse populations, offering user-friendly digital interfaces. [20]
- Data Collection & Monitoring: Leverage eClinical tools like eSource and eConsent to capture data directly and monitor recruitment metrics in real-time against your diversity goals. [20]
- Data Analysis: Use analytics to track enrollment rates by demographic, allowing you to identify gaps and adjust your outreach strategies proactively. [20]
Quantitative Data on Data Governance Challenges
Table 1: Cost and Organizational Impact of Poor Data Governance
| Metric | Statistic | Source |
|---|---|---|
| Average Annual Cost of Bad Data | $12.9 million | Gartner (via [17]) |
| Reduction in Workforce Productivity | Up to 20% | Harvard Business Review (via [17]) |
| Increase in Operational Costs | Up to 30% | Harvard Business Review (via [17]) |
| Organizations Viewing Lack of Data Governance as Primary AI Inhibitor | 62% | KPMG (via [21]) |
Table 2: AI Adoption and Governance Maturity Landscape
| Metric | Statistic | Source |
|---|---|---|
| Global Organizations Using or Planning to Adopt AI | 84% | Quinnox (via [17]) |
| Companies That Have Integrated AI into at Least One Function | 79% | McKinsey (via [17]) |
| Organizations Lacking a Clear AI Strategy/Roadmap | ~50% (Nearly 1 in 2) | BCG x MIT Sloan Report (via [17]) |
| Generative AI Initiatives Described as "Fully Mature" | 1% | BCG x MIT Sloan Report (via [17]) |
Experimental Protocol: Implementing a 5-Step Data Governance Framework for an AI Research Project
This protocol provides a step-by-step methodology for establishing foundational data governance, aligned with the framework from the search results. [17]
1. Charter: Establish Governance with AI in Mind
- Objective: Define a clear governance charter assigning accountability for data integrity and ethical use.
- Procedure:
- Form a cross-functional team with members from data science, legal, compliance, and senior leadership (C-suite involvement is critical). [17] [21]
- Draft a charter that explicitly addresses AI-specific risks like model bias, hallucinations, and prompt injection attacks. [17]
- Define and document roles: Data Owners, Data Stewards, and Data Scientists, with clear responsibilities. [19] [18]
2. Classify: Know Your Data Before You Use It
- Objective: Identify and tag sensitive and regulated data within your research datasets.
- Procedure:
- Use automated data cataloging and scanning tools to discover and profile data. [19]
- Apply metadata tags to classify data (e.g., "PII," "PHI," "Confidential Intellectual Property"). [17]
- Vet and document all third-party and public data sources used for training to avoid copyright or quality issues. [17]
3. Control: Apply Guardrails to Who Uses What and How
- Objective: Implement security and access controls to prevent data misuse.
- Procedure:
- Implement role-based access control (RBAC) policies in your cloud data platform. [17] [19]
- For Generative AI projects, deploy prompt filters and input sanitization techniques. [17]
- Apply principles of data minimization, ensuring users only have access to the data strictly necessary for their research tasks. [17]
4. Monitor: Make AI Data Transparent and Traceable
- Objective: Establish ongoing monitoring for data quality, model performance, and bias.
- Procedure:
- Implement automated data lineage tools to track the origin and movement of data throughout its lifecycle. [17] [19]
- Set up dashboards to monitor key metrics for data quality (accuracy, completeness) and model performance (accuracy, drift). [16]
- Log all model inputs and outputs for auditability, essential for regulatory compliance under frameworks like the EU AI Act. [17]
5. Improve: Adapt as Risks and Regulations Evolve
- Objective: Create a feedback loop for continuous improvement of the governance framework.
- Procedure:
Data Governance Workflow Visualization
The Researcher's Toolkit: Essential Data Governance Solutions
Table 3: Key Research Reagent Solutions for Data Governance
| Item / Solution | Function in Data Governance |
|---|---|
| Data Catalog | A centralized tool for inventorying, classifying, and making data discoverable. It automatically scans data sources to build a searchable inventory, which is foundational for data classification and lineage. [19] |
| Automated Lineage Tools | Track the origin, movement, and transformation of data throughout its lifecycle. This is critical for troubleshooting AI models, ensuring reproducibility, and passing regulatory audits. [17] [19] |
| Model Card | A documentation framework for providing context and transparency into an AI model. It details the model's intended use, training data, performance metrics, and ethical considerations. [17] |
| eClinical Suite (eSource, CTMS, eConsent) | A set of specialized software tools for clinical research. They streamline data capture (eSource), manage trial operations and recruitment (CTMS), and ensure a compliant informed consent process (eConsent), directly supporting data integrity and regulatory adherence. [20] |
| Fairness Audit Tools | Software libraries and applications used to detect and quantify bias in datasets and AI models. They help researchers ensure their models are fair and do not discriminate against protected groups. [17] |
Defining Research Goals and Target Population for Regulatory Submissions
Troubleshooting Guides
Guide 1: Troubleshooting Target Population Definition
Table: Common Target Population Challenges and Solutions
| Challenge | Root Cause | Solution | Preventive Action |
|---|---|---|---|
| Enrollment Delays [22] | Long, unpredictable regulatory ethics timelines across countries. | Build realistic timelines (e.g., mean of 17.84 months observed) [22]. Engage local regulators early in protocol development [22]. | Develop a harmonized regulatory strategy with pre-emptive country-specific consultations [22]. |
| Lack of Population Diversity [23] | Failure to enroll historically underrepresented populations. | Select trial sites in demographically diverse locations and engage community health workers [23]. | Submit a formal Diversity Action Plan (DAP) to the FDA as required [23]. |
| Data Standardization Issues [24] | Lack of standardized data collection methods, only submission standards exist. | Implement robust internal data management practices and use predefined templates [25]. | Foster collaboration among pharma companies and vendors to establish collection standards [24]. |
| Protocol Non-Compliance [23] | Staff unfamiliarity with protocol or eagerness to enroll ineligible patients. | Immediate staff retraining and suspension of enrollment until compliance is confirmed [23]. | Implement rigorous pre-enrollment checklists and ongoing protocol training [23]. |
Guide 2: Troubleshooting Research Goal Alignment
Table: Aligning Research Goals with Regulatory Requirements
| Symptoms of Misalignment | Diagnostic Checks | Corrective Actions |
|---|---|---|
| Regulatory questions about product's market context or unmet need [25]. | Review submission documents: Is there a clear, cohesive narrative on product positioning? [25] | Thread key messaging throughout the eCTD. Use a project manager to ensure narrative consistency [25]. |
| FDA rejection for lacking Investigational New Drug (IND) application [23]. | Determine if the study is an "experiment" (regulated) or "medical practice" (generally not) [23]. | Consult FDA guidance: Randomized trials of unapproved drug uses typically require an IND [23]. |
| Delays due to shifting regulatory requirements [26]. | Regularly monitor official FDA guidance and policy updates [27]. | Proactively engage the FDA early for feedback and consider parallel submissions with other agencies (e.g., EMA) [26]. |
| Inability to leverage Real-World Evidence (RWE). | Assess if RWE could complement trials for safety or effectiveness data [28]. | Align RWE study design with FDA's RWE Accelerate initiative and use fit-for-purpose data sources [28]. |
Frequently Asked Questions (FAQs)
Q1: What is the single most common mistake in defining a target population, and how can I avoid it?
The most frequent and critical mistake is failing to ensure subjects meet all inclusion/exclusion criteria before enrollment, which is a top citation in FDA Warning Letters [23]. This often stems from staff's desire to help patients access investigational treatments. To avoid this, implement rigorous pre-screening checklists and continuous training that emphasizes the difference between the practice of medicine and the strict, protocol-driven nature of clinical research [23].
Q2: How can I use real-world evidence (RWE) to support the definition of my target population and research goals?
RWE allows you to study large, diverse datasets from real-world settings to understand treatment patterns, safety signals, and gaps in care [28]. You can use RWE to:
- Harness Big Data: Understand the natural history of a disease and identify disparities in care within different patient sub-groups [28].
- Support Accelerated Development: Complement clinical trials by providing additional evidence on how a drug works in broader, more representative populations outside the strict controls of a trial [28]. Engage with the FDA's RWE Accelerate initiative early to ensure your approach to using RWE is aligned with agency expectations [28].
Q3: What are the key differences between HIPAA "Authorization" and informed consent?
These are two separate regulatory requirements. Informed consent is required by federal human subject protection regulations and focuses on the risks and benefits of the research procedures themselves. HIPAA Authorization is required by the Privacy Rule and specifically governs how a covered entity may use and disclose a patient's Protected Health Information (PHI) for research [29]. While the requirements are different, the two documents are often combined into a single form for patient comprehension and administrative ease [29].
Q4: Our multi-country trial is facing significant regulatory delays. What strategic steps can we take?
Significant delays in multi-country trials, especially in resource-limited settings, are common, with mean regulatory timelines sometimes exceeding 17 months [22]. To mitigate this:
- Engage Early: Negotiate with international drug regulators and ethics committees during the protocol development phase, not after it is finalized [22].
- Harmonize Processes: Advocate for and participate in efforts to harmonize regulatory review processes across regions. This includes supporting training exchanges between in-country regulators and established agencies like the FDA or EMA [22].
- Plan for Variability: Allocate resources and build timelines that account for unpredictable regulatory environments in different countries [22].
Q5: What should we do if we receive an FDA Form 483 after a BIMO inspection?
Remain cooperative and acknowledge the issues during the closeout meeting. The most critical step is to provide a timely, robust written response within 15 business days [23]. Your response must detail a comprehensive corrective and preventive action plan (CAPA) and confirm any actions already completed. Demonstrating a clear commitment to addressing the findings can help prevent the issuance of a more severe Warning Letter [23].
Experimental Protocol: Defining a Target Population for a Regulatory Submission
Objective: To systematically define and justify a target population for a clinical study that will meet regulatory standards for approval.
Methodology:
Disease Natural History & Unmet Need Analysis:
- Utilize real-world data (RWD) from electronic health records (EHRs) or claims databases to characterize the patient population, including demographics, disease progression, and current treatment patterns [28].
- Define the unmet medical need that the investigational product aims to address.
Competitive Landscape & Clinical Trial History Review:
- Analyze previously approved products and clinical trials for the same or similar indications.
- Identify gaps in knowledge or populations that have been underrepresented (e.g., specific racial groups, elderly patients) to inform the development of a Diversity Action Plan [23].
Stakeholder Alignment and Regulatory Strategy:
- Hold an internal cross-functional team meeting to align on the target population and research goals.
- Schedule a pre-submission meeting with the regulatory agency (e.g., FDA) to present and refine the proposed target population and overall study design [25].
Protocol Finalization and Documentation:
- Translate the agreed-upon strategy into a precise protocol with unambiguous inclusion/exclusion criteria.
- Prepare a cohesive regulatory submission that tells a clear story, justifying the target population based on the analysis in steps 1-3 and threading this rationale throughout the submission documents [25].
Workflow Diagram
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Materials for Regulatory-Focused Research
| Item/Tool | Function in Research | Regulatory Consideration |
|---|---|---|
| HIPAA Authorization Form | Legally permits the use/disclosure of Protected Health Information (PHI) for research [29]. | Must be specific and can be combined with informed consent. An IRB can waive this requirement under certain conditions [29]. |
| Data Use Agreement (DUA) | Governs the sharing of a "Limited Data Set" (data with some indirect identifiers) with parties not named in the original IRB application [29]. | Required by HIPAA to share data with external collaborators not part of the core research team [29]. |
| Diversity Action Plan (DAP) | A formal plan to enroll a representative study population from historically underrepresented groups [23]. | Soon to be mandatory for certain clinical studies per FDA guidance to improve enrollment diversity [23]. |
| Standardized Data Templates (e.g., CDISC) | Provides a common structure and format for data submitted to regulatory agencies [24]. | While submission standards are mandated, internal collection standards are not, making internal templates vital for efficiency and accuracy [24]. |
| Real-World Data (RWD) Sources | Provides evidence on disease status and healthcare delivery from sources outside traditional clinical trials (e.g., EHRs, claims data) [28]. | Must be fit-for-purpose. The FDA's RWE Accelerate initiative provides a framework for using this data in regulatory decisions [28]. |
Troubleshooting Guides & FAQs
Data Management & Regulatory Compliance
Q: Our clinical trial data collection is often flagged by regulators as being non-compliant with GDPR and HIPAA. How can we ensure we collect necessary research data while respecting data minimization principles?
A: Implement a tiered data collection strategy and leverage privacy-enhancing technologies (PETs). Start by collecting only essential baseline data, then collect additional data points as the study progresses and justifies their need. Utilize technologies like federated learning, which enables collaborative research without transferring raw data between institutions, ensuring sensitive information remains localized. Always conduct a Data Protection Impact Assessment (DPIA) to outline what data is necessary and identify risks in processing activities [30].
Q: What are the most common data-related site challenges in clinical trials, and how can we address them?
A: According to a 2025 survey of clinical research sites worldwide, the top challenges are clinical trial complexity (35%), study start-up issues (31%), and site staffing (30%). To address these, focus on enhancing operational efficiency by streamlining and standardizing routine workflows while actively tracking key metrics against industry benchmarks. Additionally, invest in comprehensive staff training and implement strategies to enhance retention through ongoing educational opportunities [31].
Table: Top Clinical Research Site Challenges (2025)
| Challenge Area | Percentage of Sites Reporting | Key Mitigation Strategies |
|---|---|---|
| Complexity of Clinical Trials | 35% | Simplify protocol designs, reduce endpoints, streamline technology requirements |
| Study Start-up | 31% | Specialize in coverage analysis, budgets, and contracts; strategically outsource |
| Site Staffing | 30% | Invest in training, enhance retention, provide professional development |
| Recruitment & Retention | 28% | Implement DE&I strategies, harness technology to optimize participant experience |
| Long Study Initiation Timelines | 26% | Enhance communication with sponsors/CROs, standardize processes |
Q: How can we ensure our data management practices meet both FDA 21 CFR Part 11 requirements and support robust research outcomes?
A: Implement Clinical Data Management Systems (CDMS) that are compliant with regulatory standards while maintaining data integrity. Key steps include: maintaining secure, computer-generated, time-stamped audit trails; using validated systems to ensure accuracy, reliability, and consistency of data; and following Clinical Data Interchange Standards Consortium (CDISC) standards for data acquisition, exchange, and submission. Ensure your system provides adequate procedures and controls to guarantee data integrity, authenticity, and confidentiality [32].
Q: What strategies can help balance comprehensive data collection for complex trials with regulatory data minimization requirements?
A: Adopt these key strategies: First, implement pseudonymization and anonymization practices to reduce risk while retaining data utility. Second, utilize tiered data collection, starting with essential data and progressively collecting more as justified by study progression. Third, employ Privacy-Enhancing Technologies (PETs) like synthetic data and differential privacy. Fourth, conduct regular audits to ensure data collection aligns with minimization principles. Finally, maintain clear documentation of all data processing activities [30].
Data Integrity & Quality Assurance
Q: We're experiencing inconsistencies in our research data quality despite following protocols. What fundamental guidelines can improve data integrity?
A: Implement the Guidelines for Research Data Integrity (GRDI) which emphasize six core principles: accuracy, completeness, reproducibility, understandability, interpretability, and transferability. Key practical steps include: always keeping raw data in its original, unprocessed form; creating a comprehensive data dictionary that explains all variable names, coding categories, and units; saving data in accessible, general-purpose file formats like CSV; and avoiding combining information in single fields that cannot be easily separated later [33].
Q: How should we handle raw versus processed data to maintain scientific integrity?
A: Raw data should be preserved in its original, unprocessed form as equipment-generated physical records or data files with timestamps and write-protection. Export raw data into write-protected open formats (CSV, JSON) for long-term accessibility. For processed data, carefully document all cleaning procedures, transformations, and normalization techniques. Be aware that aggressive data cleaning may inadvertently eliminate valid data points or introduce bias, so thorough documentation is essential to minimize information loss and maintain dataset integrity [34].
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Data Management Resources for Regulatory Compliance
| Tool/Resource | Function/Purpose | Key Features/Benefits |
|---|---|---|
| Clinical Data Management Systems (CDMS) | Collection, cleaning, and management of subject data in compliance with regulatory standards | Audit trail maintenance, discrepancy management, 21 CFR Part 11 compliance [32] |
| Privacy-Enhancing Technologies (PETs) | Safeguard participant data while maximizing utility for research | Includes synthetic data, federated learning, differential privacy [30] |
| Data Protection Impact Assessment (DPIA) | Outline necessary data and identify processing risks | Ensures GDPR compliance, balances research needs with privacy requirements [30] |
| Clinical Data Interchange Standards Consortium (CDISC) Standards | Acquisition, exchange, submission, and archival of clinical research data | Includes SDTMIG and CDASH standards; supports regulatory submission [32] |
| eConsent Platforms | Facilitate informed consent processes across study sites | Streamline enrollment, automate routing and signature management, ensure version control [20] |
| Data Management Plan (DMP) | Roadmap for handling data under foreseeable circumstances | Describes database design, quality control, discrepancy management, database locking [32] |
Experimental Protocols & Workflows
Protocol: Implementing Tiered Data Collection for Regulatory Compliance
Objective: To systematically collect necessary research data while adhering to GDPR data minimization principles and maintaining research integrity.
Materials:
- Data Protection Impact Assessment (DPIA) framework
- Privacy-Enhancing Technologies (federated learning platforms, differential privacy tools)
- Anonymization and pseudonymization software
- Clinical Data Management System (CDMS) with audit trail capability
- Data validation and edit check programs
Methodology:
Pre-Collection Planning Phase
- Conduct comprehensive DPIA to identify essential data requirements
- Define data collection objectives aligned with research endpoints
- Establish data minimization thresholds and justification criteria
- Develop tiered data collection protocol with clear escalation triggers
Baseline Data Collection
- Collect only essential demographic and baseline characteristics
- Implement pseudonymization at point of collection
- Apply data validation checks in real-time
- Document all collection processes in audit trail
Progressive Data Tier Activation
- Activate additional data collection tiers only as study progression justifies need
- Require protocol amendment and ethics approval for each tier activation
- Re-assess data minimization principles at each tier transition
- Maintain comprehensive documentation of tier activation rationale
Quality Assurance & Compliance Monitoring
- Conduct regular audits of data collection against minimization principles
- Verify appropriateness of data points collected at each tier
- Ensure continued alignment with research objectives
- Document all compliance verification activities
Protocol: Ensuring Data Integrity Throughout Research Workflow
Objective: To maintain data accuracy, completeness, and reproducibility from collection through analysis while meeting regulatory standards.
Materials:
- Raw data preservation system (write-protected storage)
- Data dictionary template
- Standardized file formats (CSV, JSON, XML)
- Version control system
- Audit trail software
- Metadata documentation tools
Methodology:
Pre-Collection Preparation
- Develop comprehensive data dictionary with variable definitions, coding schemes, and units
- Establish standardized file naming conventions and version control protocol
- Define raw data preservation procedures and storage locations
- Select appropriate, sustainable file formats for long-term accessibility
Data Collection & Documentation
- Collect data directly into standardized formats
- Implement real-time data validation and edit checks
- Preserve raw data in write-protected, timestamped formats
- Document all collection methodologies, instrument calibrations, and environmental factors
Data Processing & Transformation
- Maintain clear separation between raw and processed data
- Document all data cleaning procedures, transformations, and normalization techniques
- Preserve processing scripts and algorithms with version control
- Implement reproducible data processing workflows
Quality Assurance & Metadata Management
- Conduct regular quality checks against GRDI principles
- Ensure metadata comprehensively describes dataset context and processing history
- Verify data reproducibility through periodic replication tests
- Prepare data for sharing and preservation according to FAIR principles
Regulatory Alignment Framework
Navigating 2025 Regulatory Challenges
The regulatory landscape in 2025 is characterized by significant shifts requiring adaptive data management strategies. Key trends include growing regulatory divergence and fragmentation, increased focus on Trusted AI systems, and evolving cybersecurity requirements [1]. Specific clinical trial updates include the FDA's movement toward single IRB reviews for multicenter studies, finalized ICH E6(R3) Good Clinical Practice guidelines emphasizing flexibility and digital technology integration, and reinforced commitments to diversity in clinical trials through Diversity Action Plans [20].
Table: 2025 Regulatory Priorities and Data Implications
| Regulatory Area | Key Requirements | Data Management Implications |
|---|---|---|
| AI Regulation | Trusted AI frameworks, ethical implementation | Enhanced data governance, algorithm transparency, bias monitoring [1] |
| Data Privacy | GDPR minimization, cross-border transfer rules | Tiered data collection, privacy-enhancing technologies, anonymization protocols [30] |
| Clinical Trial Modernization | ICH E6(R3) adoption, single IRB reviews | Risk-based quality management, centralized data systems, streamlined documentation [20] |
| Diversity & Inclusion | Diversity Action Plans, representative participation | Demographic data collection, barrier analysis, inclusive recruitment strategies [20] |
| Cybersecurity & Information Protection | Enhanced data protection, state-level regulations | Secure data storage, encryption protocols, access controls [1] |
Successful navigation of these regulatory requirements demands a proactive approach that integrates compliance considerations into research design from the outset, rather than as an afterthought. By implementing the protocols and strategies outlined in this technical support center, researchers can confidently pursue their scientific objectives while maintaining rigorous regulatory compliance.
Building a Methodologically Sound and Compliant Data Collection Process
Technical Support Center
Frequently Asked Questions
Q1: Our survey response rates are low, and we are concerned about non-response bias affecting our study's validity. What steps can we take?
A1: Low response rates are a common challenge that can compromise data representatiselected sampling method accurately reflects all relevant subgroups (e.g., age, gender) within your target population and address any barriers to participation [4]. Furthermore, ensure your survey design is accessible and user-friendly. Tools like SurveyCTO offer robust, secure, and scalable mobile data collection, which can be deployed even in areas with limited connectivity, thus widening your reach [4].
Q2: We have collected EHR data, but it is messy and inconsistent. How can we define a reliable patient cohort for our analysis?
A2: Defining a clean cohort from EHR data is a critical first step. We recommend you:
- Create a Source Registry: Document every data source, its origin, and a quality rating. This helps you understand the reliability of the data you are working with [35].
- Implement Data Validation: Establish systematic processes to verify information at the point of entry and throughout its lifecycle. This can include field-level validation in forms and automated post-collection cleaning to detect and handle duplicates or incomplete records [35].
- Collaborate with Extraction Engineers: Work closely with data extraction engineers to understand the origin of data quality issues. The extraction process itself can introduce artifacts, and an iterative collaboration is crucial for ensuring the final dataset is representative [36] [37].
Q3: During clinical observations, how can we minimize the effect of the observer on the subject's behavior (the Hawthorne Effect)?
A3: Minimizing observer bias is key to collecting authentic data.
- Use Non-Participant Observation: The researcher should observe without direct interaction with the participant whenever possible [38].
- Conduct Covert Observation (with ethical approval): In some study designs where participants are unaware they are being observed, you can capture more natural behavior. However, this must be approached with extreme caution and full compliance with ethical and regulatory standards, including informed consent requirements where applicable [38].
- Standardize Procedures: Develop a strict observational framework or checklist to ensure all researchers are recording behaviors systematically, which reduces interpreter bias [38].
Q4: Our sensor data streams are large and complex. How can we ensure the data is of high quality and integrated properly with our other data sources?
A4: Handling high-volume sensor data requires modern engineering approaches.
- Implement Automated Quality Assurance: Use frameworks with machine learning models to identify anomalies, duplicates, and inconsistencies in the data stream before it reaches your analytical systems [39].
- Adopt Cloud-Native and DataOps Practices: Utilize serverless data processing platforms that auto-scale and employ DataOps principles. This involves continuous integration and delivery pipelines that automate the testing, deployment, and monitoring of your data collection workflows [39].
- Ensure Compliance-by-Design: Embed regulatory requirements directly into your collection workflows. This includes automated policy enforcement for data masking, retention, and access controls based on the classified sensitivity of the data [39].
Q5: How can we ensure our data collection methods are compliant with regulations like GDPR or HIPAA?
A5: Privacy compliance is a fundamental responsibility.
- Obtain Informed Consent: Use clear, simple language—not legal jargon—to state what data you are collecting, how it will be used, and who it will be shared with. Offer granular choices, allowing individuals to opt into different types of communication separately [35].
- Maintain Consent Records: Keep a secure, auditable trail of when and how each individual gave their consent. This is a key requirement for demonstrating compliance [35].
- Implement Privacy by Design: Build privacy and security considerations into your technology from the ground up. Ensure systems that store or process personal data have robust security measures and access controls [35].
Troubleshooting Guides
Problem: Data flowing from multiple sources (e.g., ticketing platforms, mobile apps, CRM systems) arrives in incompatible formats (e.g., dates as "MM/DD/YY," "DD-MM-YYYY," and "Month Day, Year"), making merging and analysis impossible.
Solution:
- Create a Data Dictionary: Develop a central document that defines every data field you collect, specifying its name, format (text, number, date), and accepted values [35].
- Enforce Standardized Formats: Adopt industry standards where possible. For example, require dates to follow the ISO 8601 standard (YYYY-MM-DD) and use two-letter country codes (ISO 3166) instead of free-text country names [35].
- Use Field Validation: Implement validation rules in your data capture tools and forms to enforce correct formatting upon entry [35].
Issue: Electronic Health Record (EHR) Data is Not a Perfect Reflection of the Patient
Problem: EHR data suffers from incompleteness, as not all possible observations are collected for all patients at all times. The data that is collected is highly dependent on clinical decisions and hospital procedures, which can introduce bias [36] [37].
Solution:
- Assess Data Fitness: Before model development, carefully consider if the EHR data is fit for your specific prediction goal. Acknowledge that tabular data from routine clinical practice will always have a level of incompleteness [36].
- Understand Clinical Context: Collaborate with clinicians to understand why data was collected. A missing lab test value could be because it was not clinically indicated, which is informative in itself [37].
- Document Data Lineage: Use tools or processes to track the flow of data from its source in the EHR to its destination in your model. This helps quickly identify the origin of data quality issues [35].
Issue: Sampling Bias in Collected Data
Problem: The collected data does not accurately represent the entire target population, leading to flawed conclusions.
Solution:
- Define Your Target Population: Conduct thorough research to understand the characteristics and subgroups of your target population [4].
- Choose an Appropriate Sampling Method: Anticipate and address potential biases by selecting a sampling method that allows for a representative sample of the entire population, not just an easily accessible segment [35] [4].
- Minimize Bias Proactively: Use methodological techniques to reduce systematic errors. This ensures the insights you gather are a true representation of the entire group you're studying [35].
Data Collection Methods at a Glance
The table below summarizes the core data collection methods, helping you choose the right approach for your regulatory research.
Table 1: Comparison of Primary Data Collection Methods
| Method | Primary Data Type | Key Strengths | Common Challenges | Best Use Cases in Regulatory Research |
|---|---|---|---|---|
| Surveys & Questionnaires [4] [39] | Quantitative & Qualitative | Reaches many participants quickly and cost-effectively; Structured analysis [4]. | Response bias; May not capture complex nuances [4]. | Collecting patient-reported outcomes (PROs), healthcare professional opinions on a new therapy. |
| EHR Data Extraction [36] [37] | Quantitative (Structured Data) | Provides detailed, longitudinal real-world patient data from clinical settings [37]. | Data incompleteness; Artifacts from extraction; Requires extensive cleaning [36] [37]. | Real-world evidence (RWE) generation; Pharmacovigilance; Dynamic prediction modeling for disease risk. |
| Clinical Observations [4] [38] | Qualitative & Quantitative | Captures authentic behavior and contextual information in a natural setting [4] [38]. | Observer bias; The Hawthorne Effect; Time-consuming [4] [38]. | Studying clinical workflow adherence; Understanding user interaction with a medical device in a hospital. |
| Sensor Data Collection [39] | Quantitative | Continuous, automated data; Eliminates manual recording errors; Real-time insights [39]. | High data volume and complexity; Requires robust data pipelines [39]. | Remote Patient Monitoring (RPM); Clinical trial endpoint capture (e.g., activity levels); IoT device performance. |
The Scientist's Toolkit: Essential Research Reagents & Solutions
Table 2: Key Tools and Platforms for Data Collection
| Item | Function | Example Tools & Standards |
|---|---|---|
| Electronic Data Capture (EDC) System | Securely captures and manages clinical trial data collected from participants at investigative sites. | RedCap, SurveyCTO [4] |
| EHR Data Standard | Facilitates structure and terminology consistency for extracted health data, enabling reproducible research. | OMOP Common Data Model (CDM) [36] [37] |
| Streaming Data Platform | Enables real-time ingestion and processing of high-volume data from sensors and other continuous sources. | Apache Kafka [39] |
| Data Integration & API Tool | Connects different software systems to automatically exchange and synchronize data between platforms in real-time. | GraphQL, REST APIs [39] |
| Statistical Software Package | Provides the environment for data preparation, statistical analysis, and predictive model building. | R (tidyverse, tidymodels), Python (pandas, scikit-learn) [37] |
Experimental Workflow for Data Collection
The following diagram outlines a robust, iterative workflow for data collection in regulatory research, from planning to implementation, emphasizing quality and compliance.
Sampling Strategies to Ensure Representative and Unbiased Data
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between probability and non-probability sampling?
- A: Probability sampling is a method where every member of the target population has a known and equal chance of being selected. This method is crucial for producing unbiased, representative samples and is primarily used in quantitative research to ensure generalizability [40] [41] [42]. In contrast, non-probability sampling involves selecting participants in a non-random way, where not everyone has an equal chance of selection. It is often used in qualitative research, exploratory studies, or when researching hard-to-reach populations [40] [41] [43].
Q2: My resources are limited. Can I use a convenience sample for my preliminary research?
- A: Convenience sampling, which involves selecting readily available participants, can be a quick and cost-effective method for exploratory research or pilot studies [41] [43]. However, you must be cautious. This method is highly susceptible to selection bias and may not represent the broader population, thus limiting the generalizability of your findings [41] [42]. Its use in a regulatory context would require strong justification, and it is generally not suitable for definitive design validation studies [44].
Q3: How does my research goal influence the choice of sampling technique?
- A: The research goal is a primary determinant for selecting a sampling method.
- If the goal is to generalize findings to a larger population (e.g., in a clinical trial or a survey), a probability-based method like simple random, stratified, or cluster sampling is necessary [45] [46].
- If the goal is exploratory research or to gain deep, qualitative insights into a specific phenomenon, non-probability methods like purposive or theoretical sampling are more appropriate [40] [47] [43].
- For studying hard-to-reach or hidden populations (e.g., specific patient support groups), snowball sampling is often the most practical technique [41] [42] [46].
Q4: What is data saturation in qualitative research and how does it relate to sample size?
- A: Data saturation is the guiding principle for determining sample size in qualitative research. It is the point at which collecting new data no longer yields new analytical information or insights but instead becomes redundant [47]. Sample size is not predetermined by a statistical formula but emerges during the study. The researcher continues to collect data—through interviews or observations—until saturation is achieved, ensuring the findings are rich and comprehensive [47] [43].
Troubleshooting Guides
Issue 1: Sampling Bias in Data Collection
Problem: The collected data does not accurately represent the target population, leading to skewed results and incorrect conclusions. A classic example is the 1948 U.S. presidential election telephone survey, which disproportionately sampled wealthy individuals and led to an incorrect prediction [41].
Solution:
- Use Probability Sampling: Employ methods like simple random or stratified sampling to ensure every population member has a known chance of selection, thereby minimizing selection bias [45] [48].
- Ensure a Robust Sampling Frame: Work from a complete and accurate list of all individuals in your target population. An incomplete frame automatically introduces bias [45] [46].
- Minimize Non-Response Bias: Actively encourage participation from all selected members. If certain groups are consistently non-responsive, their perspectives will be missing from your data [45].
- Justify Non-Probability Methods: If using non-probability sampling is unavoidable, transparently document the rationale and acknowledge the potential limitations on generalizability in your research report [44] [43].
Issue 2: Determining a Statistically Justified Sample Size
Problem: A sample size that is too small may lack the power to detect a meaningful effect, while an overly large sample wastes resources. Regulatory bodies like the FDA require a written statistical rationale for the sample size used [44] [49].
Solution:
- For Quantitative Studies: Use established statistical formulas that incorporate key parameters. For a simple random sample, the required size can be calculated as [45]:
n = (Z² * p * (1 - p)) / E²Where:n= required sample sizeZ= Z-value for your desired confidence level (e.g., 1.96 for 95%)p= estimated proportion in the population (use 0.5 for maximum variability)E= acceptable margin of error (e.g., 0.05 for ±5%)
- Link to Risk Assessment: For design verification and validation in regulatory research, align your sample size with your risk management file. Higher-risk scenarios typically demand higher confidence levels and reliability, which in turn require larger sample sizes [44].
- For Qualitative Studies: Plan to collect data until you reach data saturation, where no new themes or information emerge from additional interviews or observations [47].
Issue 3: Choosing Between Different Probability Sampling Methods
Problem: Uncertainty about which probability sampling method is most appropriate for a specific study context.
Solution: Refer to the following decision workflow to guide your selection:
Experimental Protocols & Methodologies
Protocol 1: Implementing a Stratified Random Sample
Objective: To obtain a sample that accurately represents key subgroups (strata) within a population.
Materials: A defined sampling frame (complete list of the population), data on the stratifying variable(s) for all units in the frame, random number generator.
Procedure:
- Define Strata: Identify the key characteristics (e.g., age groups, disease severity, clinical sites) that are critical to your research question. These will form your strata [42] [45].
- Divide the Population: Separate every unit in your sampling frame into the predefined strata [46].
- Determine Allocation: Decide on the number of units to select from each stratum. This can be:
- Random Selection: Within each stratum, use a simple random sampling method (e.g., computer-generated random numbers) to select the predetermined number of units [42] [48].
- Combine: Combine the selected units from all strata to form your final research sample.
Protocol 2: Implementing a Purposive Sample for a Qualitative Study
Objective: To intentionally select individuals or cases that are information-rich due to their specific knowledge or experience with the phenomenon of interest [47] [43].
Materials: Predefined inclusion criteria based on research objectives, a method for identifying and accessing potential participants.
Procedure:
- Define Criteria: Clearly articulate the specific experiences, characteristics, or knowledge that a participant must possess to be included in the study [43].
- Identify Potential Participants: Use your network, institutional records, or preliminary surveys to locate individuals who meet the criteria [47].
- Select Participants: Use your judgment to choose participants who best fit the criteria and are likely to provide rich, relevant data. This may involve seeking maximum variation in experiences or focusing on typical cases [47].
- Document Rationale: Keep a clear record of why each participant was selected, linking them to the research question and inclusion criteria. This transparency is crucial for the study's credibility [43].
- Iterate if Necessary: In approaches like grounded theory, the sampling continues iteratively alongside data analysis (theoretical sampling), where new participants are selected to help develop emerging theoretical concepts [47] [43].
Data Presentation: Sampling Plan Tables
The U.S. Food and Drug Administration (FDA) provides sampling tables for inspections, which illustrate the relationship between sample size, confidence level, and the maximum number of allowable defects. These principles can be adapted for quality review in research.
Table 1: Sampling Plan for 95% Confidence Level (Adapted from FDA Guidance) [49]
| Plan | Maximum Allowable Defect Rate | Sample Size for 0 Defects | Sample Size for 1 Defect | Sample Size for 2 Defects |
|---|---|---|---|---|
| A | 30% | 11 | 17 | 22 |
| B | 25% | 13 | 20 | 27 |
| C | 20% | 17 | 26 | 34 |
| D | 15% | 23 | 35 | 46 |
| E | 10% | 35 | 52 | 72 |
| F | 5% | 72 | 115 | 157 |
Table 2: Sampling Plan for 99% Confidence Level (Adapted from FDA Guidance) [49]
| Plan | Maximum Allowable Defect Rate | Sample Size for 0 Defects | Sample Size for 1 Defect | Sample Size for 2 Defects |
|---|---|---|---|---|
| A | 30% | 15 | 22 | 27 |
| B | 25% | 19 | 27 | 34 |
| C | 20% | 24 | 34 | 43 |
| D | 15% | 35 | 47 | 59 |
| E | 10% | 51 | 73 | 90 |
| F | 5% | 107 | 161 | 190 |
Table 3: Recommended Qualitative Sample Size Estimates by Methodology [47]
| Qualitative Methodology | Typical Data Collection Estimate | Key Determinant of Final Size |
|---|---|---|
| Ethnography | 25-50 interviews & observations | Data Saturation |
| Phenomenology | Fewer than 10 interviews | Data Saturation |
| Grounded Theory | 20-30 interviews | Data Saturation & Theoretical Saturation |
| Content Analysis | 15-20 interviews or 3-4 focus groups | Data Saturation |
The Scientist's Toolkit: Research Reagent Solutions
Table 4: Essential Tools for Sampling and Sample Size Determination
| Tool / Resource | Function in Research | Example / Note |
|---|---|---|
| Random Number Generator | Selects participants without bias for simple random and systematic sampling. | Use computer-based algorithms (e.g., in R, SPSS) for true randomness; avoid manual methods. |
| Sampling Frame | A complete list of all units in the target population from which a sample is drawn. | A patient registry, a list of all manufacturing lots, a university's student directory [45] [46]. |
| Sample Size Calculator | Software or formulas to determine the minimum number of participants needed. | G*Power, R, or online calculators that use inputs like effect size, power, and alpha [45]. |
| Statistical Software (e.g., R, SPSS) | Performs complex sample size calculations and analyzes data from complex sampling designs. | Essential for calculating power for advanced designs and for analyzing stratified or cluster sample data. |
| Confidence & Reliability Table | Provides a statistically valid sample size for verification/validation studies, often with zero-failure plans. | FDA sampling tables are a key example; used extensively in medical device and manufacturing research [44] [49]. |
This technical support center provides practical guidance for researchers, scientists, and drug development professionals navigating data ethics within regulatory frameworks. The following FAQs and troubleshooting guides address implementation challenges for the 5Cs of Data Ethics—Consent, Collection, Control, Confidentiality, and Compliance—to ensure your research meets ethical standards while advancing scientific discovery [50].
Frequently Asked Questions (FAQs)
1. What constitutes valid informed consent for retrospective data use in regulatory research? Valid informed consent requires clarity about data usage purposes. For retrospective studies using existing datasets, consent is valid if individuals were initially informed that their data could be used for future research and provided voluntary agreement. If the new research purpose differs significantly, re-consent may be necessary unless the data is fully anonymized and ethics board approval is obtained [51] [52].
2. How can we ensure data collection practices are ethically sound? Apply the principle of data minimization: collect only what is strictly necessary for your specific research purpose [50]. Implement transparent protocols explaining what data is collected and why [53]. Secure data through encryption and access controls from the point of collection, and conduct regular audits to maintain standards [54] [50].
3. What technical methods effectively give subjects control over their data? Implement technical systems that allow data subjects to access, review, correct, and request deletion of their information [50]. Create granular privacy preferences rather than all-or-nothing choices, and establish automated workflows to process deletion requests across all data stores while maintaining comprehensive audit trails [51].
4. How do we maintain confidentiality when sharing data with regulators? Use robust de-identification techniques that minimize re-identification risk [55]. Apply differential privacy or synthetic data generation for analysis, and establish clear data sharing agreements that define usage boundaries. Implement strong encryption for data in transit and at rest, particularly for sensitive information like genetic data [56] [54].
5. What are the key compliance requirements across different regulatory jurisdictions? Map requirements across all applicable regulations (e.g., GDPR, HIPAA). Maintain detailed documentation of data provenance and processing activities. Implement privacy by design throughout your research lifecycle, and conduct regular compliance audits with particular attention to international data transfer regulations [55] [50].
Troubleshooting Guides
Issue: Obtaining Meaningful Consent in Complex Studies
Problem: Research participants agree to terms without understanding the implications of complex data usage, especially in longitudinal studies or when data may be repurposed.
Solution:
- Implement tiered consent forms with clear, plain-language summaries
- Develop dynamic consent platforms that allow participants to update preferences
- Use interactive explanations and visual aids to illustrate data flows
- Establish ongoing communication protocols to inform participants of new uses
Preventive Measures:
- Adopt a "golden rule" standard: treat others' data as you would want your own treated [51]
- Design consent processes for specific contexts rather than one-time agreements
- Test consent forms with non-expert focus groups before deployment
Issue: Managing Data Subject Access Requests (DSARs)
Problem: Researchers struggle to efficiently respond to participant requests to access, correct, or delete their data across complex research datasets.
Solution:
- Create a centralized DSAR management system with clear workflows
- Implement data provenance tracking to identify all instances of personal data
- Develop automated data discovery tools to locate personal information across systems
- Establish verification protocols to authenticate requestor identity
Preventive Measures:
- Design data architectures with built-in subject rights capabilities
- Maintain comprehensive data maps cataloging all personal data locations
- Implement data retention policies with automatic expiration dates
- Train research staff on DSAR procedures and response timelines
Issue: Ethical Data Collection from Vulnerable Populations
Problem: Collecting data from vulnerable groups (patients, children, marginalized communities) requires special ethical considerations beyond standard protocols.
Solution:
- Implement additional safeguards specific to the vulnerable population
- Use legacy contact protocols for research involving participants who may lose capacity
- Apply additional anonymization techniques for sensitive data
- Establish community advisory boards for research affecting specific populations
Preventive Measures:
- Follow established ethical guidelines such as the American Statistical Association's principles to avoid exploiting vulnerable populations [57]
- Conduct ethical impact assessments before study design finalization
- Ensure fair benefit-sharing so vulnerable populations benefit from research outcomes [52]
- Implement ongoing ethics reviews throughout the research lifecycle
Data Ethics Implementation Framework
Regulatory Alignment Table
| Ethical Principle | FDA/EMA Requirements | GDPR Requirements | Technical Implementation |
|---|---|---|---|
| Consent | Informed consent for clinical trials (21 CFR 50) | Freely given, specific, informed, unambiguous | Electronic consent systems with versioning and audit trails |
| Collection | ALCOA principles for data integrity | Data minimization, purpose limitation | Automated data classification and tagging at point of collection |
| Control | Subject access to clinical data | Rights to access, rectification, erasure | API-based subject portal with identity verification |
| Confidentiality | Protection of subject privacy (21 CFR 11) | Appropriate security safeguards | End-to-end encryption, access controls, audit logs |
| Compliance | GCP compliance, electronic records | Documentation of processing activities | Automated compliance reporting, data protection impact assessments |
Data Ethics Audit Checklist
| Area | Assessment Questions | Compliance Verification |
|---|---|---|
| Consent | Are consent forms written in understandable language? | Test readability scores (<8th grade level) |
| Can participants withdraw consent easily? | Verify opt-out mechanisms function correctly | |
| Collection | Is only necessary data being collected? | Review data inventory against research protocol |
| Are collection methods transparent? | Verify privacy notices accuracy | |
| Control | Can subjects access their data? | Test subject access request process |
| Are data correction mechanisms effective? | Verify data rectification procedures | |
| Confidentiality | Is personal data properly encrypted? | Conduct penetration testing |
| Are access controls appropriately configured? | Review access logs and permissions | |
| Compliance | Are data processing activities documented? | Verify data mapping completeness |
| Are international data transfers compliant? | Review transfer mechanisms adequacy |
The Scientist's Toolkit: Research Reagent Solutions
| Tool/Resource | Function in Data Ethics Implementation | Application Context |
|---|---|---|
| Electronic Data Capture (EDC) Systems | Secure data collection with audit trails | Clinical trial data management |
| Data Anonymization Tools | Remove identifying information while preserving data utility | Secondary use of clinical data |
| Differential Privacy Platforms | Provide mathematical privacy guarantees | Sharing research datasets |
| Consent Management Platforms | Manage participant consent preferences and updates | Longitudinal studies and biobanks |
| Data Provenance Tracking Systems | Document data lineage and transformations | Regulatory submissions and audits |
| Automated Compliance Checkers | Validate data processing against regulations | Multi-jurisdictional research studies |
Experimental Protocols for Ethical Data Practices
Protocol 1: Ethical Data Collection for Clinical Research
Purpose: To establish standardized procedures for ethically collecting clinical research data that respects participant rights and regulatory requirements.
Methodology:
- Pre-Collection Assessment
- Conduct data protection impact assessment
- Define minimum necessary data elements for research objectives
- Document legal basis for data processing
Participant Engagement
- Present layered consent information (short summary + detailed form)
- Provide clear opt-in mechanisms for different data uses
- Establish ongoing communication plan for study updates
Data Collection Implementation
- Implement privacy-preserving data collection techniques
- Apply pseudonymization at point of collection
- Secure data transmission using encryption
Quality Assurance
- Regular audit of collection practices against protocol
- Participant feedback mechanisms on consent process
- Documentation of all collection activities
Protocol 2: Data Subject Rights Management
Purpose: To systematically handle data subject requests while maintaining research integrity and regulatory compliance.
Methodology:
- Request Intake & Verification
- Establish secure channels for request submission
- Implement identity verification protocols
- Log all requests with timestamps
Data Location & Assessment
- Query data inventory systems for relevant personal data
- Assess legal basis for processing and potential exemptions
- Evaluate impact of request on research integrity
Request Fulfillment
- Provide data in accessible format for access requests
- Implement corrections across all data instances
- Remove data from active processing for deletion requests
Documentation & Compliance
- Record all actions taken in response to requests
- Maintain evidence of compliance
- Analyze request patterns to improve processes
Workflow Diagrams
Data Ethics Implementation Workflow
Data Subject Request Handling Process
Technical Support Center: Troubleshooting Guides and FAQs
This technical support center is designed for researchers and drug development professionals navigating the complex landscape of modern data capture. Within regulatory frameworks, ensuring data integrity, security, and compliance from the point of collection is paramount for regulatory acceptance [24]. The following guides address common technical challenges in securing, managing, and leveraging data from diverse sources, including real-world settings.
Frequently Asked Questions (FAQs)
Q1: We are planning a decentralized clinical trial (DCT). How can we ensure data integrity and patient safety when collecting data remotely?
- Challenge: Maintaining data quality and ensuring patient safety in remote settings without compromising trial integrity is a top concern [58].
- Solution: Implement advanced remote monitoring systems that use AI and digital devices for real-time data collection and analysis [58]. Establish clear, pre-defined protocols for virtual patient assessments and emergency responses.
- Troubleshooting Tip: If you encounter data variance or suspect non-compliance in remote data streams, leverage regulatory technology (RegTech) for automated compliance monitoring. These systems provide real-time oversight to help identify and mitigate risks promptly [58].
Q2: Our research involves synthesizing data from multiple real-world sources (e.g., EHRs, claims data). The results are heterogeneous and difficult to pool. What are the best practices?
- Challenge: Real-world data (RWD) from sources like electronic health records and claims data is often heterogeneous, collected with different terminologies, formats, and levels of quality [55].
- Solution: To facilitate data exchange and analysis, adopt a common data model (CDM) that transforms data from multiple sources into a consistent structure, format, and terminology [55]. Implement routine validation processes and quality assurance procedures to benchmark data quality.
- Troubleshooting Tip: If significant variability in results persists after implementing a CDM, conduct a thorough feasibility analysis and document the data source environment in detail. This includes the extent of data collected on clinical outcomes, exposures, and potential confounders [55].
Q3: Is there a way to collect high-quality data in the field where internet connectivity is unreliable or unavailable?
- Challenge: Many field research environments, from remote villages to agricultural sites, lack consistent internet access, making cloud-dependent tools impractical [59].
- Solution: Utilize data collection platforms like SurveyCTO that offer full offline functionality [59]. These allow you to deploy surveys to mobile devices, collect data without a connection, store it locally, and sync it to a central server once internet access is restored.
- Troubleshooting Tip: If data collected offline fails to sync, first check the device's storage capacity. Then, verify that the form definitions on the device are up to date. Most platforms have robust logging to help diagnose sync failures.
Q4: We use an Electronic Data Capture (EDC) system, but mid-study protocol amendments cause significant downtime and disruption. How can this be managed?
- Challenge: Traditional or rigid EDC systems can struggle to accommodate protocol changes without requiring time-consuming migrations and causing system downtime [60].
- Solution: Choose a flexible, cloud-native EDC platform designed to accommodate mid-study changes with zero downtime [60]. Look for systems with drag-and-drop functionality that allow you to modify electronic case report forms (eCRFs) and add new sites or cohorts seamlessly.
- Troubleshooting Tip: Before making amendments, use the EDC's "test" or "sandbox" environment to validate all changes, including edit checks and conditional logic, to ensure they function as intended before deploying to the live study.
Q5: Regulatory agencies require standardized data for submission but do not dictate collection standards. How can we prevent inefficiencies and delays from poor initial data collection? [24]
- Challenge: A lack of industry-wide data collection standards can lead to inefficiencies, with one analysis noting only 20% of studies meeting deadlines, causing significant delays and costs [24].
- Solution: While regulators do not mandate collection standards, sponsors should develop internal standardized data collection protocols. Foster collaboration with external vendors and use standardized data elements and terminologies (e.g., mapping to MedDRA or WHODrug) from the outset of a study [60] [24].
- Troubleshooting Tip: Implement a rigorous data cleaning and organizing process immediately after collection. Identify and rectify errors, inconsistencies, or missing values, and organize data with appropriate codes to ensure its integrity and usability for analysis and regulatory submission [61].
Experimental Protocol: Validating a Mobile and Offline Data Collection Workflow
This protocol outlines the methodology for validating a secure, offline-capable data collection system for use in field research or decentralized trials, ensuring data quality and integrity from the point of capture.
1. Objective: To establish and validate a methodology for collecting high-quality, secure clinical research data using mobile devices in both online and offline environments.
2. Materials and Reagents (The Scientist's Toolkit)
| Tool/Solution | Type | Primary Function |
|---|---|---|
| SurveyCTO [59] | Software Platform | Secure, offline-first mobile data collection with advanced quality controls. |
| TrialKit EDC [60] | Electronic Data Capture System | Cloud-native system to receive, manage, and analyze collected clinical data. |
| Socket Mobile Scanners [62] | Hardware | Barcode and NFC readers for accurate data capture from drug labels and IDs. |
| Common Data Model (CDM) [55] | Methodology | A standardized framework for harmonizing disparate data sources. |
| SOC 2 Certification [59] | Security Framework | Independent audit confirming a platform's security, availability, and confidentiality. |
3. Methodology:
Step 1: System Configuration and Form Design
- Design the data collection form using the platform's form builder (e.g., SurveyCTO's online designer or XLS forms) [59].
- Incorporate automated data quality controls, such as skip logic, constraint checks on values, and required question settings.
- Configure the form for offline use and deploy it to mobile devices (smartphones or tablets).
Step 2: Offline Data Collection Simulation
- Place mobile devices in airplane mode or disconnect from all networks to simulate a field environment.
- Have trained data collectors perform mock data entries, including text, photographs, GPS coordinates, and simulated barcode scans [59].
- Conduct multiple test entries to stress-test the local data storage.
Step 3: Data Synchronization and Transfer
Step 4: Data Integrity and Security Verification
- In the EDC system, verify that all test records transferred completely and accurately. Check for data corruption or loss.
- Review the EDC's audit trail to ensure a secure chain of custody for each data point from the mobile device to the central database [60].
- Confirm that data is encrypted in transit and at rest, per platform specifications (e.g., SSL/TLS encryption) [59].
Step 5: Quality Control and Analysis
- Run pre-programmed data quality reports within the EDC to identify any constraint violations or anomalies.
- Export a subset of data to a statistical analysis environment (e.g., R or Stata) using the platform's API or integration features to confirm interoperability [59].
4. Diagram: Secure Mobile Data Capture Workflow
The diagram below illustrates the logical flow and security checkpoints for the validated mobile data capture process.
Establishing Data Governance Standards for Cross-Functional Collaboration
Frequently Asked Questions (FAQs)
FAQ 1: Why is cross-functional collaboration so challenging from a data perspective?
Traditional organizational structures in pharmaceutical companies are often hierarchical and siloed, which significantly impedes the flow of information and collaboration [63]. These departmental isolations lead to duplicated efforts and prevent the effective sharing of insights and data across different teams, resulting in missed opportunities for synergy and increased inefficiencies [63]. Furthermore, data is frequently disorganized and difficult to query, residing in various locations with unique storage practices and naming conventions, making it an untapped asset for research [64].
FAQ 2: Our team uses its own data definitions and reports. Why is this a problem for the wider organization?
When departments operate with their own data definitions and reports, it creates conflicting versions of the truth, a situation often stemming from the emergence of "shadow data teams" [65]. This decentralized approach leads to inconsistent decision-making, as sales, marketing, and finance may all be making strategic decisions based on data that does not align [65]. This not only hampers collaboration but also creates significant compliance risks, as data without proper oversight is more likely to be mishandled or misinterpreted [65].
FAQ 3: What are the primary regulatory risks of poor data governance in clinical research?
Poor data quality and governance can lead to serious compliance issues, resulting in fines, penalties, and legal complications [66]. Key challenges include keeping up with evolving global regulations like GDPR and HIPAA, managing cross-border data transfer restrictions, and ensuring proper participant consent management [67]. Failure to maintain comprehensive data provenance—the complete record of data's origins and processing history—can also jeopardize reproducibility and regulatory approval [64].
FAQ 4: We have vast amounts of data; why can't we get value from it for AI/ML projects?
AI and machine learning have additional, specific data demands [64]. Researchers often need to tap into every available data source, including data that predates AI/ML, but if this data has not been cataloged and archived with AI/ML in mind, preparing it is a major challenge [64]. For accurate models, training data must be normalized, consistent, and free of factors that could lead to bias. The core issue is often that organizations attempt to leverage AI without a clear strategy for the underlying data quality, leading to the "garbage in, garbage out" problem [63].
FAQ 5: What is a data governance framework and why do we need one?
A data governance framework is a structured model that defines how an organization manages its data assets, outlining the rules, roles, processes, and technologies required to ensure data is trustworthy, secure, and aligned with business objectives [68]. It is essential because it translates the philosophy of governance into an operational reality, making data management intentional, sustainable, and fully integrated with business and IT strategies [68]. Without a framework, data can become fragmented, inaccurate, and non-compliant with regulations [68].
Troubleshooting Guides
Guide 1: Resolving Data Silos and Disorganization
Symptoms: Inability to locate or query archived data, data stored in disparate sources with different conventions, difficulty reusing data for new research projects.
Root Cause: Data is often located in various internal and external archives (e.g., internal servers, clinical institutions, partner organizations), each with unique storage practices, naming conventions, and quality checking processes [64].
Methodology:
- Inventory Data Assets: Identify and catalog all critical data domains (e.g., customer, financial, clinical) and how they are used [68].
- Implement a Data Catalog: Use technology to create a centralized inventory of data assets. A data catalog helps make data discoverable and understandable across functions [68].
- Establish Standardized Naming and Labeling Conventions: Create and enforce organization-wide policies for how data is classified, named, and stored to ensure consistency [64].
- Adopt Standardized Data Models: Utilize industry standards like those from CDISC (e.g., SDTM, ADaM) to organize clinical trial data in a standard structure, promoting interoperability [67].
Guide 2: Addressing Poor Data Quality
Symptoms: Inconsistent or incomplete data, manual data entry errors, site-to-site variability in clinical trials, missing data from participant dropouts or device failures.
Root Cause: Human error during manual entry, lack of standardized data collection procedures across sites, complex protocols, and technical issues with data collection platforms [67].
Methodology:
- Implement Electronic Data Capture (EDC) Systems: Digitize the data collection process to reduce reliance on paper forms and minimize errors. EDC systems offer built-in validation checks and real-time data access [67].
- Standardize Data Collection Procedures: Create uniform Standard Operating Procedures (SOPs) and data dictionaries to ensure all teams and trial sites follow the same rules [67].
- Conduct Regular Training: Implement continuous training programs for site staff and data managers to ensure proper understanding of protocols and tools, which can reduce data entry errors by up to 40% [67].
- Perform Automated Data Cleaning: Use scripts and tools to automatically identify and rectify errors, outliers, and missing values. Routine data quality checks should be automated to guarantee prompt issue resolution [69].
Symptoms: Inability to merge data from EHRs, wearables, lab systems, and mobile apps; data format discrepancies; system compatibility issues; overwhelmed by data volume and velocity.
Root Cause: Each data source (EHRs, wearables, LIMS) generates data in its own unique format (HL7 FHIR, JSON, CSV, XML), and not all platforms are designed to communicate with each other via APIs [67]. The sheer volume of data from modern devices can be overwhelming.
Methodology:
- Use Integration Platforms: Employ middleware or data integration platforms (e.g., Informatica Cloud, Mirth Connect) that act as bridges between incompatible systems. These platforms offer API connectors and data transformation engines to convert formats automatically [67].
- Implement a Data Governance Framework for Integration: Define clear data ownership and establish access control rules and audit trails. A Master Data Management (MDM) strategy helps align metadata and participant IDs across systems to ensure consistency and traceability [67].
- Adopt a Cloud-Based Scalable Infrastructure: Utilize cloud computing to facilitate scalable and flexible data storage and processing solutions that can handle petabyte-scale datasets elastically [67] [64].
Table 1: Consequences of Poor Data Quality in Clinical Trials
| Consequence | Quantitative Impact | Source |
|---|---|---|
| Study Timelines | Only 20% of studies meet deadlines, causing significant delays and costs. | [24] |
| Data Issue Resolution | More than 50% of data issues arise from protocol complexity. | [67] |
| Operational Efficiency | Poor data quality increases operational costs and delays trial timelines. | [67] |
| Data Entry Errors | Continuous training can reduce data entry errors by up to 40%. | [67] |
| Data Accuracy | Adoption of Electronic Data Capture (EDC) systems can improve data accuracy by over 30%. | [67] |
Table 2: Key Performance Indicators for Data Governance
| KPI Category | Example Metric | Business Impact | |
|---|---|---|---|
| Data Quality | Number of data errors per 1,000 records; Data issue resolution time. | Ensures accurate trial outcomes, valid statistical analysis, and regulatory compliance. | [68] [67] |
| Process Efficiency | Time to integrate new data sources; Data processing throughput. | Reduces time-to-market for new drugs and lowers operational costs. | [63] [67] |
| Business Impact | Revenue increase from new data-driven products; Cost reduction from automated processes. | Demonstrates the direct return on investment of data governance initiatives. | [65] [66] |
| Compliance & Risk | Audit scores; Number of data privacy breaches. | Minimizes legal risks, fines, and reputational damage. | [68] [66] |
Experimental Protocols & Workflows
Protocol: Implementing a Data Governance Framework
Objective: To establish a structured, cross-functional data governance program that improves data quality, enables collaboration, and ensures regulatory compliance.
Methodology:
Assess the Current State:
- Inventory data assets: Identify critical data domains (e.g., clinical, imaging, genomic) and key applications [68].
- Evaluate existing policies: Document any existing informal or legacy data governance practices [68].
- Assess data quality: Use profiling tools to detect inconsistencies, duplicates, or missing values in critical data [68].
- Identify stakeholders: Determine who uses, owns, and is impacted by data in each domain [68].
Define Scope and Objectives:
- Set business-aligned goals: Examples include improving patient data accuracy, ensuring GDPR/HIPAA compliance, or enabling self-service analytics [68].
- Prioritize data domains: Start with high-impact areas like clinical trial data or customer data [68].
- Define success metrics: Establish KPIs such as reduced data errors, faster issue resolution, or improved audit scores [68].
Establish a Data Governance Structure:
Implement Policies and Technology:
Data Governance Implementation Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Components of a Data Governance Framework
| Component | Function | |
|---|---|---|
| Data Catalog | A centralized inventory of data assets that makes data discoverable and understandable across the organization, breaking down data silos. | [68] |
| Electronic Data Capture (EDC) System | Digitizes the data collection process in clinical trials, reducing manual entry errors and providing built-in validation checks for improved data quality. | [67] |
| Data Integration Platform | Middleware that acts as a bridge between incompatible systems (e.g., EHRs, LIMS, wearables), converting and routing data seamlessly to enable integration. | [67] |
| Data Quality Tools | Software that automates the profiling, cleansing, and monitoring of data to identify and rectify errors, outliers, and inconsistencies. | [68] [69] |
| Business Glossary | Provides standardized definitions for business terms across the organization, ensuring a common language and consistent interpretation of data. | [68] |
Overcoming Common Data Collection Pitfalls and Optimizing for Quality
Data Quality Troubleshooting Guides
Incomplete Data Troubleshooting Guide
Q: How can I resolve issues of incomplete data in clinical trial datasets?
A: Incomplete data, where tables are missing values or entire rows, can interrupt data integration and lead to the deletion of otherwise valuable records [70]. To address this:
- Implement Electronic Data Capture (EDC): Use ePRO and eSurveys to actively involve patients in data reporting, which improves the completeness of patient-centric data [71].
- Establish Data Validation Rules: Create rule-based verification that checks for missing values in mandatory fields before data submission [70].
- Utilize Automated Monitoring: Deploy tools that provide real-time alerts when data completeness thresholds are breached, allowing for immediate corrective action [72].
Experimental Protocol for Assessing Data Completeness:
- Profile Data Assets: Analyze dataset structure to identify missing values using automated data profiling tools [73].
- Establish Baseline Metrics: Calculate null percentages for critical data elements to set completeness benchmarks [73].
- Implement Completeness Checks: Configure systems to flag records with missing mandatory fields during data collection [70].
- Monitor Continuously: Use dashboards to track completeness metrics against established thresholds throughout the study [73].
Inconsistent Data Troubleshooting Guide
Q: What methodologies address inconsistent data formats and representations across different study sites?
A: Inconsistent data creates discrepancies in representing real-world situations, such as using different formats for the same values (e.g., "Jones Street" vs. "Jones St.") [70]. Resolution strategies include:
- Standardize Data Formats: Develop and enforce standardized templates for data collection, storage, and reporting [74] [75].
- Implement Data Governance: Establish clear policies and standards for data formats, naming conventions, and units of measurement [70] [74].
- Automate Data Transformation: Convert raw data from various sources into a unified format during integration to ensure consistency [70].
Experimental Protocol for Ensuring Data Consistency:
- Define Standard Formats: Document approved formats, abbreviations, and units of measurement for all data elements [74].
- Implement Business Rules: Create machine-readable constraints that enforce consistency (e.g., "shipping dates must always follow order dates") [73].
- Conduct Regular Audits: Schedule periodic reviews to check for inconsistencies across datasets and study sites [75].
- Establish Feedback Loops: Create mechanisms to capture and address consistency issues identified during monitoring [73].
Noisy Data Troubleshooting Guide
Q: How can I identify and correct noisy data (errors, duplicates, outliers) in research data?
A: Noisy data includes inaccuracies, duplicates, and mislabeled data that can reduce the accuracy of analysis and model predictions [70]. Mitigation approaches:
- Data Cleaning Procedures: Implement standardization, deduplication, and outlier detection methods [70].
- Electronic Data Capture Tools: Utilize systems with automatic validations to prevent errors during data entry [71].
- AI-Enhanced Cleaning: Deploy machine learning algorithms to automate data cleaning processes and identify patterns indicative of noise [76].
Experimental Protocol for Reducing Data Noise:
- Conduct Data Profiling: Analyze datasets to identify outliers, inconsistencies, and potential errors [73].
- Implement Deduplication: Use algorithms to identify and merge duplicate records based on key identifiers [70].
- Apply Statistical Methods: Utilize statistical process control techniques to identify values outside expected ranges [77].
- Validate and Verify: Conduct manual spot checks and source data verification to confirm automated findings [75].
Data Quality Framework and Dimensions
The following table summarizes the core dimensions of data quality that serve as metrics for assessment and monitoring in regulatory research:
Table 1: Data Quality Dimensions and Metrics
| Quality Dimension | Definition | Measurement Metric | Target Threshold |
|---|---|---|---|
| Completeness | Ensures enough data is gathered, measured, and available for analysis [74] | Percentage of null/missing values [73] | <2% for critical fields [73] |
| Consistency | Maintaining uniformity across data sets and formats [74] | Rate of format/representation violations [70] | >98% conformity [73] |
| Accuracy | Data points correctly represent real-world values [70] | Error rate compared to verified source [73] | >99% for key data elements |
| Timeliness | Data is up-to-date and accessible when needed [74] | Time between data creation and availability [70] | <24 hours for operational data |
| Validity | Data conforms to specified formats and business rules [70] | Percentage of values outside permitted ranges [70] | <1% invalid records |
Data Quality Monitoring Workflow
The following diagram illustrates the continuous process for monitoring and maintaining data quality throughout the research lifecycle:
Frequently Asked Questions
Q: What are the regulatory consequences of poor data quality in pharmaceutical research? A: Regulatory bodies like the FDA and EMA impose significant penalties for data quality lapses. Examples include FDA application denials for drugs with incomplete clinical trial data [75], import alerts for companies with quality issues [75], and substantial fines - such as the $350 million penalty issued to JPMorgan Chase for providing incomplete trading data [70].
Q: How can we prevent data silos from affecting data quality in multi-site trials? A: Data silos prevent data sharing and cause inconsistency [70]. Prevention strategies include implementing centralized data repositories with standardized access protocols [71], establishing data governance frameworks that define ownership and accountability [74], and using cloud-based platforms that enable real-time data sharing across sites while maintaining security [75].
Q: What role does automation play in maintaining data quality? A: Automation reduces human error, which is a leading cause of data integrity breaches [72]. It enables real-time validation checks [75], automated data cleaning processes [70], and continuous monitoring of data pipelines [72]. Machine learning algorithms can further enhance these processes by identifying patterns indicative of data quality issues [76].
Q: How often should we conduct data quality audits? A: Regular audits should be scheduled periodically and in response to significant process changes [75]. The frequency should be risk-based, with higher-risk data elements (e.g., clinical endpoints, safety data) audited more frequently. Automated systems can provide continuous auditing for critical data elements [72].
Research Reagent Solutions: Data Quality Tools
Table 2: Essential Data Quality Management Tools
| Tool Category | Purpose | Key Functions | Examples |
|---|---|---|---|
| Data Profiling Tools | Analyze existing data structure and content [73] | Identify missing values, outliers, inconsistencies [73] | IBM DataStage, Talend |
| Data Quality Monitoring | Continuous assessment of data health [70] | Real-time alerts, SLA tracking, anomaly detection [70] | Acceldata, FirstEigen DataBuck [75] |
| Data Cleansing Tools | Correct errors and standardize formats [70] | Deduplication, standardization, error correction [70] | OpenRefine, Trifacta |
| Electronic Data Capture | Collect patient-reported outcomes [71] | ePRO, eSurveys, real-time data validation [71] | Climedo, REDCap |
| Data Governance Platforms | Enforce data policies and standards [70] | Data catalogs, lineage tracking, policy management [70] | Collibra, Alation |
Data Quality Assessment Framework
The following diagram shows the relationship between core data quality concepts in a comprehensive monitoring framework:
Technical Support Center: FAQs & Troubleshooting Guides
Frequently Asked Questions (FAQs)
What is a data silo and why is it a problem in regulatory research? A data silo is a collection of data held by one group that is not easily or fully accessible by other groups in the same organization [78]. In regulatory and clinical research, they are problematic because they impede visibility and access to data, increase inefficiency and costs, and hinder effective governance [79]. This can lead to significant delays, with one source noting that only 20% of studies meet deadlines due to such inefficiencies [24].
Table: Core Problems Caused by Data Silos
| Problem Area | Impact on Research & Operations |
|---|---|
| Limited Data View | Prevents a holistic view of data, leading to incomplete analysis and decision-making [79] [78]. |
| Threats to Data Integrity | Leads to inconsistencies, duplication, and inaccuracies in data across different systems [78]. |
| Inefficiency & Wasted Resources | Results in redundant data storage, duplicate efforts, and increased IT costs [79] [78]. |
| Hindered Collaboration | Creates barriers to information sharing and collaboration across departments and agencies [80] [78]. |
| Governance & Compliance Risks | Makes organization-wide data governance impossible, complicating regulatory compliance and security [79] [78]. |
Our organization must comply with strict regulations. How can we share data securely? Data sharing must be done ethically and securely, in accordance with federal and state laws and regulations like FERPA, HIPAA, and the Privacy Act of 1974 [81]. Best practices include implementing a robust data governance framework, using end-to-end encryption, short-lived access credentials, and maintaining clear audit trails [82]. Establishing Data Sharing Agreements is also critical; most clinical trial agencies mandate them to govern data use [2].
What are the key technical approaches to breaking down data silos? Several architectural approaches can be employed, each with its own strengths. The right choice depends on your organization's specific needs and infrastructure [80].
Table: Technical Approaches for Data Integration
| Approach | Key Function | Best Suited For |
|---|---|---|
| Data Lakehouse | Combines the scale/flexibility of data lakes with the governance/performance of data warehouses [79]. | Organizations needing to support BI, SQL analytics, data science, and AI on a single platform [79]. |
| Data Fabric | Uses AI and automation to provide intelligent and seamless data integration and governance across hybrid environments [80]. | Complex, hybrid-cloud environments requiring real-time data integration with high automation [80]. |
| Data Mesh | A decentralized architectural framework that aligns data ownership with business domains [80]. | Large organizations seeking to scale data capabilities by empowering domain-oriented teams [80]. |
| Data Virtualization | Provides a unified, real-time interface to query data across disparate sources without physical replication [80]. | Scenarios requiring real-time access to diverse data sources without the overhead of data movement [80]. |
| Delta Sharing | An open protocol for secure data sharing to any computing platform, based on the Delta data format [82]. | Secure, cross-organizational data exchange, ideal for sharing with external partners or across government agencies [82]. |
We face resistance from internal teams. How can we foster a culture of data sharing? Breaking down data silos requires both technological and organizational change [78]. Key steps include:
- Executive Support: Secure management buy-in to drive a culture change, articulating clear short and long-term benefits [79].
- Change Management: Communicate the benefits of data sharing and the problems with silos, including data quality issues and the need to stay competitive [78].
- Governed Self-Service: Establish robust data access policies that facilitate self-service analysis, so users can easily access the data they need without IT acting as a gatekeeper [78].
Troubleshooting Common Data Sharing Experiments
Experiment 1: Implementing a Cross-Agency Data Sharing Pilot
- Objective: To securely share and analyze clinical trial data across two independent research units.
Detailed Protocol:
- Define Shared Purpose & Governance: Engage stakeholders from both units to establish a shared purpose, define use cases, and assess the risk versus benefit of data sharing [81]. Appoint a joint governance committee.
- Legal & Policy Review: Conduct a review to craft a legal approach that complies with relevant regulations (e.g., HIPAA, FERPA equivalents) [81] [2]. Draft a Data Sharing Agreement outlining permitted uses, security requirements, and data destruction policies [2].
- Map Data Flows: Use experts to develop a visual map of internal data flow and the necessary agreements [83]. This helps understand what data is in your systems, where it resides, and its lineage [83].
- Select Technology & Implement: Choose a sharing technology like Delta Sharing [82] or a Data Lakehouse [79]. Implement strong security controls, including end-to-end encryption and access management.
- Validate & Analyze: Perform a joint analysis on the shared data. Compare results against isolated analyses to identify new insights gained from the integrated data.
Common Issue: "We cannot reconcile data schemas between agencies."
Common Issue: "Our security team is blocking sharing due to privacy concerns."
Data Integration Workflow
Experiment 2: Creating a Federated Data Discovery Portal
- Objective: To build a single portal for researchers to discover and request access to datasets from multiple departmental silos.
Detailed Protocol:
- Inventory Data Assets: Perform a data audit across departments to identify and document available data sources [79].
- Establish Metadata Standards: Define a common metadata schema (e.g., using a data catalog) to ensure all datasets are described consistently.
- Implement a Unity Catalog: Use a unified governance solution like Unity Catalog to seamlessly govern data and AI assets across any cloud or platform. This enables secure discovery and access [79].
- Develop Access Workflows: Design and automate workflows for dataset access requests, approvals, and provisioning based on the data sharing agreements.
- Train Users: Conduct training sessions for researchers on how to use the portal, understand metadata, and submit data access requests.
Common Issue: "Researchers cannot find the datasets they need."
- Solution: Implement a centralized data catalog with powerful search functionality. Ensure all datasets have rich, accurate metadata and clear ownership. Promote Transparency Best Practices to improve communication about available data [83].
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Components for a Modern Data Integration Initiative
| Solution / Component | Function in the Data Ecosystem |
|---|---|
| Data Lakehouse | Serves as the central, unified platform for storing structured, semi-structured, and unstructured data, enabling both analytics and AI [79]. |
| Delta Sharing | Acts as an open protocol for secure data sharing with external partners, preventing vendor and cloud lock-in [82]. |
| Unity Catalog | Provides unified governance for all data and AI assets, enabling secure discovery, access, and collaboration across the organization [79]. |
| ETL/ELT Tools | Automate the process of extracting data from siloed sources, transforming it into a common format, and loading it into the central repository [79] [78]. |
| Data Fabric | Offers an intelligent, automated layer over complex data environments to simplify data management and access [80]. |
Mitigating Bias in Data Collection and Algorithmic Decision-Making
Core Concepts: Understanding Bias in Data and Algorithms
What is the fundamental distinction between data bias and algorithmic bias?
- Data Bias arises from systematic errors in the training data itself. This occurs when the data used to build a model is unrepresentative of the population the model will serve or reflects historical inequalities [84] [85]. Key types include:
- Sampling Bias: The collected data does not accurately represent the target population [84] [86].
- Historical Bias: The data reflects past societal discrimination or inequities, which the model then learns and perpetuates [84].
- Measurement Bias: Inconsistent or flawed data collection methods skew the information [84] [86].
- Algorithmic Bias emerges from the design and operation of the machine learning model itself. This can happen even with relatively good data due to choices made during development [85] [86]. It includes:
Why is bias mitigation a critical concern for AI in drug development and healthcare?
Biased AI systems can directly impact patient safety and healthcare equity. For instance, diagnostic algorithms have shown lower accuracy for darker-skinned individuals in detecting skin cancer, and models trained predominantly on male patient data can struggle to accurately diagnose conditions like pneumonia in female patients [84] [87]. This can lead to misdiagnosis, delayed treatment, and the perpetuation of existing health disparities [87] [88]. Furthermore, regulatory frameworks like the EU AI Act now classify many healthcare AI systems as "high-risk," mandating strict transparency and accountability measures [88] [86].
Bias Detection and Diagnostics
What are the primary quantitative metrics for measuring algorithmic bias?
Fairness can be quantified using several metrics, each with a different philosophical underpinning. It is crucial to use multiple metrics as they can sometimes be in conflict [87] [85].
Table: Key Fairness Metrics for Bias Detection
| Metric Name | Definition | Interpretation | Use Case Example |
|---|---|---|---|
| Demographic Parity [85] [86] | The proportion of positive outcomes is equal across different demographic groups. | An AI system satisfies this if it grants loans at the same rate to different racial groups, regardless of other factors. | Screening for potential disparate impact in initial candidate selection. |
| Equalized Odds [85] [86] | The model has equal true positive rates and equal false positive rates across all groups. | A diagnostic AI is fair if it is equally accurate at correctly identifying a disease and equally prone to false alarms for all patient groups. | Evaluating clinical diagnostic tools where both types of errors are critical. |
| Equal Opportunity [86] | A relaxation of equalized odds focusing only on equal true positive rates across groups. | A hiring tool should be equally good at identifying qualified candidates from every demographic. | Auditing models where correctly identifying the "positive" class is of primary importance. |
How can we detect bias without access to protected attribute data (like race or gender)?
Unsupervised techniques like the Hierarchical Bias-Aware Clustering (HBAC) algorithm can identify groups that experience significantly different model performance without requiring pre-defined demographic labels [89]. This method works by:
- Clustering: Grouping data points based on all available features.
- Bias Variable: Using a performance metric (e.g., error rate, accuracy) as a "bias variable."
- Anomaly Detection: Identifying clusters where the average bias variable is statistically significantly worse than the rest of the dataset [89]. This is particularly useful for discovering unforeseen or intersectional biases where disadvantaged groups are defined by a combination of features rather than a single protected attribute [89].
Experimental Protocol: Conducting a Model Fairness Audit
Objective: To systematically evaluate a trained machine learning model for bias against protected subgroups.
- Define Scope & Attributes: Identify the sensitive attributes (e.g., race, gender, age) and the model's outcome of interest (e.g., loan approval, disease diagnosis) [87] [85].
- Stratify Dataset: Split your validation dataset into subgroups based on the protected attributes.
- Calculate Performance Metrics: Run the model on the entire validation set and on each subgroup individually. Record key metrics like accuracy, true positive rate, false positive rate, and positive predictive value.
- Compute Fairness Metrics: Using the results from step 3, calculate the chosen fairness metrics (see table above) to compare performance across groups [85].
- Statistical Testing: Perform hypothesis tests (e.g., Z-tests, t-tests) to determine if observed performance disparities are statistically significant [89].
- Report & Document: Create a bias audit report detailing the methodology, metrics, and findings, highlighting any significant unfairness [90] [89].
The workflow for a comprehensive bias detection pipeline, from data preparation to reporting, is illustrated below.
Mitigation Strategies and Troubleshooting
What are the main technical strategies for mitigating bias in AI models?
Bias mitigation can be applied at different stages of the machine learning pipeline [85]:
- Pre-processing: These techniques aim to correct the data before it is used to train the model. Methods include reweighting data points from underrepresented groups, generating synthetic data for minority classes, or transforming features to remove correlation with protected attributes [91] [85].
- In-processing: This involves modifying the learning algorithm itself to incorporate fairness constraints during training. An example is adversarial debiasing, where a secondary model tries to predict the protected attribute from the main model's predictions, forcing the main model to learn features that are invariant to the attribute [85].
- Post-processing: After a model is trained, its outputs are adjusted. This may involve applying different classification thresholds to different demographic groups to equalize error rates like false positive rates [85]. This method is often used when you cannot retrain the model but need to deploy a fairer version.
We are concerned our clinical trial recruitment AI may be under-selecting patients from rural areas. What steps should we take?
This is a classic symptom of representation or selection bias. Follow this troubleshooting guide:
- Audit Training Data: Analyze the demographic and geographic composition of your historical clinical trial data used to train the model. Quantify the representation of rural patients [91] [86].
- Diversify Data Sources: Actively source additional data from clinics and hospitals in rural areas to create a more representative dataset [91].
- Apply Bias Mitigation:
- Implement Continuous Monitoring: Set up dashboards to track the selection rates for rural patients in real-time as the model is used, creating a feedback loop to detect concept drift [90] [85].
Our model passed fairness checks pre-deployment but is now showing discriminatory outcomes. What could be the cause?
This typically indicates model drift, which is a key reason why continuous monitoring is essential [90] [86]. The primary causes are:
- Data Drift: The underlying distribution of the input data has changed over time. For example, the demographic makeup of your user base may have shifted in a way not captured in the original training set [90] [86].
- Concept Drift: The relationship between the input variables and the target outcome has changed. For instance, societal definitions of a "good hire" may evolve, making historical training data less relevant [90] [86].
- Mitigation: Establish a robust MLOps pipeline that includes periodic retraining of models on fresh, representative data and continuous tracking of fairness metrics against newly defined subgroups [90] [85] [86].
Regulatory Frameworks and Governance
How do emerging standards like ISO 42001 and IEEE 7003 help address algorithmic bias?
These standards provide a systematic framework for governing AI and managing risks like bias throughout the AI lifecycle [90] [86].
- IEEE 7003-2024: This is a landmark standard that establishes processes to define, measure, and mitigate algorithmic bias. It promotes transparency and accountability by encouraging organizations to create a "bias profile" - a documentation repository that tracks bias considerations from design to decommissioning [90].
- ISO/IEC 42001: This international standard for AI Management Systems (AIMS) integrates bias control directly into organizational governance. Key controls include:
- A.2.1: Requires processes to identify potential algorithmic bias and prevent discriminatory outcomes.
- A.7.4: Mandates data quality requirements that ensure datasets adequately represent relevant demographic groups.
- A.6.2.4: Requires model verification and validation to include tests for bias metrics before deployment [86].
What are the essential components of an organizational governance framework for fair AI?
A robust framework moves beyond technical fixes to encompass people and processes [85] [86]:
- AI Ethics Committee: A cross-functional team with technical, legal, and domain expertise to review AI projects for bias risks [85].
- Clear Policies & Documentation: Written standards that define acceptable levels of bias and mandate procedures like Algorithmic Impact Assessments (AIAs) and AI System Impact Assessments (AIIAs) for high-risk systems [90] [85] [86].
- Diverse Development Teams: Ensuring team composition includes varied backgrounds, perspectives, and expertise to identify blind spots that homogeneous teams might miss [84] [85].
- Stakeholder Engagement: Involving representatives from communities affected by the AI system to provide feedback and help define fairness requirements [91] [85].
Table: Open-Source Tools for Bias Detection and Mitigation
| Tool Name | Primary Function | Key Features | Reference/Link |
|---|---|---|---|
| AI Fairness 360 (AIF360) | Comprehensive bias detection and mitigation | Contains 70+ fairness metrics and 10+ mitigation algorithms; supports multiple stages of the ML pipeline. | [92] |
| Fairlearn | Assessing and improving model fairness | Provides metrics for evaluating unfairness and algorithms for mitigating it, with a user-friendly API. | [92] |
| What-If Tool | Interactive visual investigation of models | Allows users to probe model behavior visually, analyze feature importance, and test for fairness without coding. | [92] [91] |
| Unsupervised Bias Detection Tool | Discovering bias without protected attributes | Uses clustering (HBAC algorithm) to find groups with degraded performance; privacy-friendly (local-only processing). | [89] |
| TensorFlow Fairness Indicators | Fairness metric evaluation at scale | Easily compute commonly-identified fairness metrics for classification models on large datasets. | [92] |
Ensuring Scalability and Managing Real-Time Data Streams from Clinical Trials
Technical Support Center: Troubleshooting Guides and FAQs
This technical support center provides researchers, scientists, and drug development professionals with practical solutions for managing real-time data in clinical trials. The guidance is framed within the broader challenge of collecting robust data for stringent regulatory frameworks.
Troubleshooting Common Real-Time Data Stream Issues
Problem: High Latency in Data Processing Pipeline
- Symptoms: Delays in dashboard updates, stale data in monitoring systems, lag between patient data generation and system availability.
- Potential Causes: Network bottlenecks, undersized stream processing resources, inefficient data serialization.
- Resolution Steps:
- Check Infrastructure Metrics: Monitor CPU/Memory usage of stream processors (e.g., Apache Flink, Spark Streaming). Scale up resources if utilization is consistently above 70% [93].
- Validate Message Broker Health: Check for consumer lag or backlog in your ingestion platform (e.g., Apache Kafka, Amazon Kinesis). Increase partition count or consumer groups if a backlog is present [93].
- Review Data Formats: Consider switching to binary formats (e.g., Apache Avro) for large data payloads to reduce serialization overhead and improve transfer speed.
Problem: Data Inconsistency or Duplication
- Symptoms: Conflicting data points for the same patient or trial event, duplicate records in the data lake or warehouse.
- Potential Causes: Network errors causing message re-delivery, incorrect event idempotency keys, failures in exactly-once processing semantics.
- Resolution Steps:
- Implement Idempotent Writes: Design data sinks (e.g., databases, cloud storage) to ignore duplicate writes using unique keys for each event [93].
- Audit Source Systems: Verify that data sources (e.g., EDC, wearables) are not erroneously re-sending old data.
- Enable Processing Guarantees: If supported, configure your stream processing engine for "exactly-once" processing semantics to prevent duplicates during internal failures.
Problem: Streaming Application Failure or Crash
- Symptoms: Data flow stops completely, monitoring alerts indicate a downed service, error logs show unhandled exceptions.
- Potential Causes: Unexpected data format (schema violation), resource exhaustion (out of memory), dependency failure (e.g., database connection loss).
- Resolution Steps:
- Consult Application Logs: Identify the specific error message and stack trace from the application logs.
- Implement a Dead-Letter Queue (DLQ): Route malformed data events that cause crashes to a DLQ. This allows the main application to continue processing healthy streams while problematic data is quarantined for later analysis [93].
- Restart from Checkpoint: Use the streaming engine's savepoint or checkpoint feature to restart the application from the last consistent state, preventing data loss.
Problem: Poor Data Quality from Source Systems
- Symptoms: Missing values, data format errors, outliers that break downstream analytics.
- Potential Causes: Sensor malfunction, incorrect configuration at the data source, entry errors at clinical sites.
- Resolution Steps:
- Implement Stream-Level Validation: Apply data quality rules (e.g., range checks, null checks, schema validation) within the stream processing layer to filter or flag invalid data [94].
- Establish Data Contracts: Define and enforce formal schemas for data streams using a Schema Registry to prevent incompatible data formats from entering the pipeline [93].
- Create Alerts: Configure real-time alerts for sudden spikes in data quality failure rates, which can indicate a systemic issue with a specific source.
Frequently Asked Questions (FAQs)
Q1: What are the key technology choices for building a real-time clinical data pipeline?
The core architecture typically relies on these technologies [93]:
- Ingestion & Messaging: Apache Kafka, Google Cloud Pub/Sub, or Amazon Kinesis for reliable, high-throughput data collection.
- Stream Processing: Apache Flink, Apache Spark Streaming, or Apache Storm for real-time transformations, aggregations, and analysis.
- Storage: Cloud data warehouses like Google BigQuery, Amazon Redshift, or Snowflake for querying and historical analysis.
- Visualization & BI: Tools like Grafana, Tableau, or Power BI for real-time dashboards and reporting.
Q2: Our trials are global. How do we handle data privacy regulations (like GDPR) with real-time streams?
Real-time data does not negate privacy requirements. Key strategies include:
- Anonymization/Pseudonymization at Source: Remove or tokenize direct identifiers (e.g., name, patient ID) as early as possible in the pipeline, ideally at the source system or during ingestion.
- Federated Learning: This technique allows you to train AI models across multiple decentralized data sources (e.g., different hospital servers) without moving or centrally storing the raw patient data, thus maintaining privacy and compliance [95].
- Strict Access Controls: Implement role-based access control (RBAC) to ensure only authorized personnel can access sensitive data streams and outputs.
Q3: Our legacy systems (e.g., EDC, EHR) weren't designed for real-time streams. How can we integrate them?
Integration with legacy systems is a common challenge [93].
- Use Change Data Capture (CDC): CDC tools can monitor database transaction logs of legacy systems and stream any data changes in real-time to your modern pipeline without impacting the performance of the source system.
- API Abstraction Layers: Build a lightweight API layer that polls the legacy system at high frequency and pushes data to your streaming platform, effectively creating a real-time bridge.
Q4: What are the most critical metrics to monitor for pipeline health?
Continuously track these key performance indicators (KPIs):
- Latency: End-to-end delay from data creation to availability for consumption.
- Throughput: Volume of data (events per second) being successfully processed.
- Error Rate: Percentage of messages failing processing.
- System Resources: CPU, memory, and network usage of all pipeline components.
- Consumer Lag: The delay (in time or messages) for consumers reading from message brokers like Kafka.
Real-Time Data Architecture and Market Context
The following diagram illustrates a standard real-time data architecture for clinical trials, showing the flow from data generation to actionable insights.
Real-Time Clinical Data Architecture
The market for these technologies is experiencing explosive growth, underscoring their strategic importance. The table below summarizes key quantitative data.
Table: Real-Time Data and Analytics Market Size (2024-2030)
| Market Segment | 2024 Market Size | 2030 Projected Market Size | CAGR | Key Drivers |
|---|---|---|---|---|
| Data Integration Market [96] | $15.18 Billion | $30.27 Billion | 12.1% | Digital transformation, cloud adoption, need for real-time insights. |
| Streaming Analytics Market [96] | $23.4 Billion (2023) | $128.4 Billion | 28.3% | IoT proliferation, edge computing, business need for immediate insights. |
| Healthcare Analytics Market [96] | $43.1 Billion (2023) | $167.0 Billion | 21.1% | Demand for personalized medicine, operational efficiency, 30% of world's data generated by healthcare. |
| iPaaS Market [96] | $12.87 Billion | $78.28 Billion | 25.9% | Need to integrate SaaS, on-premises, and partner ecosystems without extensive coding. |
Essential Research Reagent Solutions: The Technical Toolkit
Building and maintaining a robust real-time data pipeline requires a suite of specialized technologies. The following table details the key components.
Table: Essential Toolkit for Real-Time Clinical Data Management
| Tool Category | Example Technologies | Primary Function |
|---|---|---|
| Data Ingestion & Messaging | Apache Kafka, Amazon Kinesis, Google Cloud Pub/Sub | Decouples data producers and consumers; reliably collects and buffers high-velocity data streams from diverse sources [93]. |
| Stream Processing | Apache Flink, Apache Spark Streaming, Apache Storm | Performs real-time computations, transformations, and aggregations on continuous data flows ("data in motion") [93]. |
| Cloud Data Warehousing | Google BigQuery, Amazon Redshift, Snowflake | Stores and enables SQL-based analysis of massive, structured and semi-structured historical and real-time data [93]. |
| Monitoring & Visualization | Grafana, Tableau, Power BI | Creates real-time dashboards and visualizations for operational monitoring, clinical oversight, and business intelligence [93]. |
| AI/ML Platforms | Google AutoML, Amazon SageMaker | Provides tools to build, train, and deploy machine learning models for predictive analytics on the data streams [95] [93]. |
Experimental Protocol for Validating a Real-Time Data Pipeline
Before deploying a pipeline in a live trial, it is crucial to validate its performance and reliability. The following workflow outlines a standard testing protocol.
Pipeline Validation Workflow
Protocol Title: Performance and Resilience Validation of a Real-Time Clinical Data Pipeline
Objective: To verify that the data pipeline meets pre-defined targets for latency, throughput, data integrity, and fault tolerance before use in a clinical trial.
Methodology:
Synthetic Data Load Test:
- Procedure: Generate and inject a high-volume, synthetic dataset that mimics the structure and volume of expected clinical data (e.g., patient vitals from wearables, eCRF data). Gradually increase the load to the pipeline's maximum theoretical capacity.
- Metrics: Measure end-to-end latency and throughput (events/second). The system should maintain stable latency under peak load [93].
Data Integrity and Metric Collection:
- Procedure: Use a synthetic dataset with a known number of unique, traceable events. Run the pipeline for a fixed duration and collect all output.
- Metrics: Compare the input and output counts to confirm zero data loss. Validate that data is not corrupted or duplicated during processing [94].
Failure Injection and Recovery Test:
- Procedure: Deliberately induce failures in the pipeline (e.g., stop a stream processing job, disconnect a database). After a short period, restore the service.
- Metrics: Monitor the pipeline's behavior. After recovery, it should automatically resume processing from the last committed state with no data loss and minimal duplication (achieving at-least-once or ideally exactly-once semantics) [93].
Analysis and Reporting:
- Procedure: Compile all metrics from the previous steps. Analyze the results against the success criteria defined in the trial's data management plan.
- Deliverable: A validation report summarizing findings, confirming the pipeline is "fit for purpose," and ready for regulatory scrutiny.
Addressing Vendor Management and Third-Party Data Risks
Frequently Asked Questions (FAQs)
FAQ 1: What are the most critical third-party risks that can impact regulatory research data?
The most significant risks involve cybersecurity, compliance, and operational stability. Cyber threats are a primary concern, with threat actors increasingly targeting vendor access credentials and APIs using AI-powered techniques [97]. The financial impact is substantial; the average cost of a data breach in the U.S. has surged to a record high, and breaches involving third parties cost an average of $4.66 million [98] [97]. Furthermore, a vast majority of organizations find existing regulations too complex and have difficulty verifying third-party compliance, which can directly compromise the integrity of research data submitted to regulatory bodies [97].
FAQ 2: How can I proactively identify if a vendor poses a compliance risk?
A proactive strategy involves a multi-layered assessment process instead of waiting for an audit or breach. Your due diligence should include:
- Security Ratings: Use external platforms to generate objective, quantifiable scores of a vendor's security posture [98] [99].
- Comprehensive Questionnaires: Send customized security questionnaires that evaluate network security, data protection policies, and access controls [100] [99].
- Evidence Validation: Cross-check vendor claims with independent sources like regulatory databases and threat intelligence platforms. Do not rely solely on a vendor's self-assessment [101].
- Financial and Reputational Checks: Investigate the vendor's financial stability and commitment to ethical business practices to avoid operational disruptions and reputational damage [99].
FAQ 3: Our vendor onboarding process is slow and leads to rushed security checks. How can we improve it?
Lengthy onboarding cycles that pressure teams to cut corners are a common challenge [97]. To streamline the process:
- Standardize Pre-Contract Diligence: Use pre-defined due diligence templates to eliminate redundancies and clearly state risk assessment needs upfront [97].
- Automate Workflows: Implement a centralized vendor portal to automate data collection, simplify document submission, and avoid duplicate requests [97].
- Tier Vendors by Criticality: Classify vendors into risk tiers (e.g., critical, moderate, low) during the initial stage. This allows you to apply appropriate levels of scrutiny and accelerate the onboarding of lower-risk vendors [100] [98].
FAQ 4: What should we do if a vendor we rely on suffers a data breach?
Your response should be guided by a pre-established incident management plan, a key phase in third-party risk management frameworks [100]. Immediately:
- Activate Your Incident Response Plan: Follow the protocols established in your vendor contract, which should include clauses for audit rights and repercussions for non-compliance [100].
- Contain the Impact: Work with the vendor to understand the scope of the breach and isolate affected systems to protect your data.
- Communicate Transparently: Fulfill regulatory obligations by reporting the incident to relevant authorities and, if necessary, affected individuals, as required by laws like GDPR or HIPAA [100] [101].
FAQ 5: What is the difference between a point-in-time assessment and continuous monitoring, and why do we need both?
A point-in-time assessment, like an annual audit or a detailed questionnaire, provides a deep evaluation of a vendor's security posture at a single moment [98]. Continuous monitoring uses tools and platforms to provide real-time updates on vendor risks, such as security ratings and alerts for data leaks [98] [99]. You need both because point-in-time assessments are limited and fail to capture risks that emerge between assessments. Augmenting them with real-time monitoring removes risk exposure blind spots and provides greater awareness of your actual third-party breach potential at any time [98].
Troubleshooting Guides
Problem: Inefficient and slow vendor risk assessment process.
- Symptoms: Assessments take weeks or months to complete; security teams are overwhelmed with manual data entry; difficulty prioritizing which vendors to assess first.
- Solution: Implement a structured, multi-stage vendor risk assessment workflow.
- Identify & Classify: Create a complete inventory of all vendors and classify them by criticality based on their access to sensitive data and systems [99] [101].
- Determine Risk Tolerance: Define the level of risk your organization is willing to accept for each vendor category to guide decision-making [99].
- Gather Evidence Systematically: Use a combination of security ratings, standardized questionnaires, and on-site audits to collect information [99].
- Score and Prioritize: Use a scoring model (e.g., Likelihood x Impact) to quantify risk and prioritize high-risk vendors for immediate action [101].
- Implement Continuous Monitoring: Track vendors for changes in their risk levels, such as data leaks or financial instability [99].
Problem: Lack of visibility into fourth-party risks (our vendor's vendors).
- Symptoms: Being surprised by an incident at a subcontractor; inability to map the full chain of data handling.
- Solution: Extend your due diligence and monitoring to fourth parties.
- Contractual Obligation: Require primary vendors to disclose their critical subcontractors and mandate that those fourth parties adhere to your security standards [100].
- Mapping: Use supply chain mapping tools that work through a "cascading invitation" model to visualize multi-tier relationships and identify risk hotspots [102].
- Verification: Leverage TPRM platforms with automatic fourth-party vendor detection capabilities to analyze your third-party vendors' digital footprints [98].
Problem: Overcoming fragmented risk ownership across different departments.
- Symptoms: Inconsistent assessments between departments; duplicate efforts; critical accountability gaps when a vendor issue arises.
- Solution: Establish a centralized governance model with clear communication channels.
- Centralize Oversight: Adopt a centralized third-party risk dashboard that all relevant departments (procurement, legal, compliance, IT) can access [97] [102].
- Define Clear Ownership: Clearly define which team owns each stage of the vendor lifecycle, from onboarding to performance monitoring and termination [102].
- Adopt a Communication Framework: Implement a framework like the "4 Cs" (Culture, Competence, Control, Communication) to ensure alignment between internal and external stakeholders [102].
Key Data and Statistics
Table 1: Quantitative Overview of Third-Party Risk Challenges
| Metric | Data | Source/Context |
|---|---|---|
| Average cost of a third-party data breach | $4.66 million (USD) | $216,441 higher than the global average for all breaches [98]. |
| Average cost of a data breach in the U.S. | $10.22 million (USD) | A record high for any region as of 2025 [97]. |
| Organizations viewing TPRM as a strategic priority | 64% of leaders | Highlights growing recognition of its importance [102]. |
| Organizations using centralized risk management | 90% | A proven approach to improve accountability and effectiveness [102]. |
| Organizations with fully optimized TPRM automation | 7% | Most companies are still lagging in automating their workflows [102]. |
Experimental Protocols and Workflows
Protocol 1: Vendor Risk Assessment and Scoring Methodology
This protocol provides a detailed methodology for assessing and scoring vendor risk, crucial for maintaining data integrity in regulatory research.
1. Objective: To systematically identify, analyze, and score risks associated with third-party vendors to protect sensitive research data and ensure regulatory compliance.
2. Materials and Reagents:
- Third-Party Risk Management (TPRM) Platform: A software solution for centralizing vendor data, assessments, and monitoring (e.g., platforms from ProcessUnity, UpGuard, Censinet) [97] [101].
- Security Ratings Service: A tool that provides an objective, data-driven numerical score of a vendor's security posture (e.g., UpGuard, BitSight) [98] [99].
- Standardized Security Questionnaires: Customizable templates (aligned with NIST, ISO 27001, or HIPAA) used to gather specific security and compliance information from vendors [100] [99].
- External Risk Intelligence Feeds: Data sources providing information on financial stability, regulatory violations, and geopolitical risks (e.g., Dun & Bradstreet, Moody's) [101].
3. Procedure:
- Step 1: Vendor Identification and Tiering
- Step 2: Evidence Collection
- Step 3: Evidence Validation
- Step 4: Risk Scoring
- Apply a scoring model to quantify risk. A common model is Likelihood x Impact [101]. Score the likelihood of a risk event and its potential impact on your organization on a scale (e.g., 1-10). Multiply these values to generate a risk score.
- Example: A vendor with a likelihood of 6 and an impact of 9 would have a total risk score of 54, signaling a high priority for action [101].
- Step 5: Prioritization and Mitigation
- Prioritize vendors with the highest risk scores for immediate action.
- Develop detailed remediation plans with clear timelines and responsibilities. For lower-risk vendors, routine monitoring may be sufficient [101].
- Step 6: Ongoing Monitoring
Protocol 2: Secure Vendor Onboarding Workflow
This protocol outlines a secure, efficient workflow for integrating new vendors into your research ecosystem.
1. Objective: To establish a standardized process for onboarding new vendors that integrates compliance and security at every step, minimizing business delays and initial risk exposure.
2. Procedure: The following workflow diagram outlines the key stages of the secure vendor onboarding process, from due diligence to integration.
Diagram 1: A workflow for securely onboarding vendors, emphasizing due diligence and continuous monitoring.
- Stage 1: Due Diligence & Risk Assessment
- Activity: Conduct the Vendor Risk Assessment as detailed in Protocol 1.
- Deliverable: A comprehensive risk profile for the prospective vendor, including a security rating and completed questionnaires [98].
- Stage 2: Risk-Based Decision
- Stage 3: Vendor Onboarding
- Activity: Upon approval, formally onboard the vendor. This includes:
- Contracting: Baking compliance requirements directly into the vendor agreement, including clauses for audit rights and clear repercussions for non-compliance [100].
- Defining Attributes: Documenting the vendor lifecycle, roles and responsibilities, compliance requirements, and Service Level Agreements (SLAs) [98].
- Deliverable: A fully executed contract and a completed vendor profile in your centralized inventory.
- Activity: Upon approval, formally onboard the vendor. This includes:
- Stage 4: Integration & Ongoing Monitoring
- Activity: Integrate the vendor into your operations and initiate continuous monitoring as defined in Protocol 1, Step 6.
- Deliverable: An operational vendor relationship with active, ongoing oversight.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools for Managing Third-Party Risk in Research
| Tool Category | Function | Examples / Key Frameworks |
|---|---|---|
| TPRM Platforms | Centralizes all vendor information, automates assessment workflows, and provides a dashboard for monitoring and reporting. | ProcessUnity, UpGuard, Censinet RiskOps, MetricStream [97] [102] [101]. |
| Security Ratings Services | Provides an objective, data-driven numerical score of a vendor's cybersecurity posture for quick benchmarking and comparison. | UpGuard, BitSight [98] [99]. |
| Standardized Frameworks | Provides a roadmap and set of best practices for building a robust TPRM program and ensuring compliance. | NIST Cybersecurity Framework (CSF), ISO 27001, SOC 2, HIPAA [100] [98] [101]. |
| Supply Chain Mapping Tools | Visualizes multi-tier supplier relationships to identify dependencies and hidden fourth-party risks. | Sourcemap [102]. |
| External Risk Intelligence | Provides data on vendor financial stability, regulatory violations, and geopolitical exposure. | Dun & Bradstreet, EcoVadis, Moody's [101]. |
Validating Data and Comparing Frameworks for Automated Compliance
For researchers, scientists, and drug development professionals, high-quality data is not just a best practice—it is a regulatory imperative. In the context of regulatory framework research, flawed data can lead to rejected submissions, compliance failures, and ultimately, delays in delivering critical therapies to patients. Data validation through accuracy, completeness, and consistency checks forms the foundational layer of data integrity, ensuring that collection methods yield reliable, audit-ready evidence. This guide provides actionable troubleshooting and protocols to integrate these principles directly into your research workflow.
Core Principles and Definitions
- Accuracy: The degree to which data correctly represents the real-world values or events it is intended to describe. Inaccurate data in a clinical dataset could misrepresent patient outcomes, leading to incorrect conclusions about a drug's efficacy or safety [103].
- Completeness: The extent to which all required data is present and sufficiently detailed. Missing data in a research dataset can introduce bias and weaken the statistical power of the analysis [103] [104].
- Consistency: The assurance that data is uniform and reliable across different datasets, systems, and time periods. It ensures that data does not contradict itself and is formatted according to defined standards [103].
Troubleshooting Guides
Guide 1: Resolving Data Accuracy Errors
Problem: Suspected inaccuracies in experimental readings or patient data, potentially leading to flawed analysis.
Investigation & Resolution:
- Verify Data Entry Sources: Check for human entry errors, such as typos or transposed numbers, by comparing a sample of the data against original source documents (e.g., lab notebooks, electronic medical records) [103] [105].
- Calibrate Measurement Instruments: Confirm that all lab equipment and sensors are properly calibrated according to manufacturer specifications and standard operating procedures (SOPs). Log calibration dates and results [103].
- Implement Range and Boundary Checks: Enforce automated checks to flag values that fall outside plausible scientific boundaries. For example, a human body temperature reading of 50°C should be immediately flagged for review [104] [106].
- Conduct Cross-Field Validation: Check for logical inconsistencies between related fields. For instance, a patient's "date of death" should not precede their "date of birth" [104].
Guide 2: Addressing Data Completeness Issues
Problem: Missing values in critical datasets, rendering them unsuitable for analysis or regulatory submission.
Investigation & Resolution:
- Audit for Mandatory Fields: Identify all fields defined as mandatory by your study protocol. Run completeness checks to quantify the percentage of non-null values for each [104] [107].
- Analyze Data Pipelines: Trace the data flow from collection to storage to identify points where data could be dropped or lost, such as during system integrations or file format transformations [103].
- Review Data Collection Protocols: Ensure that all personnel are trained on and adhere to standardized data entry protocols. Simplify forms to reduce the likelihood of skipped fields [107].
- Establish Data Handling Rules: Define and document procedures for handling missing data (e.g., imputation, exclusion) in your statistical analysis plan to maintain methodological rigor [107].
Guide 3: Fixing Data Consistency Problems
Problem: Data is formatted differently across systems (e.g., "M/F" vs "Male/Female" for gender), or duplicate records exist, compromising data integrity.
Investigation & Resolution:
- Profile Data Sources: Use data profiling techniques to analyze the actual content, structure, and values within your datasets. This helps uncover hidden patterns and inconsistencies [104] [108].
- Enforce Standardization Rules: Apply consistent formatting rules across all data. For example, standardize date formats to
YYYY-MM-DDand enforce controlled vocabularies for categorical data like specimen types [104] [105]. - Perform Uniqueness Checks: Implement automated checks to detect and merge duplicate records. In a patient registry, this might involve matching on multiple identifiers like name, date of birth, and national ID to avoid double-counting [103] [104].
- Validate Referential Integrity: In relational data systems, ensure that all foreign key relationships are maintained. For example, every lab result in one table should link to a valid patient ID in the master patient table [104].
Frequently Asked Questions (FAQs)
FAQ 1: What is the difference between data accuracy and data integrity?
Answer: While related, they are distinct concepts. Data accuracy refers specifically to the correctness of the data values themselves [103]. Data integrity is a broader concept that encompasses the overall reliability and trustworthiness of data throughout its entire lifecycle, including its accuracy, consistency, and protection from unauthorized alteration [103].
FAQ 2: How can we efficiently validate data in large-scale research studies?
Answer: Manual validation does not scale. The most efficient approach is to use automated data validation tools and frameworks. Tools like Great Expectations, Pandera, or Soda Core allow you to define "expectations" or validation rules (e.g., for schema, values, ranges) that are automatically checked as data flows through your pipelines [109] [108]. This shifts validation left in the process, catching errors early.
FAQ 3: Our team is encountering many human entry errors. How can we reduce them?
Answer: A multi-pronged approach is most effective:
- At the point of entry: Use dropdown menus, radio buttons, and input masks in electronic data capture (EDC) systems to restrict free-text fields [105].
- Through training: Conduct regular, role-specific training on data entry protocols and the critical importance of data quality for research outcomes [107].
- Via culture: Foster a culture of data stewardship where every team member feels accountable for data quality [107].
FAQ 4: Why is data validation particularly critical in regulatory framework research?
Answer: Regulatory submissions, such as to the FDA or EMA, require complete, accurate, and consistent data to demonstrate the safety and efficacy of a new drug or device. Poor data quality can lead to requests for re-analysis, rejection of the submission, and compliance issues, resulting in significant delays and costs [1] [110] [111]. Validation provides the documented evidence of data integrity required for audit trails.
Workflow Visualization
The following diagram illustrates a foundational data validation workflow that integrates the core principles of accuracy, completeness, and consistency checks into a research data pipeline.
Data Validation Workflow
Essential Research Reagent Solutions
The following table details key digital "reagents"—tools and software—essential for building a robust data validation framework in a modern research environment.
| Tool/Software | Primary Function in Validation |
|---|---|
| Great Expectations [109] [108] | An open-source Python framework for defining, documenting, and validating "expectations" on your data, integrated into pipelines. |
| Pandera [109] | A lightweight Python library for statistical data validation of pandas, Dask, and PySpark DataFrames, useful for in-memory checks. |
| Pydantic [109] | A Python library for data validation and settings management using Python type annotations, ideal for validating API inputs and configuration. |
| Data Quality Tools (e.g., Soda, Monte Carlo) [108] | Platforms that provide automated data observability, monitoring, and anomaly detection across data warehouses and lakes. |
| JSON Schema [109] | A vocabulary that allows you to annotate and validate JSON documents to ensure they meet required structure and data types. |
The table below summarizes key quantitative findings related to the impact and prevalence of data quality issues, providing context for the critical need for robust validation.
| Metric | Statistic | Source / Context |
|---|---|---|
| Cost of Poor Data Quality | USD $12.9 million annually | Average loss for businesses (Gartner via [103]) |
| Prevalence of Inaccurate Data | 60% of all business data | Gitnux report (via [104]) |
| Analyst Time Spent on Data Cleaning | Over 30% | McKinsey finding (via [108]) |
| New U.S. State Privacy Laws in 2025 | 8 new laws | Doubling the number of enforceable laws (via [110]) |
Technical Support Center: FAQs & Troubleshooting Guides
Frequently Asked Questions (FAQs)
Q1: What are the most critical features to look for in an Automated Compliance Checking (ACC) platform for pharmaceutical applications? Effective ACC platforms for the pharmaceutical industry should offer real-time monitoring, automated evidence collection, and seamless integration with existing Quality Management Systems (QMS) and Manufacturing Execution Systems (MES) [112] [113]. The platform must support risk-based credibility assessment frameworks, as outlined in the FDA's draft guidance, to ensure the trustworthiness of AI/ML models for their specific context of use [114]. Furthermore, capabilities for automated audit trails and Part 11 / GAMP 5 compliance are non-negotiable for meeting FDA data integrity requirements [112] [115].
Q2: How can we validate an AI model used for compliance checking, such as in pharmacovigilance or process validation? Validating AI models requires a structured, risk-based approach [116]. The FDA recommends a credibility assessment framework that involves defining the model's context of use and providing evidence of its reliability for that specific purpose [114]. Key steps include:
- Comprehensive testing protocols covering data integrity, calculation accuracy, and audit trail completeness [116].
- Ongoing monitoring and periodic revalidation to detect and correct for model performance drift over time [116] [114].
- Documentation that demonstrates compliance with Good Machine Learning Practice (GMLP) and other relevant guidelines [112] [114].
Q3: Our organization struggles with data silos. How can we implement ACC with disparate data sources? This is a common challenge. A phased implementation strategy is recommended [116]. Begin by adopting a cloud-based ACC platform designed to integrate with various systems using APIs and standardized data formats [112] [116]. The core technical step is the creation of a unified ontology or knowledge graph during the "Knowledge Acquisition" phase, which extracts and structures rules from disparate documents and links them to create a single source of truth for compliance rules [117].
Q4: What is the regulatory stance on fully automated decision-making in drug development and pharmacovigilance? Regulatory agencies like the FDA and EMA support automation as a tool to improve consistency and accuracy but emphasize that companies remain ultimately responsible for all automated decisions [116] [114]. They expect human oversight and medical review to be integral parts of the process, especially for complex assessments. The paradigm is one of "human-in-the-loop," where automation handles data processing and initial flagging, but experts make the final critical judgments [116].
Troubleshooting Common ACC Implementation Issues
Issue: Inconsistent or Failed Compliance Checks Against Regulatory Rules
| Symptom | Potential Root Cause | Recommended Troubleshooting Action |
|---|---|---|
| High false-positive rate in automated checks. | Underlying regulatory rules are ambiguous or contain unstated exceptions [118]. | Implement a Verification Language Model (VER-LLM) that uses logical reasoning and hypothesis-testing to navigate rule ambiguities, rather than relying on rigid, binary logic [117]. |
| System fails to identify non-compliant items. | The knowledge base is outdated or does not cover all relevant regulatory amendments. | Activate the ACC system's continuous monitoring feature for regulatory updates. Verify that the knowledge acquisition component has dynamic links between rules and source documents for automatic updates [117]. |
| Compliance checks are slow, impacting development cycles. | Evidence collection is manual and system integrations are incomplete. | Configure and enable automated evidence collection from integrated systems (e.g., LIMS, MES, EHR). Utilize APIs and standardized formats like OSCAL to streamline data sharing [112] [119]. |
Experimental Protocols for ACC Implementation
Protocol 1: Implementing a Continuous Process Verification (CPV) System
Objective: To deploy an automated system for continuous monitoring and validation of a pharmaceutical manufacturing process, aligning with FDA's Process Validation Guidance Stage 3 [112].
Methodology:
- System Integration: Integrate the ACC platform with IoT-enabled process sensors and the Manufacturing Execution System (MES) to enable real-time data streaming [112].
- Define Critical Process Parameters (CPPs): Input validated CPPs and their acceptable ranges into the ACC system's rule engine.
- Configure Alert Workflows: Set up automated alerts and notifications for when process parameters deviate from predefined limits. Assign remediation tasks to relevant personnel [113].
- Enable Automated Reporting: Configure the system to generate real-time dashboards and periodic CPV reports for quality management review [112].
Protocol 2: Validating an AI-based Pharmacovigilance Triage System
Objective: To assess the credibility and performance of a Natural Language Processing (NLP) model designed to triage adverse event reports [116] [114].
Methodology:
- Define Context of Use (COU): Precisely specify the AI model's function—e.g., "to categorize incoming adverse event reports into 'Critical,' 'Serious,' or 'Non-Serious' priority levels based on unstructured narrative text" [114].
- Generate Validation Dataset: Create a ground-truthed dataset of historical adverse event reports, independently classified by human safety experts. To ensure privacy and diversity, leverage synthetic data generation techniques that anonymize real data and create novel variations for comprehensive testing [117].
- Execute Performance Testing: Run the validation dataset through the AI model. Compare the model's output against the expert ground truth to calculate performance metrics (e.g., accuracy, precision, recall, F1-score).
- Document Credibility Evidence: Compile all testing protocols, raw data, results, and a conclusion on the model's suitability for the defined COU into a validation report, as per FDA's credibility assessment framework [114].
Data Presentation
Table 1: Comparison of Leading Compliance Automation Platforms
Data sourced from industry analyses and tool comparisons [120] [113].
| Platform / Tool | Key Strength | Supported Frameworks (Pharma-Relevant) | G2 Rating (5-point scale) |
|---|---|---|---|
| Vanta | Automated evidence collection & real-time monitoring | SOC 2, HIPAA, ISO 27001, PCI DSS | 4.7 [120] |
| Drata | Continuous control monitoring & vendor management | SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS | 4.9 [120] |
| Scrut | Unified compliance management for multiple frameworks | ISO 27001, SOC 2, GDPR, PCI DSS, HIPAA | 4.9 [120] |
| Thoropass | Combines software with access to expert support | SOC 2, ISO 27001, HIPAA, GDPR | Information Missing |
Table 2: Quantified Benefits of Regulatory Compliance Automation
Data synthesized from industry case studies and reports [112] [115].
| Metric | Improvement | Context / Source |
|---|---|---|
| Data Breach Cost Mitigation | ~$1.88M average savings | Organizations with extensive security automation had significantly lower costs [115]. |
| Validation Documentation Effort | 45% reduction | Case study of an Indian sterile injectables manufacturer implementing a Digital Validation Management System (DVMS) [112]. |
| Qualification Time for New Equipment | 40% reduction | Biotech company using a digital twin for line qualification [112]. |
| Pharma Company Digitalization Plans | Over 60% plan full digitization by 2026 | ISPE 2024 survey on validation processes [112]. |
Workflow Visualization
ACC System Architecture
AI Model Credibility Assessment
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Components for an ACC Research Framework
| Item / Solution | Function in ACC Research | Example / Notes |
|---|---|---|
| Digital Validation Platforms (DVPs) | Automates validation lifecycle management, document control, and integrates with lab systems (LIMS) [112]. | ValGenesis, Kneat Gx, Veeva Quality Vault. |
| Synthetic Data Generation | Creates privacy-safe, annotated datasets for training and validating AI/ML compliance models without using sensitive real data [117]. | Utilizes foundation models to create novel, varied data points based on real-data patterns. |
| Open Security Controls Assessment Language (OSCAL) | A machine-readable language for representing compliance control information, enabling automated evidence sharing and audit processes [119]. | Standard format for control catalogs, system security plans, and assessment results. |
| Cloud Controls Matrix (CCM) | A foundational tool for the "Harmonize" action area, providing a standardized set of security controls to map and align various regulatory frameworks [119]. | Maintained by the Cloud Security Alliance (CSA). |
| Verification Language Model (VER-LLM) | A fine-tuned AI model specifically designed for logical reasoning and hypothesis testing in unbounded compliance verification tasks [117]. | Trained on synthetically generated compliance data to navigate rule ambiguity. |
Frequently Asked Questions: Framework Selection & Troubleshooting
Q1: What is the fundamental difference between OWL and SHACL for data validation?
OWL and SHACL serve different primary purposes. OWL (Web Ontology Language) is designed for inference and reasoning under an open-world assumption; it helps discover new knowledge and relationships from existing data [121] [122]. In contrast, SHACL (Shapes Constraint Language) is designed specifically for data validation under a closed-world assumption; it checks data against a set of defined rules to ensure it conforms to expected patterns and structures [121] [122].
For example, an OWL cardinality constraint might be used to infer that an individual belongs to a certain class, while a SHACL constraint will flag a data violation if a required property is missing [121]. For compliance checking where enforcing specific data shapes is critical, SHACL is often the more adept choice [123] [124].
Q2: When should I use the IFC Validation Service, and what are its limits?
The IFC Validation Service from buildingSMART is a free, online platform for validating IFC files against the official IFC schema and specification [125]. You should use it as a first step to ensure an IFC file is syntactically correct and conforms to the standard.
Its key limits are:
- It does not check project-specific rules. It validates the structure of the file, not your specific domain or regulatory content [125].
- File size limit. The online service has a maximum file size limit of 250 MB [125].
- No geometric visualization. It does not perform visual checks; it is a structural and syntactic validator [125].
Q3: We are working on a web-based tool. Why might we choose JSON Schema over more complex semantic web technologies?
JSON Schema is ideal for web-based tools due to its simplicity and native compatibility with JSON, the de facto data interchange format for the web [126] [127]. It provides a straightforward way to validate the structure of JSON data, including constraints on data types, value ranges, and required fields [127]. If your data pipeline already uses JSON and does not require the sophisticated inferencing capabilities of OWL or the complex graph validations of SHACL, JSON Schema offers a lighter-weight and more accessible solution [123].
Q4: During IFC to GIS conversion, we lose semantic information. What is a modern approach to mitigate this?
Data degradation during BIM (IFC) to GIS (e.g., CityJSON) conversion is a known challenge [128]. A modern approach to mitigate semantic loss is to leverage Semantic Web technologies, such as using Linked Data and geometric conversion tools. One study developed an algorithm using this approach, achieving a 95% accuracy rate for converted semantic information by preserving the semantic links between the two environments [128].
Comparative Analysis at a Glance
Table 1: Overview of Validation Framework Capabilities
| Framework | Primary Purpose | Underlying Assumption | Key Strength | Typical Use Case in AEC |
|---|---|---|---|---|
| IFC Validation Service [125] | Syntax & Schema Conformance | Not Applicable | Ensures IFC file is standard-compliant. | Pre-checking IFC files before data exchange. |
| JSON Schema [127] | Structural Validation of JSON | Closed World | Web-friendly, simple to implement. | Validating data from web APIs or in web applications. |
| SHACL [123] [122] | Data Validation & Quality | Closed World | Enforcing complex business rules and data shapes. | Automated compliance checking against regulations [124]. |
| OWL [121] [122] | Knowledge Inference | Open World | Discovering new relationships and facts. | Enriching a building model by inferring new class memberships. |
Table 2: Quantitative Data from Experimental Studies
| Experiment / Approach | Reported Accuracy / Outcome | Key Metric / Constraint Category | Source |
|---|---|---|---|
| IFC to CityJSON Conversion | 95% accuracy | Preservation of semantic information during conversion [128]. | [128] |
| Semantic Compliance Checking | 66% of requirements | Percentage of human-readable requirements automatically validated using Semantic Web tech [124]. | [124] |
| Comparative ACC Analysis | 5 categories | Constraints executed for comparison (e.g., using SHACL, SPARQL, OWL) [123]. | [123] |
Detailed Experimental Protocols
Protocol 1: Automated Compliance Checking (ACC) of Construction Data
This protocol is based on a comparative study that executed five constraint categories from the Flemish building regulation on accessibility [123].
- Requirement Selection & Categorization: Select a set of regulatory requirements. Categorize them into different types (e.g., cardinality, value range, relational constraints).
- Constraint Definition: Define each requirement as a machine-executable constraint in each of the target frameworks:
- IFC-based: Use software like Solibri Model Checker or define an Information Delivery Specification (IDS) [123].
- JSON Schema: Define the expected structure and data types for a JSON representation of the data [127].
- Linked Data (OWL, SPARQL, SHACL): For OWL, define ontological restrictions. For SPARQL, write queries to find violations. For SHACL, define shapes and constraints [123].
- Data Preparation: Obtain the construction data (e.g., a BIM model in IFC format). Convert the data to the required input format for each framework if necessary (e.g., convert IFC to RDF for SHACL).
- Execution & Validation: Run the validation checks in each framework against the prepared dataset.
- Result Analysis & Comparison: Collect the results from each framework. Compare the outcomes based on criteria such as ease of implementation, expressiveness, and performance.
Protocol 2: Validating an IFC Model for a Research Project
- Acquire the IFC Model: Obtain the IFC model from your BIM authoring software or a research repository.
- Initial IFC Validation:
- Navigate to the buildingSMART IFC Validation Service [125].
- Upload your IFC file (ensure it is under 250 MB).
- Review the generated report. Address any schema errors or warnings about industry practices.
- Project-Specific Rule Checking:
- If the model is valid, proceed to check project-specific rules.
- For geometric or complex relational rules, consider using a dedicated rule-checking tool.
- For semantic or data-quality rules, convert the IFC model to RDF and use a SHACL validator to check against your predefined shapes [124].
- Documentation: Record the results of both the standard and project-specific validations for your research data collection.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools and Resources for Validation Experiments
| Item / Resource | Function / Description | Relevance to Research |
|---|---|---|
| buildingSMART IFC Validator [125] | Free online service to check IFC file conformity against the official schema. | Foundational tool for ensuring input data quality for any IFC-related experiment. |
| SHACL Validator (e.g., PySHACL) | Tool to validate RDF graphs against SHACL shape definitions. | Key for executing closed-world, rule-based validation on semantic data derived from building models [123] [122]. |
| JSON Schema Validator | Library (available in many programming languages) to validate JSON documents against a schema. | Essential for testing and validating data in web-based research applications and APIs [127]. |
| SPARQL Endpoint | A query interface for an RDF database, allowing the execution of SPARQL queries. | Used for both querying knowledge graphs and for constraint validation via ASK/CONSTRUCT queries [123]. |
| Semantic Web Stack | The combination of standards (RDF, OWL, SPARQL, SHACL) for managing linked data. | Provides the technological foundation for advanced data integration, inference, and validation research [128] [124]. |
Workflow and Logical Relationship Diagrams
Framework Selection Logic
Validation Framework Decision Tree
Conducting Regular Audits and Continuous Monitoring for Ongoing Compliance
For researchers, scientists, and drug development professionals, the regulatory landscape is undergoing a significant transformation. Traditional periodic audits are no longer sufficient to manage the velocity of regulatory changes and the complexity of modern data-driven research. A 2025 survey of compliance professionals highlights this challenge, revealing that 44.1% cite keeping up with regulatory changes as a major difficulty [129]. This evolving environment demands a shift from reactive, point-in-time audits to continuous compliance monitoring—an automated, proactive approach that provides real-time insight into regulatory adherence [130] [131].
This technical guide provides practical methodologies and troubleshooting advice for implementing continuous monitoring frameworks specifically within regulatory research contexts, helping ensure data integrity, security, and compliance throughout the research lifecycle.
Core Concepts and Key Differentiators
What is Continuous Compliance Monitoring?
Continuous compliance monitoring is the ongoing process of automatically assessing an organization's adherence to regulatory requirements, security standards, and internal policies. Unlike traditional audits, it provides real-time visibility into compliance posture through automated data collection, immediate analysis, and alerts for identified gaps [130] [131].
Traditional Audits vs. Continuous Monitoring
The table below summarizes the fundamental differences between these two approaches.
| Feature | Traditional Periodic Audits | Continuous Compliance Monitoring |
|---|---|---|
| Frequency | Periodic (e.g., annually) [131] | Ongoing, real-time [130] [131] |
| Primary Approach | Reactive, manual sampling [131] | Proactive, automated scanning [130] |
| Risk Identification | Delayed by months [131] | Immediate detection [130] [131] |
| Resource Intensity | High during audit periods [131] | Steady, automated operation |
| Data Accuracy | Prone to human error [131] | High, due to automation [131] |
| Remediation Speed | Slow, post-audit | Rapid, parallel to detection |
| Audit Readiness | Time-limited | Constant [130] |
Implementation Methodology: A Technical Workflow
The following diagram, "Continuous Compliance Monitoring Workflow," visualizes the operational lifecycle of a continuous monitoring system. This is an idealized logical flow; specific tool implementations may vary.
Prerequisites and Setup
Before implementing the workflow, establish these foundational elements:
- Centralized Compliance Platform: Implement a system that provides a unified view of policies, procedures, controls, and evidence. This is critical for managing complexity and offering real-time dashboards [130].
- Integrated Tooling: Select tools that integrate with your existing research infrastructure (e.g., cloud services, ELN/LIMS, document management systems) to automate evidence collection [130] [131].
- Regulatory Intelligence Feed: Subscribe to services that provide real-time updates on regulatory changes from agencies like the FDA, EMA, and others to keep your framework current [129].
The Researcher's Toolkit: Essential Solutions for Compliance
The table below details key tools and resources essential for establishing an effective continuous compliance program.
| Tool/Resource Category | Primary Function | Key Considerations for Research |
|---|---|---|
| GRC Platform (e.g., Scrut, Hyperproof) | Centralizes risk management, control monitoring, and automates evidence collection across multiple frameworks (e.g., GxP, HIPAA) [130]. | Ensure the platform supports specific clinical or laboratory standards relevant to your work. |
| Regulatory Intelligence Platform | Provides automated tracking and alerts for changes in global regulations [129]. | Look for feeds focused on health authorities (FDA, EMA) and research data protection laws. |
| Automated Reporting Tools | Generates detailed, accurate compliance reports on a scheduled basis, reducing manual errors [130]. | Must be capable of generating audit trails and reports for regulatory submissions. |
| Access Control Management System | Dynamically adjusts user permissions to enforce the principle of least privilege [130]. | Critical for protecting sensitive patient data and intellectual property in collaborative research. |
Troubleshooting Guide: FAQs and Common Challenges
Q1: Our team still relies heavily on manual spreadsheets for tracking. How can we transition without overwhelming the team?
- Challenge: 76.9% of compliance teams still use manual processes, indicating this is a common hurdle [129]. The perceived disruption and learning curve are major barriers.
- Solution: Start with a phased approach. First, automate evidence collection for a single, high-impact framework (e.g., GxP data integrity controls). Use a platform that offers pre-loaded policy templates and control mappings to accelerate setup [130]. Demonstrate quick wins by showing how automation reduces pre-audit scrambling for evidence.
Q2: We had a control failure because integrated application evidence was outdated. How can we prevent this?
- Challenge: A common point of failure in automated systems is stale or expired evidence, leading to false negatives in compliance status.
- Solution: Implement a tool with automated alerting features. Configure the system to notify control owners when evidence is soon to expire or when a scheduled check fails. This transforms the process from manual tracking to proactive notification [131].
Q3: A new regulatory update from the EMA impacts our data collection protocol. How do we rapidly adapt our monitoring?
- Challenge: Keeping pace with regulatory changes is the top challenge for 44.1% of professionals [129]. Manually updating controls is slow and error-prone.
- Solution: Leverage a regulatory intelligence platform that offers real-time alerts on changes from specific bodies [129]. Supplement this with external compliance expertise to help interpret new rules and translate them into updated internal controls and monitoring parameters [130].
Q4: Our external auditor is requesting proof of continuous control monitoring over the last quarter. How do we provide this efficiently?
- Challenge: Traditional audits require massive, last-minute evidence compilation, which is inefficient and stressful.
- Solution: Use the reporting function of your centralized compliance platform. These systems are designed to generate detailed, time-stamped reports on demand, showing control performance, evidence collection history, and remediation activities over any specified period. This demonstrates constant vigilance and simplifies the audit process [130] [131].
Q5: How do we ensure our compliance monitoring itself remains effective and doesn't become a "check-the-box" activity?
- Challenge: Compliance programs can stagnate if not regularly reviewed for effectiveness.
- Solution: Schedule regular internal audits specifically targeting the compliance monitoring system itself. This meta-audit should verify that automated controls are functioning as intended, alerts are being addressed, and the system is adapting to new risks. This reinforces accountability and long-term value [130].
Best Practices for Sustained Success
- Adopt a Centralized Platform: A unified dashboard provides the real-time visibility necessary for proactive management and swift issue resolution [130].
- Supplement with Expert Knowledge: While automation is powerful, human expertise is irreplaceable for fine-tuning strategies, interpreting complex regulations, and navigating bottlenecks [130].
- Conduct Regular Internal Audits: Proactive internal audits are essential for identifying and addressing gaps before they escalate into significant violations [130].
- Foster Cross-Department Collaboration: Ensure streamlined communication and collaboration between research, IT, legal, and compliance teams to eliminate silos and ensure comprehensive coverage [130].
Documenting Collection Methods for Reproducibility and Regulatory Scrutiny
Frequently Asked Questions (FAQs)
Q: Why is there a specific standard for data submission but not for data collection? Regulatory agencies require standardized data submission so they can efficiently review, understand, and compare clinical trial results for safety and efficacy [24]. However, they do not govern how data is collected, as this responsibility falls to pharmaceutical companies to conduct their trials efficiently [24]. This lack of centralized standards for collection can lead to inefficiencies and delays [24].
Q: What are the core principles of Good Documentation Practices (GDP) I should follow? Good Documentation Practices are the foundation of data integrity in regulated research. Data must be ALCOA+: Attributable (who created the data), Legible (easy to read), Contemporaneous (recorded at the time of the activity), Original (the first or source record), and Accurate (error-free) [132]. The "+" extends this to include Complete, Consistent, Enduring, and Available [132].
Q: My experimental results are unexpected. What is the first thing I should do? Before assuming a novel finding, first check your assumptions and repeat the experiment if it is not cost or time prohibitive [133] [134]. You may have made a simple human error, such as an incorrect measurement or an extra wash step [133].
Q: How can a research community help promote integrity in observational studies? A collaborative community can foster integrity through practices like pre-specifying and discussing analysis plans, presenting results for feedback, and conducting mandatory analysis code review before manuscript submission [135]. This creates an integrated "hidden curriculum" of quality [135].
Q: What are the main regulatory barriers to sharing clinical trial data? Data sharing is complicated by a complex mix of technical, legal, and ethical barriers [2]. Key issues include intellectual property rights, data exclusivity practices by sponsors, concerns over participant privacy, and a lack of harmonized global regulations, particularly for multi-country trials [2].
Troubleshooting Guides
Guide 1: Troubleshooting Unexpected Experimental Results
Follow these steps to systematically identify the cause of unexpected outcomes.
Step 1: Check Your Assumptions and Repeat Confirm your hypothesis was testable and your experimental design was sound [134]. Unless prohibitive, simply repeating the experiment can reveal simple mistakes [133].
Step 2: Review Your Methods Meticulously Scrutinize all equipment, reagents, and samples. Ensure equipment is calibrated, reagents are fresh and stored correctly, and samples are labeled accurately [134]. Check that controls are valid and reliable [133].
Step 3: Verify the Result and Your Controls Determine if the result is a true failure or a valid, unexpected finding. Use a positive control to confirm your protocol works. If the positive control also fails, the problem is likely with the protocol itself [133].
Step 4: Isolate and Test Variables Change only one variable at a time [133]. Generate a list of potential culprits (e.g., reagent concentration, incubation time, equipment settings) and test the easiest or most likely one first [133].
Step 5: Document the Entire Process Keep a detailed and organized record of every troubleshooting step, change made, and the corresponding result [133] [134]. This is crucial for tracking progress and communicating your work.
Step 6: Seek Help from Colleagues and Experts If you cannot resolve the issue, seek a fresh perspective from your supervisor, colleagues, or external experts who can offer different insights and suggestions [134].
Guide 2: Troubleshooting Data Collection for Regulatory Compliance
Use this guide to address common data integrity and documentation challenges.
- Challenge: Inconsistent data collection across sites or timepoints.
- Solution: Develop and implement standardized data collection forms and Standard Operating Procedures (SOPs) across the entire study. Collaborate with all stakeholders, including external vendors, to agree on these standards [24].
- Challenge: Poor documentation practices risking data integrity.
- Challenge: Inadequate audit trails for data changes.
- Solution: Ensure your electronic system captures a secure, computer-generated audit trail that tracks who made changes to data, when, and why [132]. This is non-negotiable for regulatory inspections.
- Challenge: Uncertain how to pre-specify analysis to avoid scrutiny.
- Solution: Submit a detailed analysis proposal outlining your hypotheses, study design, exposure/outcome definitions, and statistical analysis plan for review by your research community before beginning analysis [135]. This demonstrates rigor and transparency.
Data and Workflow Summaries
Quantitative Data on Drug Development and Color Contrast
Table 1: Key Quantitative Standards for Development and Accessibility
| Category | Metric | Value | Notes / Minimum Standard |
|---|---|---|---|
| Drug Development Attrition [136] | Candidates entering clinical trials that gain approval | 10-15% | Highlights the high-risk nature of research. |
| Clinical Trial Timeline [136] | Average time from discovery to market | 10-15 years | |
| Color Contrast (WCAG AA) [137] [138] | Standard body text | 4.5:1 | Minimum contrast ratio for readability. |
| Large-scale text | 3:1 | For text 120-150% larger than body text. | |
| User interface components | 3:1 | For icons, graphs, and UI elements [137]. |
Research Reagent Solutions
Table 2: Essential Materials for Experimental Research
| Item | Function |
|---|---|
| Primary & Secondary Antibodies | Used in techniques like immunohistochemistry to specifically bind and visualize a target protein [133]. |
| Positive Control Samples | A known source of the target analyte used to verify that an experimental protocol is functioning correctly [133]. |
| Buffer Solutions | Used for rinsing and washing steps to remove unbound reagents, minimizing background signal [133]. |
| Electronic Data Capture (EDC) System | A digital tool that streamlines data collection in clinical trials, reduces transcription errors, and supports real-time data integrity monitoring [132]. |
Experimental Protocols & Workflows
Protocol: Detailed Immunohistochemistry (IHC)
This protocol is used to detect specific proteins in tissue samples for experimental analysis [133].
- Fixation: Preserve the tissue structure.
- Blocking: Apply a solution to minimize non-specific background signal.
- Primary Antibody Labeling: Incubate with an antibody that binds specifically to your protein of interest.
- Washing: Rinse with buffer to remove any excess, unbound primary antibody.
- Secondary Antibody Labeling: Incubate with a fluorescent-tagged antibody that binds to the primary antibody, allowing for visualization.
- Washing: Rinse with buffer to remove any excess, unbound secondary antibody.
- Visualization: Take pictures using an appropriate microscope [133].
Protocol: Systematic Troubleshooting for Failed IHC
This methodology should be followed if the fluorescence signal from the IHC protocol is dimmer than expected [133].
- Repeat the Experiment: Rule out simple human error by repeating the protocol exactly.
- Check Controls: If a known positive control also shows a dim signal, the problem is with the protocol, not the sample.
- Inspect Reagents and Equipment:
- Confirm all reagents have been stored at the correct temperature and have not expired.
- Check that the primary and secondary antibodies are compatible.
- Visually inspect solutions for cloudiness or precipitation.
- Ensure the microscope light source and settings are correct.
- Change Variables One at a Time:
- Generate a list of variables to test (e.g., fixation time, antibody concentration, number of washes).
- Test the easiest variable first (e.g., microscope settings).
- If that fails, test the most likely variable (e.g., concentration of the secondary antibody), trying a range of concentrations in parallel if possible [133].
Workflow: The Life Course of a Research Project for Integrity
This workflow diagram outlines the key stages in a rigorous research project lifecycle designed to promote integrity and reproducibility, based on practices from long-term observational studies [135].
Workflow: Systematic Experimental Troubleshooting
This diagram maps the logical, step-by-step process for diagnosing and resolving issues when an experiment yields unexpected results [133] [134].
Conclusion
Navigating data collection within regulatory frameworks requires a proactive and integrated strategy that blends a deep understanding of the regulatory landscape with rigorous methodology and continuous validation. Success hinges on establishing strong data governance, embedding ethical principles like the 5Cs into every step, and leveraging technology for both collection and automated compliance checking. For biomedical and clinical research, mastering this complex interplay is not merely about compliance—it is a critical enabler for accelerating drug development, ensuring patient safety, and bringing innovative therapies to market. Future efforts must focus on adapting to increasingly automated regulatory processes and developing more agile data practices that can keep pace with scientific and technological advancement.
References
- 1. Ten Key Regulatory Challenges: 2025 Mid-Year Report [https://kpmg.com/us/en/media/news/2025-mid-year-regulatory-report.html]
- 2. Regulatory Frameworks for Clinical Trial Data Sharing [https://pmc.ncbi.nlm.nih.gov/articles/PMC9118011/]
- 3. Mid Year Challenges-What Regulatory Trends To Watch ... [https://complianceandethics.org/mid-year-challenges-what-regulatory-trends-to-watch-for-in-the-second-half-of-2025/]
- 4. A Guide to Data Collection: Methods, Process, and Tools [https://www.surveycto.com/resources/guides/data-collection-methods-guide/]
- 5. Navigating Diverging State Rules: The Case for a Single ... [https://www.sigma360.com/navigating-diverging-state-rules-the-case-for-a-single-source-of-truth/]
- 6. Troubleshooting in pharmaceutical manufacturing processes [https://www.hwi-group.de/en/blog/details/troubleshooting-in-pharmaceutical-manufacturing-processes-root-cause-analysis-of-quality-defects]
- 7. Troubleshooting in Pharma Formulations Services [https://www.vergolabs.com/troubleshooting_pharma_formulations_services/]
- 8. RNAscope Troubleshooting Guide and FAQ [https://acdbio.com/technical-support/solutions]
- 9. Common Problems with GDPR Compliance (& How to ... [https://www.itsasap.com/blog/problems-solutions-gdpr-compliance]
- 10. GDPR Compliance Challenges: Common Issues and ... [https://complydog.com/blog/gdpr-compliance-challenges-common-issues-solutions]
- 11. 7 Most Common HIPAA Compliance Issues [https://compliancy-group.com/7-most-common-hipaa-compliance-issues/]
- 12. The Most Common HIPAA Violations You Must Avoid [https://www.hipaajournal.com/common-hipaa-violations/]
- 13. 8 SOX Pitfalls to Avoid When Preparing for Your First SEC ... [https://www.armanino.com/articles/sox-compliance-challenges-first-sec-audit/]
- 14. 7 Key Compliance Relating to Regulations Storage - SOLIX Blog Data [https://www.solix.com/blog/learning/7-key-compliance-regulations-relating-to-data-storage/]
- 15. Ultimate Guide to Cybersecurity Laws & Policies : GDPR , ISO 27001... [https://www.linkedin.com/pulse/ultimate-guide-cybersecurity-laws-policies-gdpr-iso-27001-malik-8e1af]
- 16. The Complete Guide to AI Maintenance and Support Services [https://www.aalpha.net/blog/ai-maintenance-and-support-services-guide/]
- 17. Data Governance for AI in 2025: Challenges, Best ... [https://www.quinnox.com/blogs/data-governance-for-ai/]
- 18. 10 Data Governance Challenges & How to Address Them ... [https://atlan.com/data-governance-challenges/]
- 19. Why Cloud Data Governance is Critical in 2025 [https://www.alation.com/blog/cloud-data-governance-2025/]
- 20. Regulatory Updates in Clinical Trials: What's New [https://realtime-eclinical.com/2025/01/14/regulatory-updates-in-clinical-trials-whats-new/]
- 21. Data governance in the age of AI [https://kpmg.com/us/en/articles/2025/data-governance-age-ai.html]
- 22. Regulatory challenges associated with conducting multi ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC3900239/]
- 23. Compliance Challenges for Clinical Research Sites [https://www.fdli.org/2025/02/compliance-challenges-for-clinical-research-sites/]
- 24. Regulatory Challenges With Data Collection [https://www.appliedclinicaltrialsonline.com/view/regulatory-challenges-data-collection]
- 25. Regulatory Submission Pitfalls and Ways to Avoid Them [https://www.ipmcinc.com/insights/common-regulatory-submission-pitfalls/]
- 26. Navigating Regulatory Uncertainty: Adapting to FDA ... [https://www.allucent.com/resources/blog/navigating-regulatory-uncertainty-fda-changes-2025]
- 27. Common Causes of Regulatory Submission Rejections [https://www.freyrsolutions.com/blog/common-causes-of-regulatory-submission-rejections-and-how-to-avoid-them]
- 28. Regulatory Submissions with Real-World Evidence ... [https://www.fda.gov/news-events/speeches-fda-officials/regulatory-submissions-real-world-evidence-successes-challenges-and-lessons-learned-09232025]
- 29. HIPAA Questions and Answers Relating to Research [https://www.hopkinsmedicine.org/institutional-review-board/hipaa-research/faq-research]
- 30. Data Minimization: Balancing GDPR & Research Insights [https://www.clinicaltrialvanguard.com/article/data-minimization-balancing-gdpr-research-insights/]
- 31. Unveiling 2025's Biggest Site Challenges: Data-Driven ... [https://acrpnet.org/2025/10/14/unveiling-2025s-biggest-site-challenges-data-driven-insights-to-optimize-site-success]
- 32. Data management in clinical research: An overview - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC3326906/]
- 33. Guidelines for Research Data Integrity (GRDI) [https://www.nature.com/articles/s41597-024-04312-x]
- 34. Best practices for data management and sharing in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11380994/]
- 35. 10 Best Practices for Data Collection in 2025 [https://add-to-calendar-pro.com/articles/best-practices-for-data-collection]
- 36. Challenges and Recommendations for Electronic Health ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12579287/]
- 37. Challenges and recommendations for Electronic Health ... [https://arxiv.org/html/2501.10240v1]
- 38. A Guide to Data Collection Methods: Choosing the Right ... [https://www.ref-n-write.com/blog/a-guide-to-data-collection-methods-choosing-the-right-approach/]
- 39. 10 Interesting Data Collection Techniques & Methods For ... [https://airbyte.com/data-engineering-resources/data-collection-techniques]
- 40. How to choose a sampling technique and determine ... [https://www.sciencedirect.com/science/article/pii/S2772906024005089]
- 41. Sampling Methods for Research: Types, Uses, and Examples [https://dovetail.com/research/sampling-methods/]
- 42. Different Types of Data Sampling Methods and Techniques [https://www.geeksforgeeks.org/data-analysis/different-types-of-data-sampling-methods-and-techniques/]
- 43. Different Types of Sampling Techniques in Qualitative Research [https://sago.com/en/resources/blog/different-types-of-sampling-techniques-in-qualitative-research/]
- 44. [ARTICLE] Sampling Strategy: 10 FAQs on Sample Size ... [https://medidee.com/2022/08/29/sampling-strategy-10-faqs-on-sample-size-selection/]
- 45. Representative Sample | Size, Examples & Key Insights [https://www.checkbox.com/blog/representative-sample]
- 46. Sampling methods in Clinical Research; an Educational ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5325924/]
- 47. Series: Practical guidance to qualitative research. Part 3 [https://pmc.ncbi.nlm.nih.gov/articles/PMC5774281/]
- 48. Design, data analysis and sampling techniques for clinical ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC3271469/]
- 49. Sampling Plans [https://www.fda.gov/inspections-compliance-enforcement-and-criminal-investigations/inspection-guides/sampling-plans]
- 50. Data Ethics: Frameworks, Principles & Challenges (2025) [https://atlan.com/data-ethics-101/]
- 51. The five Cs [https://www.oreilly.com/radar/the-five-cs/]
- 52. The evolution of data ethics in clinical research and drug ... [https://www.sciencedirect.com/science/article/pii/S2352552520300554]
- 53. 5 Principles of Data Ethics for Business - HBS Online [https://online.hbs.edu/blog/post/data-ethics]
- 54. Data Ethics: Safeguarding Privacy and Ensuring ... [https://www.dataversity.net/articles/data-ethics-safeguarding-privacy-and-ensuring-responsible-data-practices/]
- 55. Real‐World Data for Regulatory Decision Making [https://pmc.ncbi.nlm.nih.gov/articles/PMC6617710/]
- 56. Exploring the ethical issues posed by AI and big data ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12581208/]
- 57. Ethical Guidelines for Statistical Practice [https://www.amstat.org/your-career/ethical-guidelines-for-statistical-practice]
- 58. Top 10 Challenges and Solutions for Decentralized ... [https://globalforum.diaglobal.org/issue/march-2025/top-10-challenges-and-solutions-for-decentralized-clinical-trials-technology-diversity-and-regulations-in-2025-and-beyond/]
- 59. SurveyCTO: Secure Data Collection Software [https://www.surveycto.com/]
- 60. Electronic Data Capture (EDC) System for Clinical Trials [https://www.crucialdatasolutions.com/edc/]
- 61. 12 Best Data Collection Tools For Research [https://otio.ai/blog/data-collection-tools]
- 62. Data Capture Solutions for Pharmacy Drug Verification [https://www.socketmobile.com/solutions/healthcare/pharmacy-drug-verification]
- 63. Challenges and opportunities in data for drug discovery [https://www.cas.org/ja/resources/cas-insights/challenges-opportunities-prioritizing-data-drug-discovery]
- 64. 5 common data management problems affecting drug discovery [https://www.drugdiscoverytrends.com/5-common-data-management-problems-affecting-drug-discovery/]
- 65. Passing Through the Trifecta of People, Process, and Tech [https://moderndata101.substack.com/p/the-governance-framework-people-process-tech]
- 66. Regulatory Compliance With Data Governance Strategies [https://kopiustech.com/insights-innovation/navigating-regulatory-compliance-with-data-governance-strategies/]
- 67. Key Challenges in Clinical Trial Data Management [https://ccrps.org/clinical-research-blog/challenges-in-clinical-trial-data-management]
- 68. Data Governance Framework: Key Elements and Examples [https://www.dataversity.net/articles/data-governance-frameworks/]
- 69. Addressing Data Quality Challenges in Drug Discovery [https://www.elucidata.io/blog/the-challenges-of-data-quality-in-drug-discovery-managing-complexity-for-better-innovations]
- 70. Data Quality Issues and Challenges [https://www.ibm.com/think/insights/data-quality-issues]
- 71. Improve Data in Clinical Trials | Climedo Quality [https://climedo.de/en/blog/3-ways-to-improve-data-quality-in-clinical-trials/]
- 72. Governance in Pharma: Compliance and Integrity Data Quality [https://www.acceldata.io/blog/a-comprehensive-guide-to-data-quality-governance-in-pharmaceuticals]
- 73. Data Quality Framework Guide: Components To ... [https://www.montecarlodata.com/blog-data-quality-framework/]
- 74. Data Quality Frameworks guide for pharma & life sciences [https://www.ideagen.com/thought-leadership/blog/data-quality-frameworks-dqf-guide]
- 75. Issues Affecting the Pharmaceutical Industry: Finding... Data Quality [https://firsteigen.com/blog/data-quality-issues-affecting-the-pharmaceutical-industry-finding-a-solution/]
- 76. Data quality management in big data: Strategies, tools, and ... [https://www.sciencedirect.com/science/article/pii/S0743731525000346]
- 77. Data Quality in Health Research: Integrative Literature Review [https://pmc.ncbi.nlm.nih.gov/articles/PMC10646672/]
- 78. Data Silos, Why They're a Problem, & How to Fix It [https://www.talend.com/resources/what-are-data-silos/]
- 79. Data Silos Explained: Problems They Cause and Solutions [https://www.databricks.com/blog/data-silos-explained-problems-they-cause-and-solutions]
- 80. The Data Silo Challenge: Breaking Down Barriers to ... [https://www.linkedin.com/pulse/data-silo-challenge-breaking-down-barriers-integration-savan-group-bglfe]
- 81. Data Sharing FAQ - Actionable Intelligence for Social Policy [https://aisp.upenn.edu/data-sharing-faq/]
- 82. Best practices for cross-government data sharing [https://www.databricks.com/blog/2023/02/21/best-practices-cross-government-data-sharing.html]
- 83. Request PTAC Training or Technical Assistance [http://studentprivacy.ed.gov/request-ptac-training-or-technical-assistance]
- 84. Bias in AI | Examples, Causes & Mitigation Strategies 2025 [https://kodexolabs.com/bias-in-ai/]
- 85. How to Prevent AI Bias in 2025 [https://nwai.co/how-to-prevent-ai-bias-in-2025/]
- 86. How Does ISO 42001 Address Algorithmic Bias in 2025? [https://nwai.co/how-does-iso-42001-address-algorithmic-bias-in-2025/]
- 87. Algorithm fairness in artificial intelligence for medicine and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10632090/]
- 88. Making sense of AI: bias, trust and transparency in pharma ... [https://www.drugtargetreview.com/article/183358/making-sense-of-ai-bias-trust-and-transparency-in-pharma-rd/]
- 89. Unsupervised bias detection tool [https://algorithmaudit.eu/technical-tools/bdt/]
- 90. Landmark AI framework sets new standard for tackling ... [https://www.dlapiper.com/en/insights/publications/ai-outlook/2025/landmark-ai-framework-sets-new-standard-for-tackling-algorithmic-bias]
- 91. Effective Techniques for Reducing Bias in Data Collection [https://www.sapien.io/blog/bias-in-data-collection-6-practical-steps-to-minimize-bias]
- 92. Essential Open-Source Tools for Bias Detection and ... [https://www.turingpost.com/p/ai-fairness-tools]
- 93. Guide to Real-Time Data in 2025 | Architecture and More [https://www.aezion.com/blogs/real-time-data/]
- 94. Real-Time Data Tracking Explained: Strategies for 2025 [https://reportz.io/digital-marketing/real-time-data-tracking-guide-2025/]
- 95. Clinical trial data analytics: Revolution in 2025 [https://lifebit.ai/blog/clinical-trial-data-analytics/]
- 96. 39 Key Facts Every Data Leader Should Know in 2025 [https://www.integrate.io/blog/real-time-data-integration-growth-rates/]
- 97. 10 Critical Third-Party Risk Management Challenges in ... [https://www.processunity.com/resources/blogs/10-critical-third-party-risk-management-challenges-and-how-to-mitigate-them/]
- 98. 4-Stage Vendor Risk Management Framework (2025 Edition) [https://www.upguard.com/blog/vendor-risk-management-implementation-framework]
- 99. A Playbook for Vendor Risk Assessment in 2026 [https://panorays.com/blog/vendor-risk-assessment-complete-guide/]
- 100. Regulatory Challenges - Third-Party Risk Management [https://www.certa.ai/blogs/navigating-regulatory-challenges-with-third-party-risk-management]
- 101. Ultimate Guide to Vendor Risk Scoring 2025 [https://censinet.com/perspectives/ultimate-guide-to-vendor-risk-scoring-2025]
- 102. Top Main Challenges of TPRM [https://veridion.com/blog-posts/third-party-risk-management-challenges/]
- 103. Data Accuracy in 2025: Ensure Reliable, Quality Data [https://atlan.com/data-accuracy-101-guide/]
- 104. Data Validation Techniques: Complete Guide 2025 [https://www.alation.com/blog/data-validation-techniques/]
- 105. The Best 5 Data Validation Tools in 2025 [https://numerous.ai/blog/data-validation-tools]
- 106. 8 Essential Data Validation Techniques for 2025 [https://osher.com.au/blog/data-validation-techniques/]
- 107. 7 Best Practices for Data Quality Management in 2025 [https://www.invensis.net/blog/effective-data-quality-management-best-practices]
- 108. Data Quality Tools 2025: The Complete Buyer's Guide to ... [https://www.ovaledge.com/blog/data-quality-tools/]
- 109. The data validation landscape in 2025 [https://aeturrell.com/blog/posts/the-data-validation-landscape-in-2025/]
- 110. Midyear Momentum: What's Trending in Data Privacy for ... [https://trustarc.com/resource/midyear-momentum-data-privacy-trends-2025/]
- 111. AI and Data Protection in 2025: Everything That Rises Must ... [https://www.thinkbrg.com/thinkset/ai-and-data-protection-in-2025-everything-that-rises-must-converge/]
- 112. The Future of US FDA Pharmaceutical Validation Services ... [https://confiancapharmazon.com/future-us-fda-pharmaceutical-validation-services-2025/]
- 113. What to look for in automated regulatory compliance ... [https://www.thoropass.com/blog/automated-regulatory-compliance-software]
- 114. Regulating the Use of AI in Drug Development: Legal ... [https://www.fdli.org/2025/07/regulating-the-use-of-ai-in-drug-development-legal-challenges-and-compliance-strategies/]
- 115. The Importance of Regulatory Compliance Automation in 2025 [https://scytale.ai/center/grc/the-importance-of-regulatory-compliance-automation/]
- 116. The Role of Automation in Enhancing Regulatory ... [https://www.vitrana.com/the-role-of-automation-in-enhancing-regulatory-compliance-in-pharmacovigilance/]
- 117. The Dawn of a New Era of Compliance [https://law.mit.edu/pub/thedawnofaneweraofcompliance]
- 118. The challenge of automated compliance checking - Apollo [https://www.repository.cam.ac.uk/items/38d99cc1-1059-44f1-986c-18249e8db1f1]
- 119. A New Era for Compliance | Compliance Automation | CSA [https://cloudsecurityalliance.org/blog/2025/04/29/a-new-era-for-compliance-introducing-the-compliance-automation-revolution-car]
- 120. Top 13 Compliance Automation Tools in 2025 [https://www.zluri.com/blog/compliance-automation-tools]
- 121. OWL Property Restrictions vs. SHACL - constraints [https://stackoverflow.com/questions/44767223/owl-property-restrictions-vs-shacl]
- 122. What is SHACL? (With Examples) [https://medium.com/fluree/what-is-shacl-with-examples-2697f659d465]
- 123. Comparative analysis of approaches for automated ... [https://www.sciencedirect.com/science/article/pii/S1474034624000910]
- 124. Validation of technical requirements for a BIM model using ... [https://www.sciencedirect.com/science/article/pii/S1474034624000740]
- 125. IFC Validation Service [https://www.buildingsmart.org/users/services/validation-service/]
- 126. JSON Schema - Specification [#section] [https://json-schema.org/specification]
- 127. A Vocabulary for Structural Validation of JSON [https://json-schema.org/draft/2020-12/json-schema-validation]
- 128. a new approach for IFC to CityJSON conversion [https://link.springer.com/article/10.1007/s12145-024-01343-1]
- 129. 2025 Regology State of Regulatory Compliance Survey [https://www.regology.com/whitepaper/2025-regology-state-of-regulatory-compliance-survey]
- 130. Compliance Monitoring in 2025: Best Practices and Tools [https://www.scrut.io/post/compliance-monitoring]
- 131. Why Continuous Compliance Monitoring is the Future of GRC [https://www.complyance.com/resources/why-continuous-compliance-monitoring-is-the-future-of-grc]
- 132. The Role of Good Documentation Practices (GDP) in ... [https://jafconsulting.com/the-role-of-good-documentation-practices-gdp-in-ensuring-data-integrity-in-clinical-trials/]
- 133. Troubleshooting Protocols - Biological Sciences: Summer ... [https://guides.library.cmu.edu/biologicalsciencesSRI/troubleshooting]
- 134. How to Troubleshoot Experimental Protocols in the Lab [https://www.linkedin.com/advice/1/what-some-strategies-troubleshooting-experimental-jekfe]
- 135. Promoting Reproducibility and Integrity in Observational ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10073307/]
- 136. Drug Development Pipeline: A Complete Guide to All Phases [https://intuitionlabs.ai/articles/drug-development-pipeline-guide]
- 137. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 138. Elements must meet minimum color contrast ratio thresholds [https://dequeuniversity.com/rules/axe/4.8/color-contrast]