Validating Biometric Monitoring Technologies: A 2025 Regulatory Framework for Clinical Research and Drug Development
This article provides researchers, scientists, and drug development professionals with a comprehensive guide to the evolving regulatory landscape for Biometric Monitoring Technologies (BioMeTs) in 2025.
Validating Biometric Monitoring Technologies: A 2025 Regulatory Framework for Clinical Research and Drug Development
Abstract
This article provides researchers, scientists, and drug development professionals with a comprehensive guide to the evolving regulatory landscape for Biometric Monitoring Technologies (BioMeTs) in 2025. It explores the foundational V3 validation framework, details methodologies for integrating AI and multimodal systems, addresses critical challenges in data privacy and algorithmic bias, and establishes best practices for performance benchmarking. The content synthesizes current regulatory standards, technological trends, and strategic imperatives to ensure that biometric technologies are fit-for-purpose in clinical trials and biomedical research.
The Evolving Regulatory Landscape for BioMeTs in 2025
Defining Biometric Monitoring Technologies (BioMeTs) and Their Role in Modern Clinical Trials
Biometric Monitoring Technologies (BioMeTs) represent a category of technologies, primarily wearable devices, that digitally capture and measure physiological and behavioral data in a structured manner. They are defined as "devices that can be worn on human skin to continuously and closely monitor an individual’s activities, without interrupting or limiting the user’s motions" [1]. In the context of clinical research, BioMeTs facilitate the continuous, remote monitoring of patient outcomes outside traditional hospital settings, unlocking new dimensions of objective, real-world data [1]. The global wearable electronics market, estimated at $32.5 billion in 2022 and projected to reach $173.7 billion by 2030, underscores the rapid growth and adoption of these technologies [1]. Their application in clinical trials is driven by the need for more ecologically valid data, the ability to capture rare events, and the potential to reduce the frequency of site visits, thereby lowering patient burden and trial costs.
Categorization and Comparison of Major BioMeTs
BioMeTs can be categorized based on their form factor, physiological parameters measured, and their application in clinical trials. The table below summarizes the key technologies, their data modalities, and primary clinical use cases.
Table 1: Comparison of Major Biometric Monitoring Technologies in Clinical Research
| Technology Category | Measured Parameters/Data Modalities | Common Clinical Trial Applications | Key Strengths |
|---|---|---|---|
| Electroencephalography (EEG) | Neuronal electrical activity (brain rhythms) [2] | Motor imagery decoding for Brain-Computer Interfaces (BCIs), monitoring neurological disorders [2] | High temporal resolution (milliseconds) [3] |
| Functional Near-Infrared Spectroscopy (fNIRS) | Hemodynamic responses (changes in oxygenated/deoxygenated hemoglobin) [2] | Motor imagery BCIs, cognitive workload assessment, neurorehabilitation [2] [3] | Better spatial resolution than EEG; robust to motion artifacts [3] |
| Multimodal EEG-fNIRS | Combined neuro-electrical and hemodynamic activity [4] | Advanced BCIs, comprehensive brain state decoding in naturalistic settings [4] [3] | Complementary information enhances spatiotemporal resolution and classification performance [4] |
| Consumer Wearables (e.g., Smartwatches) | Heart rate, physical activity, oxygen saturation, sleep patterns [1] | Monitoring chronic diseases (cardiac, respiratory, neurodegenerative), detecting disease onset (e.g., arrhythmias) [1] | High patient acceptability, continuous data collection in real-world settings |
The convergence of these technologies with artificial intelligence (AI) and big data analytics is transforming their utility. AI algorithms can analyze vast amounts of biometric data to identify potential safety concerns, predict drug efficacy, and optimize trial operations [5] [6]. Furthermore, the rise of "risk-based everything" in clinical data management encourages sponsors to focus monitoring efforts on the most critical biometric data points, enhancing trial quality and efficiency [7].
Experimental Data and Performance Comparison
The validation of BioMeTs relies on rigorous experiments demonstrating their technical performance and clinical utility. The following section details key experimental protocols and outcomes for prominent BioMet categories.
Multimodal Brain-Computer Interface (BCI) Decoding
Experimental Protocol: A landmark study creating a multimodal EEG-fNIRS dataset involved 18 subjects performing eight distinct motor imagery (MI) tasks related to hand, wrist, elbow, and shoulder movements [2]. Each subject completed 320 trials, resulting in a total of 5,760 trials of simultaneously recorded EEG and fNIRS data [2]. The protocol for each trial was as follows: a 2-second rest period with a fixation cross, a 2-second visual and text cue indicating the task, a 4-second motor imagery period, and a final 10-12 second rest period to allow fNIRS hemodynamic responses to return to baseline [2]. EEG was recorded using a 64-channel cap with a sampling frequency of 1000 Hz, while fNIRS was collected with a system using 8 sources and 8 detectors, resulting in 24 channels at a sampling rate of 7.8125 Hz [2].
Performance Outcomes: When this dataset was used to train a typical deep learning model (ShallowConvNet) with data augmentation, the highest classification accuracy of 65.49% was achieved for distinguishing between two complex tasks: hand open/close and shoulder pronation/supination using EEG data [2]. This demonstrates the feasibility of decoding fine-grained motor intentions from the same limb, a significant advancement over traditional left/right hand MI paradigms.
Representation Learning for Few-Shot Classification
Experimental Protocol: To address the challenge of limited labeled data, a novel multimodal EEG–fNIRS Representation-learning Model (EFRM) was developed [4]. This model employs a two-stage process: a pre-training stage that learns both modality-specific and shared representations from large-scale unlabeled data, followed by a transfer learning stage where the model is adapted to specific tasks with minimal labeled samples [4]. The pre-training leveraged approximately 1,250 hours of brain signal recordings from 918 participants [4]. The model uses a Masked Autoencoder (MAE) to learn modality-specific features and contrastive learning to align the shared representations between EEG and fNIRS [4].
Performance Outcomes: The EFRM model demonstrated competitive performance compared to state-of-the-art supervised learning models, even with very few labeled samples [4]. It showed significant improvements in fNIRS classification performance by leveraging the shared domain knowledge learned from the multimodal pre-training. This approach provides a robust framework for building accurate BioMet classifiers without the need for massive, expensively labeled datasets [4].
Table 2: Quantitative Performance of BioMet Classification Models
| Model/Algorithm | Data Modality | Classification Task | Reported Performance |
|---|---|---|---|
| ShallowConvNet [2] | EEG | Hand MI vs. Shoulder MI | 65.49% Accuracy |
| Multimodal EFRM [4] | EEG-fNIRS | Few-shot brain-signal classification | Competitive with supervised models; significant gains for fNIRS |
| AI for Clinical Trial Risk [6] | Diverse (EHR, genomic, etc.) | Adverse Event Prediction | AUROC up to 96% |
The workflow for developing and validating such a multimodal model can be summarized as follows:
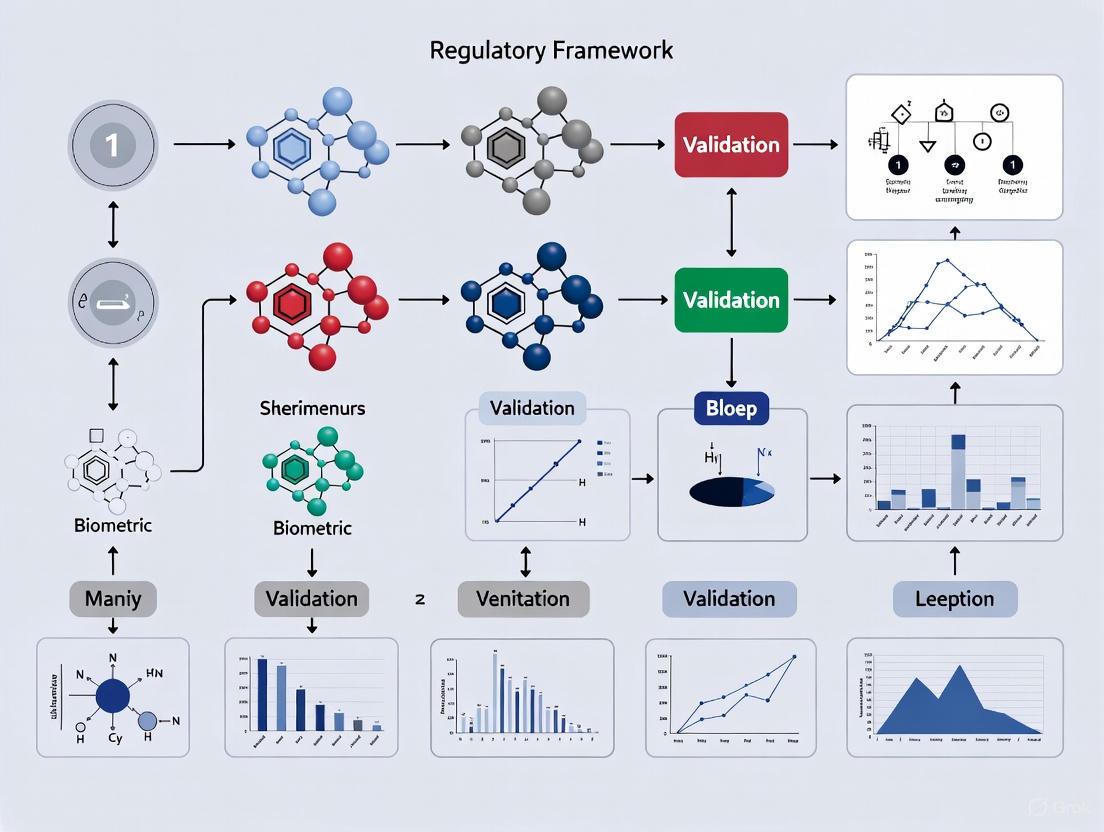
Diagram 1: Workflow for multimodal representation learning with EEG and fNIRS signals, enabling few-shot learning for classification tasks [4].
Detailed Methodologies and Signaling Pathways
A deep understanding of the underlying physiology and data processing workflows is critical for the valid application of BioMeTs.
The Neurovascular Coupling Pathway
The synergistic value of multimodal EEG-fNIRS is rooted in Neurovascular Coupling (NVC), the biological process that links neural activity to subsequent changes in cerebral blood flow [4]. This relationship forms the foundation for correlating electrical and hemodynamic brain signals.
Diagram 2: The neurovascular coupling pathway, linking neural activity measured by EEG to the hemodynamic response measured by fNIRS [4] [3].
Experimental Workflow for a Multimodal BCI Study
A standardized experimental protocol is essential for generating high-quality, reproducible data. The following workflow, derived from a public dataset creation study, outlines the key steps [2].
Diagram 3: Standardized experimental workflow for a multimodal EEG-fNIRS motor imagery study [2].
The Scientist's Toolkit: Key Research Reagent Solutions
The successful implementation of BioMet studies requires a suite of specialized hardware, software, and data resources. The following table details essential components of a modern BioMet research toolkit.
Table 3: Essential Research Reagent Solutions for BioMet Studies
| Tool / Resource | Function / Description | Example Use Case |
|---|---|---|
| 64-channel EEG System (e.g., Neuroscan SynAmps2) | Records electrical brain activity with high temporal resolution from the whole scalp [2]. | Capturing event-related potentials (ERPs) or motor imagery-related oscillations [2]. |
| fNIRS System (e.g., NIRScout) | Measures hemodynamic responses (changes in HbO/HbR) using near-infrared light [2]. | Localizing brain activation associated with cognitive or motor tasks [2] [3]. |
| Multimodal EEG-fNIRS Caps | Integrated headgear allowing simultaneous, co-located recording of both modalities. | Ensuring data is spatially and temporally aligned for fusion algorithms [2] [4]. |
| Public BioMet Datasets | Curated, annotated datasets for benchmarking algorithms (e.g., the 8-task MI dataset) [2]. | Training and validating machine learning models without primary data collection [2]. |
| Pre-trained Models (e.g., EFRM, BENDR) | Foundation models pre-trained on large-scale brain signal data [8] [4]. | Enabling few-shot or transfer learning for new tasks with limited labeled data [4]. |
| Data Fusion & ML Platforms | Software tools for artifact removal, feature extraction, and multimodal classification [3]. | Implementing advanced analysis pipelines, such as source decomposition or deep learning [3]. |
Biometric Monitoring Technologies are fundamentally reshaping the landscape of clinical trials by providing continuous, objective, and multidimensional data from patients in their natural environments. From consumer wearables tracking vital signs to sophisticated multimodal brain imaging systems like EEG-fNIRS, BioMeTs offer unprecedented insights into disease progression and treatment efficacy. The integration of these technologies with advanced AI and data-driven methodologies, such as risk-based monitoring and representation learning, is enhancing the efficiency, cost-effectiveness, and predictive power of clinical research. As the field matures, the continued validation of BioMeTs within robust regulatory frameworks will be paramount to fully realizing their potential in delivering better clinical solutions and accelerating drug development.
Biometric data, derived from the precise measurement of an individual's unique physical, physiological, or behavioral characteristics, represents a particularly sensitive category of personal information. Unlike passwords or identification cards, biometric identifiers—such as fingerprints, facial patterns, iris structures, and voiceprints—are inherently linked to an individual and are fundamentally immutable. This permanence and uniqueness make biometric data highly valuable for authentication and identification purposes in research and commercial applications, but also magnify the privacy and security risks associated with its processing. A data breach involving biometric information carries consequences far more severe than one involving traditional data, as individuals cannot change their fingerprints or facial structure once compromised.
The escalating integration of biometric monitoring technologies into research environments, particularly in clinical trials and pharmaceutical development, necessitates a rigorous understanding of the complex regulatory landscape governing its use. Researchers and organizations operating globally must navigate a fragmented framework of regulations that apply different standards, requirements, and protections. The European Union's General Data Protection Regulation (GDPR) establishes a stringent, rights-based approach, while the United States' Health Insurance Portability and Accountability Act (HIPAA) provides a sector-specific rule for health information. Concurrently, state-level laws like the California Consumer Privacy Act (CCPA), as amended by the CPRA, create a patchwork of requirements within the U.S. This guide provides a detailed comparative analysis of these core regulatory pillars, offering researchers and drug development professionals the essential knowledge for ensuring compliant and ethical handling of biometric data in a global context.
Core Regulatory Frameworks: A Detailed Analysis
The General Data Protection Regulation (GDPR)
The GDPR is a comprehensive data privacy law that applies to all processing of personal data of individuals in the European Economic Area (EEA), regardless of where the processing organization is located [9]. For researchers using biometric data, the most critical provision is its classification of biometric data specifically used for the purpose of uniquely identifying a person as a "special category of data" (akin to health data or religious beliefs) [10]. This classification triggers the highest level of protection under the regulation.
Lawful Basis for Processing: Processing biometric data under the GDPR requires identifying both a lawful basis for general processing (e.g., consent, public interest) and an additional, specific condition for processing special category data [11]. Explicit consent is the most common and often the most appropriate condition for research contexts [10]. This consent must be a freely given, specific, informed, and unambiguous indication of the data subject's wishes, demonstrated by a clear affirmative statement or action [11] [9]. The GDPR also mandates adherence to core principles, including purpose limitation, data minimization, and storage limitation, meaning researchers can only collect biometric data for specified, explicit, and legitimate purposes and retain it for no longer than necessary [9].
Data Subject Rights: The GDPR grants individuals robust rights over their data, including the right to access their biometric data, the right to rectification of inaccurate data, and the powerful right to erasure ('right to be forgotten') [10] [12]. Researchers must implement processes to facilitate these rights within the timelines stipulated by the regulation.
Security and Accountability: Organizations must implement appropriate technical and organizational measures to ensure a level of security appropriate to the high risk presented by biometric data processing, potentially including encryption, access controls, and regular security testing [10]. A Data Protection Impact Assessment (DPIA) is mandatory for processing operations that are likely to result in a high risk to individuals' rights and freedoms, a category that typically includes the systematic processing of biometric data [10]. The accountability principle requires organizations to be able to demonstrate their compliance with all these principles [9].
The Health Insurance Portability and Accountability Act (HIPAA)
HIPAA is a U.S. federal law that establishes standards for the protection of certain health information. Its scope is narrower than the GDPR, as it applies specifically to "covered entities" (healthcare providers, health plans, healthcare clearinghouses) and their "business associates" (contractors that handle protected health information on their behalf) [13] [12].
Protected Health Information (PHI): The core of HIPAA is the protection of Protected Health Information (PHI), which is individually identifiable health information that is created, received, or maintained by a covered entity [12]. Biometric data, such as a fingerprint used to identify a patient in a hospital, would be considered PHI if it is linked to health or payment information.
The Security Rule: The HIPAA Security Rule establishes national standards for securing electronic PHI (ePHI) [14]. It requires the implementation of administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and availability of ePHI. The rule is flexible and scalable, allowing organizations to implement measures appropriate to their size and complexity. In response to rising cyber threats, 2025 proposed updates to the HIPAA Security Rule seek to strengthen these requirements by mandating specific controls like multi-factor authentication (MFA) for all access to ePHI, enhanced data encryption protocols (both at rest and in transit), and regular vulnerability scanning and penetration testing [14] [15].
Patient Rights: Under HIPAA, patients have rights to access their own health information, request amendments, and receive an accounting of disclosures [12]. However, these rights are generally less extensive than those under the GDPR; for instance, HIPAA does not provide a broad "right to be forgotten" that would allow a patient to demand the deletion of their medical records from a covered entity.
The California Consumer Privacy Act (CCPA/CPRA)
The CCPA, as amended by the CPRA, is a comprehensive state-level privacy law that grants California residents significant control over their personal information. It applies to for-profit businesses that operate in California and meet specific revenue or data processing thresholds [16].
Biometric Information as Sensitive Personal Information: The CCPA defines "personal information" broadly. While it does not single out biometric data as a "special category" in the same way as the GDPR, it classifies biometric information as a form of "sensitive personal information" [16]. This classification gives consumers the right to direct businesses to limit the use and disclosure of their sensitive personal information to that which is necessary to provide the requested goods or services.
Consumer Rights and Opt-Out Model: The CCPA is founded on an opt-out model, contrasting with the GDPR's opt-in default [17]. It grants California consumers the right to know what personal information is collected about them, the right to delete it, the right to correct inaccurate information, and the right to opt-out of the "sale" or "sharing" of their personal information [16]. Businesses must honor user-enabled global privacy controls, like the Global Privacy Control (GPC), as a valid opt-out request [17] [16].
2025 Regulatory Updates: New CCPA regulations approved in 2025 introduce significant new obligations for businesses, including requirements for cybersecurity audits and risk assessments for processing that presents significant risk to consumers [18]. These audits, with deadlines starting in 2028, must assess policies on MFA, encryption, access controls, and more. Furthermore, the regulations now specifically include "neural data" in the definition of sensitive personal information, reflecting the evolving nature of biometric monitoring technologies [18].
Comparative Analysis of Regulatory Pillars
The following tables provide a structured, quantitative comparison of the core regulatory frameworks governing biometric data, highlighting their key differences and overlaps to aid in compliance strategy development.
Table 1: Core Definitions, Scope, and Legal Basis Across Regulatory Frameworks
| Aspect | GDPR | HIPAA | CCPA/CPRA |
|---|---|---|---|
| Geographic Scope | Applies to processing of EU/EEA residents' data, regardless of entity location [9]. | Primarily applies to U.S. covered entities and business associates [12]. | Applies to businesses collecting California residents' data, with extraterritorial effect [17]. |
| Definition of Biometric Data | "Personal data resulting from specific technical processing... relating to physical, physiological, or behavioural characteristics... which allow or confirm the unique identification of that natural person" [10]. | Not explicitly defined; falls under PHI if it is an identifier linked to health information (e.g., fingerprint for patient ID) [13]. | "Biometric information" is defined and classified as "sensitive personal information" [16]. |
| Primary Legal Basis for Research | Explicit consent (for special category data) [10] [11]. | Permitted for research with patient authorization or as part of limited preparatory activities [13]. | Consent not required by default; consumers have right to limit use of sensitive information [17] [16]. |
| Default Consent Model | Opt-In [17]. | N/A (Authorization required for specific uses). | Opt-Out [17]. |
Table 2: Security, Rights, and Enforcement Mechanisms
| Aspect | GDPR | HIPAA | CCPA/CPRA |
|---|---|---|---|
| Core Security Mandates | "Appropriate technical and organisational measures" [9]. DPIA mandatory for high-risk processing [10]. | Administrative, Physical, and Technical Safeguards. 2025 updates propose mandatory MFA, encryption, vulnerability scans [14]. | Cybersecurity audits required for high-risk processors per 2025 rules; must cover MFA, encryption, access controls [18]. |
| Key Data Subject Rights | Right to Access, Rectification, Erasure ('Right to be Forgotten'), Portability [10] [12]. | Right to Access, Request Amendment, Accounting of Disclosures [12]. | Right to Know, Delete, Correct, Opt-Out of Sale/Sharing, Limit Use of Sensitive Information [16]. |
| Penalty Structure | Up to €20 million or 4% of global annual turnover, whichever is higher [13] [9]. | Tiered fines from $100 to $1.5 million per violation category [13]. | Civil penalties up to $7,500 per intentional violation [13]. |
Experimental Protocols for Regulatory Compliance
Validating research protocols against regulatory frameworks requires a systematic approach. The following experimental workflows and methodologies are designed to ensure compliant handling of biometric data.
Protocol 1: Lawful Basis Establishment for Biometric Processing
This protocol provides a step-by-step methodology for determining a lawful basis for processing biometric data under the GDPR, which requires both a general lawful basis and a specific condition for processing special category data.
Methodology Summary: This decision tree guides researchers through the stringent requirements of GDPR Article 9. The primary and most straightforward path is securing explicit consent, which requires a clear statement from the data subject and must be accompanied by a viable, non-biometric alternative (e.g., a PIN code for system access) to ensure the choice is truly free [11]. If consent is not feasible, two alternative grounds may be considered: substantial public interest must be rooted in EU or member state law, while vital interests apply strictly to scenarios necessary to protect someone's life. If none of these conditions can be met, the processing of special category biometric data is not permitted under the GDPR.
Protocol 2: Cross-Border Research Compliance Workflow
For research institutions operating internationally, managing data flows and compliance across multiple jurisdictions is a critical function. This workflow outlines the key steps.
Methodology Summary: This workflow emphasizes a sequential compliance strategy. The process begins with a Jurisdiction Assessment to identify all applicable laws based on the data subjects' locations and the research entity's operations [17] [9]. This is followed by Data Residency & Transfer Mapping to understand where data is stored and transferred, ensuring GDPR restrictions on international transfers are respected. The core of the protocol is the Dual Compliance Check, where researchers must implement both GDPR requirements (like DPIAs and data subject rights procedures) and HIPAA mandates (like Security Rule safeguards and BAAs) for projects involving EU and US patient data [12]. Finally, a State Law Analysis is required to comply with specific statutes like the CCPA, particularly its opt-out and sensitive information rules [17] [18]. This entire process must be underpinned by unified technical safeguards (e.g., encryption, MFA) and meticulous documentation for accountability and audit purposes [10] [14].
The Scientist's Toolkit: Essential Research Reagent Solutions
Navigating the complex regulatory environment requires a set of procedural and technical "reagents." The following table details essential components for a compliant biometric data research framework.
Table 3: Essential Compliance and Security Solutions for Biometric Data Research
| Research Reagent Solution | Function & Purpose | Applicable Regulatory Framework |
|---|---|---|
| Data Protection Impact Assessment (DPIA) Template | A structured tool to systematically identify and mitigate risks of data processing activities before they begin. | GDPR (Mandatory for high-risk processing) [10]. |
| Multi-Factor Authentication (MFA) | A technical security control that requires multiple verification methods to access data, drastically reducing risk of unauthorized access. | HIPAA (Proposed 2025 Mandate) [14], CCPA Cybersecurity Audits [18]. |
| Global Privacy Control (GPC) Signal Recognition | Technical capability to detect and honor a user's browser-level opt-out request for data sale/sharing. | CCPA/CPRA (Legally recognized) [17] [16]. |
| Encryption Protocols (Data at Rest & in Transit) | Cryptographic methods to render data unreadable without a key, protecting confidentiality and integrity. | GDPR (Appropriate security) [9], HIPAA (Proposed 2025 Mandate) [14]. |
| Business Associate Agreement (BAA) / Data Processing Agreement (DPA) | A legally binding contract that ensures third-party vendors (processors) provide sufficient data protection guarantees. | HIPAA (Required for Business Associates) [12], GDPR (Required for Data Processors) [9]. |
| Consent Management Platform (CMP) | A software tool to obtain, manage, and document user consent preferences, ensuring they are specific and withdrawable. | GDPR (Explicit Consent) [10] [11]. |
The field of digital medicine, propelled by advances in sensor technology and data analytics, has given rise to Biometric Monitoring Technologies (BioMeTs). These connected technologies process data from mobile sensors to generate measures of behavioral and physiological function [19]. However, the interdisciplinary nature of digital medicine—drawing from engineering, clinical science, data science, and regulatory science—has led to fragmented terminology and evaluation standards, creating a critical need for a unified framework to ensure these technologies are fit-for-purpose in clinical research and practice [19] [20]. The V3 framework (Verification, Analytical Validation, and Clinical Validation) emerged to address this gap, providing a structured approach to evaluating digital measures across technical, analytical, and clinical dimensions [19].
This framework has become the de facto standard for assessing sensor-based digital health technologies (sDHTs), with the original framework accessed over 30,000 times and cited in more than 250 peer-reviewed publications since its 2020 introduction [21]. Its adoption by regulatory bodies, including the U.S. Food and Drug Administration (FDA) and the European Medicines Agency (EMA), underscores its importance in the regulatory validation of BioMeTs for clinical trials and healthcare applications [21] [22].
The Core Components of the V3 Framework
The V3 framework comprises three distinct but interconnected components that form a comprehensive evidence-generation process for BioMeTs [19].
Verification
Verification constitutes the foundational layer, focusing on the technical performance of the sensors themselves. This process involves systematic evaluation by hardware manufacturers to ensure that sample-level sensor outputs meet pre-specified criteria [19] [22]. Verification occurs computationally (in silico) and at the bench (in vitro), confirming that the raw data captured by the sensor has integrity and that the source is correctly identified [19] [23].
In practice, verification includes checks throughout data collection. For computer vision sensors, this might involve ensuring proper illumination, maintaining contrast between subjects and their background, and confirming that recordings come from the correct sources with precise timestamps [23]. This stage serves as a quality assurance process, verifying consistent and uncorrupted data collection from initiation to completion of a study [23].
Analytical Validation
Analytical validation assesses the performance of algorithms that transform raw sensor data into meaningful physiological or behavioral metrics [19] [22]. This component bridges engineering and clinical expertise, translating evaluation procedures from bench settings to in vivo contexts [19]. Analytical validation determines whether the quantitative metrics generated by an algorithm accurately represent the captured events with appropriate precision and resolution [23].
A key challenge in analytical validation is that digital technologies often measure biological events with greater temporal precision than traditional "gold standard" methods, and for novel endpoints, no direct comparator may exist [23]. To address this, researchers employ a triangulation approach, integrating multiple lines of evidence including biological plausibility, comparison to reference standards where available, and direct observation of measurable outputs [23]. Successful analytical validation requires collaboration between machine learning scientists and biologists to establish clear definitions ensuring digital measures accurately reflect biological phenomena [23].
Clinical Validation
Clinical validation establishes whether a digital measure acceptably identifies, measures, or predicts a meaningful clinical, biological, physical, functional state, or experience in a specified context of use [19] [22]. Typically performed by clinical trial sponsors, this validation demonstrates that the BioMeT-derived measure is biologically meaningful and relevant to health or disease states within a specific research context [19] [23].
This component builds upon analytical validation by demonstrating that digital measures provide insights that are both interpretable and actionable within the intended research or clinical setting [23]. For example, in a toxicology study, clinically validated locomotor activity data may serve as a relevant biomarker for assessing drug-induced central nervous system effects [23]. Clinical validation is typically performed on cohorts of patients with and without the phenotype of interest to establish clinical relevance [19].
Table 1: Core Components of the V3 Framework
| Component | Primary Focus | Key Activities | Typical Responsible Party |
|---|---|---|---|
| Verification | Sensor performance and data integrity | Sample-level sensor evaluation; in silico and in vitro testing; data quality checks | Hardware manufacturers |
| Analytical Validation | Algorithm performance | Assessment of data processing algorithms; precision and accuracy testing; triangulation with reference standards | Algorithm developer (vendor or clinical trial sponsor) |
| Clinical Validation | Clinical relevance | Evaluation in target population; assessment of ability to identify/predict clinical states; determination of biological meaning | Clinical trial sponsor |
The V3+ Extension: Integrating Usability Validation
As clinical research sponsors and healthcare organizations implemented sDHTs at scale, challenges related to user-centricity and real-world implementation emerged [22]. In response, the V3 framework was extended to V3+ through the addition of a fourth component: usability validation [22].
The Need for Usability Validation
Real-world examples highlighted limitations in the original V3 framework. In the Wearable Assessment in the Clinic and at Home in Parkinson's Disease study, tremor classification data were missing for 50% of participants due to inadvertent deactivation of device permissions [22]. Similarly, the FDA recalled a specific blood glucose monitor because the product could inadvertently switch units of measure during battery insertion during normal use [22]. These examples underscored that even technically sound devices could fail due to usability issues, necessitating an expanded framework.
Components of Usability Validation
The usability validation component of V3+ comprises four key activities [22]:
- Develop the use specification: Creating a comprehensive description of intended user groups, their interactions with the sDHT, and their motivations.
- Conduct a use-related risk analysis: Identifying foreseeable risks associated with sDHT use, including use-errors and potential harms from missing data.
- Conduct iterative formative evaluation: Testing sDHT prototypes with users to identify use-errors and inform design improvements.
- Conduct summative evaluation: Formal testing to demonstrate that the sDHT can be used without serious use-errors for critical tasks.
Usability validation ensures that sDHTs can be used optimally at scale by diverse users, paving the way for more inclusive, reliable, and trustworthy digital measures within clinical research and care [22].
Experimental Protocols and Methodologies
Implementing the V3 framework requires rigorous experimental methodologies at each validation stage. Below, we detail protocols for generating evidence for each V3 component.
Verification Protocols
Verification focuses on the data supply chain, ensuring integrity from hardware sensors through data storage [19]. For a computer vision-based monitoring system, verification would include [23]:
- Illumination verification: Confirm consistent, adequate lighting conditions across all recording environments using calibrated light meters. Document minimum and maximum lux values during acquisition periods.
- Subject-background contrast validation: Quantify contrast ratios between subject and background across all possible environments. Establish minimum acceptable contrast ratio threshold (e.g., ≥3:1).
- Source identification testing: Implement automated checks confirming recordings originate from correct sources with proper animal/patient identification and precise timestamps.
- Data integrity checks: Establish protocols for verifying consistent, uncorrupted data collection throughout intended study period, including checks for data gaps or corruption.
Analytical Validation Protocols
Analytical validation employs a triangulation approach when traditional gold standards are inadequate [23]. For validating a digital locomotion measure:
- Reference standard comparison: Compare digital locomotion measures against manually scored video observations by trained experts. Calculate agreement statistics (e.g., intraclass correlation coefficients, Cohen's kappa).
- Biological plausibility assessment: Examine whether digital measures demonstrate expected responses to known stimuli or interventions. For example, assess if locomotor activity appropriately decreases following sedative administration.
- Precision evaluation: Conduct test-retest reliability studies under consistent conditions to establish within-subject and between-subject variability.
- Cross-method correlation: Compare digital measures with established but imperfect methods (e.g., photobeam breaks) to identify consistent response patterns despite absolute value differences.
Clinical Validation Protocols
Clinical validation establishes biological meaningfulness and context relevance [23]. For validating a digital measure of respiratory rate in a toxicology study:
- Population stratification: Enroll animals or patients with and without the condition of interest (e.g., drug-induced respiratory depression vs. healthy controls).
- Clinical reference standard testing: Compare digital respiratory measures against clinically accepted standards (e.g., plethysmography) using Bland-Altman analysis and correlation coefficients.
- Intervention response assessment: Evaluate whether digital measures detect expected changes following interventions with known effects (e.g., respiratory stimulants or depressants).
- Dose-response characterization: For toxicology studies, establish whether the digital measure demonstrates dose-dependent responses to toxicant exposure.
- Outcome prediction validation: Assess whether the digital measure predicts clinically relevant outcomes (e.g., need for medical intervention, survival).
Table 2: Methodological Approaches Across V3 Components
| V3 Component | Primary Methodologies | Key Outcome Measures | Acceptance Criteria |
|---|---|---|---|
| Verification | Technical specification testing; data integrity checks; environmental testing | Data completeness; signal-to-noise ratio; adherence to technical specifications | Meeting all pre-specified technical performance criteria |
| Analytical Validation | Comparison to reference standards; triangulation; precision studies; reliability testing | Agreement statistics (ICC, kappa); correlation coefficients; sensitivity; specificity | Sufficient accuracy and precision for intended measurement purpose |
| Clinical Validation | Cohort studies; intervention studies; outcome prediction; dose-response studies | Clinical accuracy; predictive values; effect sizes; clinical outcome correlations | Statistically significant association with clinical states or outcomes |
Framework Adaptations and Applications
The V3 framework has demonstrated remarkable adaptability across domains, with tailored implementations emerging for specific applications.
Preclinical In Vivo Adaptation
The In Vivo V3 Framework adapts the original clinical framework for preclinical animal research [23] [24]. This adaptation addresses unique challenges including sensor verification in variable environments, and analytical validation ensuring data outputs accurately reflect intended physiological or behavioral constructs in animal models [24].
In preclinical applications, the framework must account for species-specific behaviors, the need for non-invasive monitoring, and requirements for continuous data collection in home cage environments [23] [24]. The framework emphasizes replicability across species and experimental setups—an aspect critical due to inherent variability in animal models [24].
Regulatory Alignment
The V3 framework aligns with regulatory expectations for fit-for-purpose evaluation of digital health technologies [19] [22]. In the United States, regulators evaluate claims made for a product rather than the product's capabilities per se, making the framework's structured evidence generation particularly valuable for regulatory submissions [19].
The framework has been referenced by both the FDA and EMA in discussions of digital measure validation [21] [22]. This regulatory recognition positions V3 as a valuable tool for sponsors seeking qualification of digital measures as drug development tools or for regulatory endorsement of digital endpoints [22].
Comparative Analysis: V3 Versus Traditional Validation Approaches
The V3 framework addresses critical limitations of traditional validation approaches for digital measures.
Limitations of Traditional Approaches
Traditional validation methods for medical devices often employ siloed practices with discipline-specific terminology and standards [19]. This fragmentation creates confusion and inefficiency in evaluating digital technologies that inherently span multiple disciplines [19]. Additionally, traditional approaches often fail to distinguish between the technical validation of sensors and algorithms versus the clinical validation of derived measures [19].
For digital measures that capture novel constructs or provide higher temporal resolution than existing methods, traditional validation against potentially suboptimal "gold standards" can be particularly challenging [23]. The lack of a structured framework for evaluating multimodal and composite digital measures further limits traditional approaches [20].
Advantages of the V3 Framework
The V3 framework provides a comprehensive, structured approach that explicitly addresses the multi-layered nature of digital measure validation [19]. By separating verification, analytical validation, and clinical validation, the framework enables appropriate expertise to be applied at each stage while maintaining an integrated view of the overall evidence generation process [19].
The framework's common vocabulary bridges disciplinary divides, facilitating more effective communication and collaboration across engineering, data science, clinical, and regulatory domains [19]. This shared language enables generation of a common and meaningful evidence base for BioMeTs [19].
For novel measures, the framework's recognition of triangulation approaches to analytical validation provides methodological flexibility when direct comparison to gold standards is impossible or inappropriate [23]. This is particularly valuable for digital measures capturing previously unmeasurable aspects of physiology or behavior.
The Scientist's Toolkit: Essential Research Reagent Solutions
Implementing the V3 framework requires specific methodological tools and approaches at each validation stage. The table below details key "research reagent solutions" essential for executing V3 evaluations.
Table 3: Essential Research Reagents and Tools for V3 Implementation
| Tool Category | Specific Examples | Function in V3 Implementation | Key Considerations |
|---|---|---|---|
| Reference Standard Technologies | Plethysmography systems; manual video observation protocols; clinical grade lab equipment | Provides comparator measures for analytical and clinical validation | Select based on measurement accuracy, feasibility, and relevance to target construct |
| Data Quality Assessment Tools | Signal-to-noise calculation algorithms; data completeness dashboards; outlier detection scripts | Enables verification of data integrity throughout collection pipeline | Should be implemented proactively with pre-specified quality thresholds |
| Statistical Analysis Packages | Agreement statistics (ICC, kappa); Bland-Altman analysis; correlation analyses; mixed effects models | Supports quantitative assessment across all V3 components | Selection should align with research questions and data characteristics |
| Sensor Testing Equipment | Light meters; temperature chambers; motion simulators; signal generators | Facilitates technical verification under controlled conditions | Should reflect intended use environment conditions |
| Usability Testing Frameworks | Formative evaluation protocols; use-error categorization systems; task success metrics | Supports usability validation in V3+ implementation | Should involve representative users from target population |
The V3 framework represents a significant advancement in the systematic evaluation of Biometric Monitoring Technologies, providing a structured approach to establishing whether digital measures are fit-for-purpose [19]. Its core components—verification, analytical validation, and clinical validation—address the multi-layered evidence needs for digital measures across technical, analytical, and clinical dimensions [19].
The framework's evolution to V3+ through the incorporation of usability validation demonstrates its responsiveness to real-world implementation challenges [22]. This extension ensures that technologies are not only technically sound and clinically relevant but also user-centric and scalable across diverse populations and settings [22].
As digital measures continue to gain acceptance as primary endpoints in clinical trials and find broader application in clinical practice, the V3 framework provides a foundational methodology for generating the evidence necessary to support regulatory, clinical, and payer decision-making [19] [22]. The framework's adaptability across clinical and preclinical contexts further enhances its utility in the translational pipeline [23] [24].
For researchers, scientists, and drug development professionals, understanding and implementing the V3 framework is increasingly essential for successfully developing and deploying digital measures that are trustworthy, meaningful, and ultimately beneficial to patients.
V3 Framework Validation Workflow
Digital Measure Evidence Generation
In 2025, the field of biometric monitoring technologies (BioMeTs) is defined by a critical imperative: establishing robust validation standards that ensure data quality, clinical relevance, and regulatory compliance. As connected digital medicine products that process sensor data to generate measures of physiological function, BioMeTs represent a revolutionary tool for clinical research and patient care [25]. However, their rapid proliferation has created a validation landscape reminiscent of laboratory biomarkers two decades ago—lacking standardized frameworks, common terminology, and widely accepted performance characteristics [25]. This guide examines how major funding entities—including the National Institutes of Health (NIH), the Advanced Research Projects Agency for Health (ARPA-H), and private grant-making organizations—are strategically directing resources to address these gaps through specific validation requirements and support for standardized frameworks.
The alignment between funding priorities and validation standards represents a pivotal shift in the BioMeTs ecosystem. Funders are increasingly mandating rigorous evaluation frameworks as a precondition for support, thereby accelerating the adoption of practices that ensure BioMeTs are "fit-for-purpose" for specific research contexts and clinical applications [25] [19]. This convergence is particularly evident in areas such as AI-powered diagnostics, remote patient monitoring, and digital biomarker development, where funders are prioritizing projects that demonstrate adherence to evolving validation paradigms [26].
Foundational Validation Framework: The V3 Model
The evaluation of BioMeTs requires a structured, multi-stage process to establish their reliability and clinical relevance. The Verification, Analytical Validation, and Clinical Validation (V3) framework has emerged as the foundational model for this purpose, providing a standardized approach to determining whether a BioMeT is "fit-for-purpose" [19].
V3 Stage Definitions and Requirements
Verification: A systematic evaluation process conducted by hardware manufacturers to confirm that sample-level sensor outputs meet specified technical requirements. This stage occurs computationally (in silico) and at the bench (in vitro), focusing on the fundamental technical performance of the sensor hardware itself [19].
Analytical Validation: Conducted at the intersection of engineering and clinical expertise, this stage evaluates the data processing algorithms that convert sample-level sensor measurements into physiological metrics. Analytical validation translates the evaluation procedure from the bench to in vivo settings, typically performed by the entity that created the algorithm (vendor or clinical trial sponsor) [19].
Clinical Validation: Performed by clinical trial sponsors to demonstrate that the BioMeT acceptably identifies, measures, or predicts a clinical, biological, physical, functional state, or experience in the defined context of use. This stage establishes the relationship between the BioMeT-derived metric and clinically meaningful endpoints, typically evaluated on cohorts of patients with and without the phenotype of interest [19].
Funding Landscape and Strategic Imperatives for 2025
Agency-Specific Funding Priorities and Validation Requirements
Table 1: 2025 Federal Funding Priorities for BioMeTs and Associated Validation Requirements
| Funding Agency | 2025 Budget Authority/Request | Primary BioMeT Focus Areas | Key Validation Requirements |
|---|---|---|---|
| National Institutes of Health (NIH) | $50.1 billion requested [26] | • All of Us Research Program (precision medicine) • AI-powered diagnostics • Digital biomarker development | • Adherence to V3 framework • Demonstration of clinical utility • Interoperability with EHR systems • Data standardization across platforms |
| Advanced Research Projects Agency for Health (ARPA-H) | $1.5 billion requested [26] | • Real-time biometric data collection • Privacy-enhancing technologies • Autonomous diagnostic systems [27] | • Human factors testing • Cybersecurity protocols • Bench-to-human testing phases • Algorithm transparency |
| National Institute of Standards and Technology (NIST) | Ongoing program funding [26] | • Biometric standards development • Interoperability testing • Performance benchmarking | • Technical performance standards • Cross-platform compatibility • Reference materials and protocols |
Private and Philanthropic Funding Priorities
Private and philanthropic funders are playing an increasingly important role in advancing BioMeT validation, particularly through support for decentralized clinical trials and digital biomarker development [26]. Notable contributors include:
- Gates Foundation: Focusing on global health applications, particularly resource-limited settings, with emphasis on practical implementation and accessibility of BioMeTs [26].
- Leducq Foundation: Supporting cardiovascular research that integrates biometric data, with requirements for robust statistical validation and clinical correlation [26].
Private sector funding is increasingly directed toward wearable sensors, remote monitoring platforms, and AI-driven diagnostics, with a strong emphasis on generating evidence that supports regulatory submissions and clinical adoption [26].
Experimental Protocols for BioMeT Validation
Protocol 1: Analytical Validation of a Novel Digital Biomarker
Objective: To establish the analytical validity of a novel digital biomarker for monitoring cardiovascular function via a wearable patch.
Materials and Equipment:
- BioMeT device (wearable patch with accelerometer and gyroscope)
- Reference standard (12-lead ECG with synchronized timestamping)
- Controlled motion platform for simulating human movement
- Data acquisition system with secure storage
- Statistical analysis software (R, Python with pandas, sci-kit-learn)
Methodology:
- Device Verification: Confirm sensor specifications per manufacturer claims using calibrated input signals across operational range (e.g., 0-10 Hz for motion sensors) [19].
- Reference Standard Synchronization: Implement precise time-synchronization (±10ms) between BioMeT and reference standard data streams.
- Controlled Environment Testing: Collect data from 30 healthy volunteers performing standardized movements (rest, walking, running) while wearing both BioMeT and reference systems.
- Algorithm Performance Assessment: Evaluate the accuracy, precision, sensitivity, and specificity of the algorithm for detecting specific cardiovascular parameters against the reference standard.
- Statistical Analysis: Calculate intraclass correlation coefficients (ICC) for test-retest reliability, Bland-Altman plots for agreement analysis, and receiver operating characteristic (ROC) curves for classification performance.
Acceptance Criteria: ICC > 0.8, sensitivity and specificity > 0.9 for detecting target physiological states, mean absolute percentage error < 5% for continuous parameters [19].
Protocol 2: Clinical Validation of a Remote Monitoring BioMeT
Objective: To clinically validate a wrist-worn BioMeT for detecting exacerbations in patients with chronic respiratory disease.
Study Design: Prospective observational cohort study with 200 patients followed for 90 days.
Methodology:
- Participant Recruitment: Enroll adults with confirmed diagnosis of moderate-to-severe chronic obstructive pulmonary disease.
- Device Deployment: Provide participants with wrist-worn BioMeT and train on proper use, charging, and data synchronization.
- Data Collection: BioMeT continuously collects motion, heart rate, and respiratory rate data; participants complete daily symptom diaries.
- Event Detection: Algorithm identifies potential exacerbations based on predefined biometric signatures; these are compared with patient-reported events and healthcare utilization records.
- Clinical Correlation: Assess sensitivity, specificity, positive predictive value, and negative predictive value of BioMeT-detected events against clinician-adjudicated exacerbations.
Endpoint Comparison: Compare time to detection between BioMeT algorithm and patient self-report, with statistical analysis using Cox proportional hazards models [25].
The Scientist's Toolkit: Essential Research Reagents for BioMeT Validation
Table 2: Essential Research Reagents and Resources for BioMeT Validation Studies
| Reagent/Resource | Function in Validation | Example Applications | Critical Specifications |
|---|---|---|---|
| Reference Standard Devices | Provides gold-standard measurement for comparison | ECG for cardiovascular BioMeTs, polysomnography for sleep BioMeTs, motion capture for activity BioMeTs | • Validation against primary standards • Measurement uncertainty quantification • Appropriate sampling frequency |
| Data Synchronization Systems | Ensures temporal alignment between BioMeT and reference data | Hardware triggers, network time protocol, custom timestamping | • Sub-100ms synchronization accuracy • Minimal jitter • Robust failure recovery |
| Controlled Testing Environments | Enables verification under known conditions | Motion simulators, environmental chambers, signal generators | • Repeatable testing protocols • Comprehensive parameter sweeps • Real-world condition simulation |
| Open-Source Analysis Libraries | Facilitates standardized data processing and statistical analysis | Python BioSPPy, R signal, MATLAB toolboxes | • Peer-reviewed algorithms • Documentation and examples • Community support and maintenance |
| Validation Data Repositories | Provides benchmark datasets for algorithm development and testing | PhysioNet, Biometric Evaluation datasets | • Expert annotation • Diverse participant demographics • Comprehensive metadata |
Strategic Imperatives for Research Teams
Navigating the 2025 Funding Landscape
Research teams seeking funding for BioMeT development must align their validation strategies with funder priorities and requirements. Key strategic imperatives include:
- Embrace the V3 Framework: Implement verification, analytical validation, and clinical validation as distinct but connected phases of BioMeT evaluation, with documented evidence at each stage [19].
- Address Human Factors Early: Incorporate user-centered design and human factors testing throughout development, as required by ARPA-H and other funders [25] [27].
- Prioritize Data Standards: Ensure interoperability with EHR systems and adherence to data format standards, particularly for NIH-funded projects [26].
- Demonstrate Clinical Utility: Move beyond technical performance to show how BioMeT-derived measures impact clinical decision-making and patient outcomes [19].
The year 2025 represents an inflection point for validation standards in biometric monitoring technologies. Through strategic funding initiatives, NIH, ARPA-H, and private grant-makers are creating an ecosystem where rigorous validation is not just encouraged but required. The adoption of frameworks like V3 provides a common language and methodology for establishing that BioMeTs are truly "fit-for-purpose" for specific research and clinical contexts.
For research teams, success in this evolving landscape requires a proactive approach to validation—one that integrates regulatory science, clinical expertise, and engineering excellence throughout the development process. By aligning with funder priorities and embracing standardized validation frameworks, researchers can accelerate the development of high-quality, clinically valuable BioMeTs that transform healthcare and advance precision medicine.
The fields of wearable sensors and AI-powered diagnostics are rapidly converging to create a new paradigm in biometric monitoring and medical diagnostics. This transformation is primarily driven by the growing demand for remote patient monitoring, the need for more personalized medicine, and advancements in artificial intelligence that can interpret complex physiological data [28] [29]. For researchers, scientists, and drug development professionals, understanding this landscape is crucial for developing valid, reliable, and regulatory-compliant digital measures. These technologies are increasingly being incorporated into clinical trials and pharmaceutical development to provide continuous, objective data on patient outcomes, moving beyond traditional episodic measurements to richer, real-world evidence [24]. The global wearable sensors market, valued at $1.9 billion in 2024 and projected to reach $13.2 billion by 2034, underscores the significant investment and growth in this sector [28]. This article provides a comparative analysis of key technologies and players, framed within the essential context of validation frameworks required for regulatory and scientific acceptance.
The wearable sensors market is segmented by type, application, and end-user, with accelerometers currently dominating the market share by type [28]. Wristwear, such as smartwatches and fitness trackers, represents the largest application segment, while the consumer sector is the largest end-user, followed by healthcare [28]. Regionally, Asia-Pacific held the largest market share in 2024, exceeding 40%, but Europe is expected to witness the highest CAGR during the forecast period [28].
Leading Companies in Wearable Sensors and Digital Health
The competitive landscape includes established semiconductor companies, specialized sensor manufacturers, and emerging digital health technology firms. Key players identified in the wearable sensors market include STMicroelectronics, Panasonic Corporation, Infineon Technologies, Knowles Electronics, NXP Semiconductors, ROHM Semiconductor, TE Connectivity, MEMSIC, Analog Devices, and Murata [28]. These companies primarily compete through product launches and strategic acquisitions to expand their technological capabilities and market reach.
In the broader healthcare technology space, several companies are leading the integration of these sensors into diagnostic and therapeutic applications. Notable companies recognized among the top 50 healthcare technology companies of 2025 include [30]:
- Natera: A leader in cell-free DNA testing for oncology, women's health, and organ health.
- Spring Health: Provides a precision mental health platform for employers and payers.
- Komodo Health: Offers an AI-powered healthcare intelligence platform that tracks de-identified patient journeys.
- CareDx: Specializes in molecular diagnostics and digital tools for transplant patient monitoring.
- Qualifacts: Provides electronic health record solutions for behavioral health organizations.
Comparative Analysis of Wearable Sensor Technologies
Wearable sensors form the foundational layer for biometric monitoring, capturing raw physiological and movement data. The performance characteristics of these sensors directly impact the quality and reliability of the digital measures derived from them. The table below provides a structured comparison of primary wearable sensor technologies based on key parameters critical for research applications.
Table 1: Performance Comparison of Key Wearable Sensor Technologies
| Sensor Technology | Primary Measured Biometrics | Common Form Factors | Key Strengths | Key Limitations / Validation Challenges |
|---|---|---|---|---|
| Inertial Measurement Units (Accelerometers, Gyroscopes) [28] [31] | Movement, acceleration, step count, posture, gait. | Wristwear, Footwear, Bodywear | Compact, low power consumption, well-established for activity profiling. | Data can be noisy; requires complex algorithms for specific movement classification; accuracy varies with placement. |
| Optical Sensors (e.g., PPG) [32] | Heart rate, blood oxygen saturation (SpO₂), potentially blood pressure. | Wristwear, Smart Rings | Non-invasive, enables continuous vital sign monitoring. | Signal susceptible to motion artifacts; skin pigmentation and body hair can affect accuracy; calibration challenges for advanced metrics like blood pressure. |
| Electrodes (Wet, Dry, Microneedle) [32] | Electrical activity of heart (ECG), brain (EEG), muscles (EMG). | Chest Patches, Headbands, Smart Clothing | Provides clinical-grade electrical biosignals; high accuracy for specific physiological events. | Skin contact impedance can affect signal quality (especially dry electrodes); comfort and long-term wearability issues for some designs. |
| Chemical Sensors (e.g., for Interstitial Fluid) [32] | Glucose, lactate, alcohol, electrolytes. | Skin Patches, Smart Watches (emerging) | Potential for continuous, non-invasive monitoring of metabolites. | Maturity varies significantly; calibration and specificity are major hurdles; limited commercial availability for non-glucose analytes. |
Supporting Experimental Data and Validation
The validity of data generated from these sensors is paramount for research use. A 2024 systematic review on the use of wearable devices in field hockey provides insightful experimental data on the performance of GPS and heart rate monitors in a real-world, high-mobility setting. The study reported that the intraclass correlation coefficient (ICC) for these wearable devices showed "reasonably high between-trial ICCs ranging from 0.77 to 0.99," indicating good to excellent reliability [31]. This study highlights both the potential and the challenges of wearable sensor data, noting that "discrepancies in sampling rates and performance bands makes it arduous to draw comparisons between studies" [31]. This underscores the need for standardized experimental protocols, even within a single sport.
Frameworks for Validating Digital Measures in Research
For digital measures to be accepted in pharmaceutical research and development, they must undergo a rigorous validation process. The V3 Framework, developed by the Digital Medicine Society (DiMe) and adapted for preclinical research, provides a structured approach [24]. This framework is essential for establishing the reliability and relevance of digital measures, ensuring they are fit for their intended use in drug discovery and development.
The V3 Validation Framework
The framework breaks down validation into three distinct but connected stages [24]:
- Verification: Confirms that the digital technology accurately captures and stores the intended raw data. This involves ensuring sensors and data acquisition systems function correctly in the intended environment.
- Analytical Validation: Assesses the precision and accuracy of the algorithms that transform the raw sensor data into a meaningful digital measure (e.g., converting raw accelerometer data into a "step count" or "gait score").
- Clinical Validation: Establishes that the digital measure accurately reflects the specific biological, functional, or behavioral state it is intended to measure within its Context of Use (COU).
The following workflow diagram illustrates the application of this framework from technology development to a qualified digital biomarker.
Diagram 1: The V3 Framework for Digital Measure Validation
Experimental Protocol for Sensor Validation
Researchers can implement the V3 framework through a structured experimental protocol. The methodology below is adapted from principles outlined in the validation literature and systematic reviews on wearable technology [31] [24].
- Aim: To determine the validity and reliability of a specific digital measure (e.g., heart rate from a PPG sensor) against an accepted reference standard.
- Experimental Design: A controlled laboratory study with a cross-comparison design.
- Participants: A cohort representative of the intended population (e.g., healthy adults, patients with a specific condition), with sample size justified by a power calculation.
- Protocol:
- Simultaneous Data Collection: Participants wear the test wearable device (e.g., smartwatch) while simultaneously being connected to the reference standard (e.g., 12-lead ECG for heart rate).
- Protocolized Activities: Participants perform a series of activities in a controlled sequence to test the sensor across a range of physiological states. This typically includes:
- Resting (seated, supine)
- Controlled breathing
- Postural changes (e.g., sit-to-stand)
- Steady-state walking/running on a treadmill at varying intensities
- Recovery period
- Data Synchronization: Precise time-synchronization between the test device and the reference standard is critical.
- Data Analysis:
- Statistical Comparison: Use Bland-Altman analysis to assess agreement (bias and limits of agreement) and intraclass correlation coefficients (ICC) for reliability between the test device and the reference standard.
- Error Analysis: Investigate the root cause of any significant discrepancies (e.g., motion artifacts, poor skin contact).
AI-Powered Diagnostics and Clinical Decision Support
The data from wearable sensors serves as a key input for AI-powered diagnostic tools. Artificial intelligence, particularly machine learning and deep learning, is transforming diagnostics by analyzing complex datasets—including medical images, biosignals, and electronic health records—to identify patterns that may elude human observation [29]. The AI diagnostic market is evolving rapidly, with trends pointing toward Explainable AI (XAI), General AI (GAI), and even exploratory Quantum AI (QAI) to enhance accuracy, speed, and trust in these systems [29].
The Emerging Workflow of AI-Assisted Diagnosis
The integration of AI is fundamentally changing clinical workflows. A 2025 qualitative study on stroke care provides a compelling model. Traditionally, diagnosis is an iterative process where a clinician gathers data, forms a hypothesis, and refines it until a diagnostic label is reached. With AI, this process is being transformed [33].
In advanced stroke hubs, the diagnostic journey now often begins with an AI system that processes MRI/CT images and distributes a preliminary diagnosis (e.g., "large vessel occlusion detected") to the entire stroke team within minutes. The clinical team's role then shifts to verifying the AI's claim against other evidence and clinical findings, a process that can trigger early activation of treatment pathways like thrombectomy [33]. This "AI-as-first-reader" model, where the algorithmic output precedes the clinician's diagnosis, represents a significant shift in clinical agency and workflow.
The following diagram contrasts the traditional diagnostic process with the emerging AI-assisted model.
Diagram 2: Traditional vs. AI-Assisted Diagnostic Workflow
Key Considerations for AI Diagnostics in Research
For drug development professionals, several factors are critical when evaluating AI-powered diagnostic tools for use in clinical trials [29] [33]:
- Data Quality and Bias: AI algorithms require large, high-quality, and representative datasets. Biased training data can lead to incorrect diagnoses and unfair outcomes for underrepresented populations.
- Algorithmic Transparency and Explainability: The "black box" nature of some complex AI models poses a challenge for regulatory approval and clinical trust. Explainable AI (XAI) is crucial for understanding the rationale behind an AI's diagnosis.
- Regulatory and Ethical Compliance: Issues of data privacy, security, and informed consent are amplified when using AI. Clear accountability for decisions made with AI assistance must be established.
The Scientist's Toolkit: Essential Research Reagents and Materials
For researchers designing studies involving wearable sensors and digital biomarkers, the following toolkit outlines essential components and their functions, derived from the cited technologies and validation frameworks.
Table 2: Essential Research Toolkit for Digital Biomarker Development
| Tool/Component | Function in Research | Example Specifics |
|---|---|---|
| Multi-Modal Sensor Platform | Captures raw physiological and behavioral data (e.g., acceleration, heart rate, ECG). | Research-grade devices with raw data access (e.g., from ActiGraph, GENEActiv, Empatica) [31]. |
| Reference Standard Instruments | Provides gold-standard measurement for validating digital measures (Analytical Validation). | 12-lead ECG, metabolic cart for energy expenditure, clinical-grade spirometer, lab-based blood analyzers [31] [24]. |
| Data Synchronization System | Precisely time-aligns data from multiple sensors and reference systems. | Dedicated hardware (e.g., LabStreamingLayer) or software-based timestamping with high precision. |
| Algorithm Development Environment | Platform for building and testing algorithms that convert raw sensor data into digital measures. | Python/R with signal processing libraries (e.g., SciPy, TensorFlow, PyTorch) for custom feature extraction and model training [29]. |
| V3 Framework Checklist | Guides the structured validation of the digital measure from sensor to clinical relevance. | A protocol checklist based on Verification, Analytical Validation, and Clinical Validation principles [24]. |
| Regulatory Guidance Documents | Informs study design to meet standards for regulatory submission. | FDA's "Bioanalytical Method Validation Guidance," DiMe's V3 Framework publications, and ICH guidelines [24]. |
The integration of wearable sensors and AI-powered diagnostics presents a transformative opportunity for medical research and drug development. A thorough understanding of the performance characteristics, limitations, and validation requirements of these technologies is fundamental to their successful application. As the field evolves, the rigorous application of frameworks like V3 will be paramount in ensuring that digital measures are reliable, clinically meaningful, and ultimately acceptable to regulators. This will enable researchers to robustly capture the patient experience through continuous, objective data, accelerating the development of new therapeutics and personalized medicine approaches.
Implementing Robust Validation Methodologies and Clinical Applications
Integrating AI and Machine Learning for Enhanced Accuracy and Liveness Detection
The increasing reliance on biometric verification across sectors such as financial services, healthcare, and border security has made robust liveness detection a critical component of identity systems. This technology determines whether a biometric sample comes from a live person present at the time of capture, thereby preventing spoofing attempts using photos, videos, or deepfakes [34]. For researchers and professionals validating these technologies against emerging regulatory frameworks, understanding the integration of AI and machine learning is paramount. These technologies are not merely enhancements but fundamental requirements for achieving the accuracy and reliability demanded by international standards and regulations aiming to validate biometric monitoring technologies [35] [36]. This guide objectively compares the performance of leading liveness detection and accuracy-enhancing methods, providing the experimental data and protocols necessary for rigorous technological assessment.
The Critical Role of AI and ML in Modern Biometrics
Artificial Intelligence (AI), particularly deep learning models, and Machine Learning (ML) have transformed biometrics from a static verification tool into a dynamic, adaptive security layer. These technologies directly address two core challenges: maximizing accuracy in diverse real-world conditions and ensuring robust liveness detection against evolving spoofing attacks.
AI-driven systems, such as Convolutional Neural Networks (CNNs) and the emerging Capsule Networks, analyze facial features with unprecedented detail, identifying subtle characteristics that are imperceptible to the human eye or traditional algorithms [35] [37]. This capability is crucial for maintaining high accuracy across varied demographics and environmental conditions, a key metric for regulatory validation.
Simultaneously, ML models are the foundation of modern liveness detection. They are trained on massive, diverse datasets of real human features and known spoofing artifacts—such as printed photos, digital screens, and masks—to learn the minute differences between live human skin texture, blood flow patterns, and micro-movements compared to inanimate spoofs [34]. This continuous learning process is essential for defending against new, AI-generated deepfakes, whose sophistication is growing rapidly [8] [34].
Comparative Analysis of Liveness Detection Modalities
Liveness detection methodologies are broadly categorized into two approaches, each with distinct mechanisms, strengths, and ideal applications. The following table provides a structured comparison, crucial for evaluating their suitability for specific regulatory and use-case requirements.
Table 1: Comparative Analysis of Active vs. Passive Liveness Detection
| Feature | Active Liveness Detection | Passive Liveness Detection |
|---|---|---|
| User Interaction | Required (e.g., blinking, head turns) [34] | None required; works in the background [34] |
| Detection Method | Motion analysis and response to prompts [34] | AI-based image analysis (texture, depth, micro-expressions) [36] [34] |
| User Experience | More intrusive; may cause friction [34] | Seamless and frictionless [34] |
| Spoofing Resistance | High, depending on implementation [34] | Very high, especially against advanced deepfakes [34] |
| Processing Speed | Slightly slower due to user prompts [34] | Generally faster [34] |
| Best Use Cases | High-risk or high-security environments [34] | Scalable onboarding, mobile-first user experiences [34] |
Experimental Protocols for Liveness Detection
To validate the performance claims of liveness detection systems, researchers employ standardized experimental protocols. These methodologies are designed to simulate real-world spoofing attacks and measure the system's resilience.
Presentation Attack Detection (PAD) Evaluation:
- Objective: To determine the system's ability to correctly reject Presentation Attacks (PAs), such as photos, videos, masks, and deepfakes.
- Protocol: A dataset containing both "bonafide" (live) samples and "attack" (spoof) samples is used. The system processes each sample, and the outcomes are tallied to calculate key metrics like Attack Presentation Classification Error Rate (APCER) and Bonafide Presentation Classification Error Rate (BPCER) in line with the ISO/IEC 30107-3 standard [34].
- Deepfake-Specific Testing: Given the surge in AI-generated fraud, a dedicated protocol involves challenging the system with a dataset of hyper-realistic deepfakes. The model analyzes pixel-level inconsistencies, unnatural eye blinking patterns, and AI-generated artifacts that are not present in live human videos [34]. The quadrupling of deepfake usage from 2023 to 2024 makes this a critical test [34].
User Experience and Performance Benchmarking:
- Objective: To measure the impact of liveness detection on system throughput and user acceptance.
- Protocol: For active liveness, researchers measure the total task completion time and the error rate (how often users fail the challenge). For passive liveness, the focus is on the marginal increase in processing time compared to a baseline facial recognition step. Both methods are evaluated through user satisfaction surveys to quantify perceived friction.
Diagram 1: Liveness Detection Workflow Comparison. This diagram illustrates the divergent user journeys for active (red) and passive (blue) liveness detection methodologies.
Quantitative Performance of AI-Enhanced Facial Recognition
The integration of AI has dramatically elevated the performance benchmarks for facial recognition technology. Under controlled laboratory conditions, top-performing algorithms now demonstrate accuracy rates exceeding 99.5%, with some verification algorithms reaching as high as 99.97%—a performance level that rivals leading iris recognition systems [35]. However, for regulatory validation, it is critical to examine performance across diverse scenarios and demographic groups.
Table 2: AI-Enhanced Facial Recognition Performance Metrics (2024-2025)
| Performance Metric | Laboratory / Optimal Conditions | Real-World / Challenging Conditions | Notes & Context |
|---|---|---|---|
| Top Verification Accuracy | 99.97% [35] | Not directly comparable | Ideal lighting, front-facing, high-resolution images. |
| General Identification Accuracy | >99.5% [35] | Varies significantly | 45 of 105 NIST-tested algorithms were >99% accurate on high-quality images [35]. |
| False Negative Identification Rate (FNIR) | <0.15% [35] | Can increase to 9.3% [35] | Measured at a False Positive Rate (FPIR) of 0.001. "In the wild" factors cause performance drop. |
| Demographic Variance (Error Rates) | N/A | Light-skinned men: ~0.8%Dark-skinned women: >34% [37] | Highlights bias in training data; modern systems are improving, aiming for 98-99% across all groups [35]. |
| Processing Speed | Under 120 milliseconds [37] | Latency can increase with edge computing | 35% improvement from 2022 benchmarks, enabling real-time use cases [37]. |
Experimental Protocols for Accuracy and Bias Assessment
Robust validation of facial recognition systems requires controlled experiments to benchmark accuracy and uncover algorithmic bias.
NIST FRTE Protocol:
- Objective: To provide a standardized, independent benchmark of facial recognition algorithm performance across a range of tasks and datasets.
- Protocol: The National Institute of Standards and Technology (NIST) conducts regular Face Recognition Technology Evaluations (FRTE). Vendors submit their algorithms to NIST, which tests them against massive, curated datasets containing millions of images. The tests measure key metrics like false negative and false positive identification rates under various probe conditions (e.g., different lighting, angles, and image qualities) [35]. This is the global gold standard for performance comparison.
Demographic Differential Analysis:
- Objective: To identify and quantify performance disparities across demographic groups defined by sex, skin tone, and age.
- Protocol: Researchers use datasets annotated with demographic metadata. The same algorithm is tested on subsets of the data for each demographic group, and its performance metrics (e.g., false match rate, false non-match rate) are calculated per group. The relative difference in error rates—such as the significantly higher error rates for dark-skinned women compared to light-skinned men—is a critical measure of algorithmic bias and fairness [37]. This is a fundamental test for regulatory compliance.
Cross-Environment Performance Testing:
- Objective: To evaluate the robustness of an algorithm when moving from ideal laboratory settings to challenging real-world conditions.
- Protocol: An algorithm's performance is first established on a high-quality, curated dataset (e.g., mugshots). It is then tested on a "wild" dataset comprised of images from surveillance cameras, mobile phones, and internet photos with variations in lighting, pose, and resolution. The performance gap, where an error rate can jump from 0.1% to 9.3%, highlights the algorithm's real-world applicability [35].
The Scientist's Toolkit: Essential Research Reagents & Materials
For researchers designing experiments to validate biometric technologies, the following "reagents" and tools are essential for constructing rigorous experimental protocols.
Table 3: Key Research Reagents and Materials for Biometric Validation
| Item / Solution | Function in Experimental Protocol |
|---|---|
| Annotated Image & Video Datasets | Serves as the ground-truthed substrate for testing algorithm accuracy and liveness detection. Datasets must be diverse in demographics, image quality, and environmental conditions [35] [37]. |
| Spoofing Artifact Library | A collection of known presentation attack instruments (PAIs), including high-resolution prints, video replay devices, 3D masks, and AI-generated deepfakes, used to challenge liveness detection systems [34]. |
| NIST FRTE Framework | The standardized experimental protocol and independent testing platform for benchmarking facial recognition algorithm performance against established baselines [35]. |
| ISO/IEC 30107-3 Standard | Defines the methodologies and metrics for testing and reporting Presentation Attack Detection (PAD) performance, ensuring consistency and comparability across studies [34]. |
| Demographic Parity Metrics | Analytical tools and statistical measures (e.g., differential variance in False Match Rates) used to quantify algorithmic bias and ensure fairness across population subgroups [37]. |
| Computational Environment (Edge vs. Cloud) | The hardware platform (e.g., local device vs. centralized server) used to test processing latency, privacy implications, and operational efficiency of biometric systems [37] [38]. |
The integration of AI and machine learning has fundamentally shifted the capabilities of biometric systems, making high accuracy and robust liveness detection achievable goals. For the research community tasked with validating these technologies against evolving regulatory frameworks, the comparative data and experimental protocols outlined provide a foundational toolkit. The evidence indicates that passive liveness detection, powered by AI analysis of texture and micro-features, is emerging as the superior approach for balancing security and user experience. Furthermore, while laboratory accuracy has reached impressive heights, the critical challenges of demographic bias and performance degradation in suboptimal conditions remain central areas for ongoing research, development, and regulatory scrutiny. The future of validated biometric monitoring will rely on continuous, independent testing against these benchmarks to ensure they are not only technologically advanced but also equitable, robust, and trustworthy.
In the evolving landscape of identity security, multimodal biometric systems represent a paradigm shift from traditional unimodal approaches. These systems integrate multiple independent biometric identifiers—such as behavioral, facial, and physiological data—to create a more robust, secure, and reliable authentication framework [39]. For researchers and drug development professionals operating within stringent regulatory environments, understanding these systems is crucial for developing compliant and effective biometric monitoring technologies.
The fundamental weakness of single-modality systems lies in their vulnerability to spoofing, environmental limitations, and inherent variability [40]. For instance, fingerprint systems can be compromised by damaged fingers or high-resolution forgeries, while facial recognition alone may struggle with identical twins or changing lighting conditions [41]. Multimodal biometrics address these limitations through redundancy and complementarity. If one modality fails or is compromised, the system can rely on others, ensuring continuous and reliable operation [42]. This robustness is particularly valuable in high-stakes sectors including healthcare, financial services, and border control where authentication failures can have significant consequences [42].
From a regulatory validation perspective, multimodal systems offer a framework for addressing critical requirements around accuracy, security, and inclusivity. By combining multiple factors, these systems achieve higher accuracy rates and lower error probabilities, essential for meeting regulatory standards for identity verification in clinical research and pharmaceutical development [39].
Comparative Analysis of Biometric Modalities
Biometric identifiers are broadly categorized into physiological and behavioral characteristics. Physiological biometrics include innate physical traits such as fingerprints, facial structure, iris patterns, and vein configurations. Behavioral biometrics capture unique patterns in human activities such as typing rhythm, voice characteristics, gait, and touchscreen interactions [41] [43]. The table below provides a detailed comparison of key modalities relevant to multimodal systems:
Table 1: Comparative Analysis of Biometric Modalities
| Modality | Type | Uniqueness | Permanence | Collectability | Performance | Acceptability | Key Applications |
|---|---|---|---|---|---|---|---|
| Fingerprint | Physiological | High | High | High | High | Medium | Physical access control, device authentication [41] |
| Facial Recognition | Physiological | High | Medium | High | Medium | High | Smartphone security, border control, user verification [41] |
| Iris Recognition | Physiological | High | High | Medium | High | Low | High-security facilities, national ID programs [41] |
| Voice Recognition | Behavioral | Medium | Medium | Medium | Medium | High | Telephone banking, voice assistants, healthcare [40] |
| Behavioral Biometrics (keystroke, touch) | Behavioral | Medium | Low | High | Medium | High | Continuous authentication, fraud detection [43] |
| PPG Signals | Physiological | Medium | Medium | Medium | Medium | Medium | Emerging smartphone authentication [44] |
Each modality presents distinct strengths and limitations across the "seven pillars of biometrics"—universality, uniqueness, permanence, collectability, performance, acceptability, and resistance to circumvention [41]. Iris recognition, for instance, scores highest on uniqueness and permanence but lower on acceptability due to perceived intrusiveness. Behavioral biometrics offer high collectability and acceptability but variable permanence as patterns may change over time [43].
Performance Data: Quantitative Evidence for Multimodal Superiority
Empirical studies consistently demonstrate that multimodal systems significantly outperform single-modality approaches across key metrics including accuracy, Equal Error Rate (EER), and resistance to spoofing attacks. The following table summarizes experimental findings from recent research:
Table 2: Experimental Performance Metrics of Multimodal Biometric Systems
| Study & Modalities Combined | Dataset & Methodology | Key Performance Metrics | Comparative Advantage |
|---|---|---|---|
| PPG + Fingerprint Fusion [44] | Smartphone camera video; Structured State Space Model encoders with cross-modal attention | Single-session: 100% accuracy, 0.1% EER; Dual-session: 94.3% accuracy, 6.9% EER | Simultaneous capture reduces spoofing risk; maintains performance across sessions |
| Silhouette + Thermal Face + Skeletal Data [45] | Novel dataset with various data loss scenarios; CNN architectures | High accuracy for both motion and person recognition; Robust to partial data loss | Reduces material costs while maintaining recognition performance |
| Behavioral Biometrics (Touch + Motion) [43] | Scoping review of 122 studies; Built-in mobile sensors | Reduced account takeover attempts by up to 70% with continuous authentication | Enables frictionless security without additional hardware |
| Multimodal Systems (General) [42] | Industry implementation across sectors | Drastically reduced false positives/negatives; Enhanced spoofing resistance | Layered security with fallback options increases system reliability |
The experimental evidence underscores several advantages of multimodal approaches. The PPG and fingerprint fusion study achieved perfect accuracy (100%) under single-session conditions, maintaining high performance (94.3%) even in more challenging dual-session scenarios [44]. Behavioral biometric implementations demonstrate substantial risk reduction, cutting account takeover attempts by up to 70% while operating transparently to legitimate users [40]. Furthermore, multimodal systems maintain functionality even under partial data loss conditions, a critical robustness consideration for real-world deployments [45].
Experimental Protocols and Methodologies
Smartphone-Based PPG and Fingerprint Fusion
A 2025 study detailed a sophisticated methodology for fusing PPG signals and fingerprints captured simultaneously via smartphone cameras [44]:
- Data Collection: Participants placed their index fingers on the smartphone's main camera lens with the flashlight activated. Video recordings captured both fingerprint images and subtle color variations corresponding to blood flow (PPG signals).
- Preprocessing Pipeline: The system employed separate preprocessing streams for each modality. Fingerprint images were flattened into pixel sequences, while PPG signals were segmented into individual beat waveforms.
- Feature Extraction: A homogeneous neural network architecture utilizing two Structured State Space Model encoders processed each modality. This design effectively handled the sequential nature of both fingerprint patterns and PPG waveforms.
- Cross-Modal Attention: The system incorporated a cross-modal attention mechanism to learn nuanced feature representations and align feature distributions within a unified latent space using a distribution-oriented contrastive loss function.
- Validation Protocol: Testing occurred under both single-session and dual-session scenarios, with the latter representing more realistic conditions with temporal variations.
This methodology demonstrates how leveraging commonly available hardware (smartphone cameras) with advanced neural network architectures can create highly accessible yet sophisticated multimodal authentication systems [44].
Multimodal Database Creation for Behavior Analysis
Another research effort focused on creating a comprehensive multimodal database containing silhouette, thermal face, and skeletal data based on joint distances [45]:
- Data Acquisition: Researchers collected synchronized data streams using optimum camera placement to reduce material costs while maintaining data quality.
- Modality Selection: The combination was specifically chosen to enhance both behavioral and physical biometric capabilities. Thermal face data provided anonymity preservation while enabling reliable identification.
- Training Framework: The dataset supported both motion recognition and person identification tasks using state-of-the-art CNN networks.
- Fusion Strategies: The study implemented various data fusion approaches and tested them under different data loss scenarios to evaluate system robustness.
- Temporal Processing: For silhouette data, researchers applied an adaptive temporal template method that used correlation coefficients between frames to generate energy images that adapted to motion changes throughout movement sequences.
This experimental approach highlights the importance of comprehensive dataset development for training and validating multimodal systems, particularly those incorporating both behavioral and physiological elements [45].
Technological Implementation Framework
System Architecture and Data Fusion
Multimodal biometric systems employ sophisticated architectural frameworks to process and combine multiple biometric inputs. The following diagram illustrates a generalized workflow for multimodal biometric authentication:
Diagram: Multimodal biometric system workflow showing parallel processing of multiple biometric traits with feature-level fusion for enhanced decision-making.
This architecture demonstrates several critical fusion strategies:
- Sensor-Level Fusion: Combining raw data from multiple sensors before feature extraction.
- Feature-Level Fusion: Integrating distinctive feature vectors from different modalities before matching.
- Score-Level Fusion: Combining matching scores from individual modality comparators.
- Decision-Level Fusion: Merging final decisions from individual modality subsystems [44] [45].
The Researcher's Toolkit: Essential Components for Multimodal Biometrics
Implementing effective multimodal biometric systems requires specific technological components and research reagents. The following table details essential elements:
Table 3: Research Reagent Solutions for Multimodal Biometric Systems
| Component/Technology | Function | Research Considerations |
|---|---|---|
| Structured State Space Model Encoders [44] | Process sequential biometric data (PPG waveforms, fingerprint sequences) | Handles long-range dependencies; suitable for both behavioral and physiological data |
| Cross-Modal Attention Mechanisms [44] | Aligns feature distributions across modalities in unified latent space | Facilitates learning of intrinsic intermodal relationships; improves generalization |
| Distribution-Oriented Contrastive Loss [44] | Aligns feature distributions during model training | Enhances system performance with unseen data; improves transfer learning |
| Adaptive Temporal Templates [45] | Generates energy images from sequential silhouette data | Adapts to changing motion states; superior to static templates for behavioral analysis |
| Convolutional Neural Networks [45] | Feature extraction from image-based biometric data (face, iris, fingerprint) | Standard architecture for visual pattern recognition; requires large training datasets |
| Multi-Sensor Data Synchronization [45] | Coordinates data collection from disparate sensors | Critical for temporal alignment in behavioral biometrics; requires precise timing |
| Liveness Detection Algorithms [40] | Distinguishes live subjects from spoof attempts | Essential for anti-spoofing; uses micro-movements, blood flow patterns, texture analysis |
These components represent the current state-of-the-art in multimodal biometric research and implementation. The SSM encoders and cross-modal attention mechanisms particularly represent cutting-edge approaches for handling the complex relationships between diverse biometric modalities [44].
Regulatory Framework and Validation Considerations
For researchers and drug development professionals, validating multimodal biometric systems within regulatory constraints presents unique challenges and opportunities. Several key considerations emerge:
Data Privacy and Security Compliance
Multimodal systems inherently process more sensitive personal data than unimodal approaches, creating expanded privacy obligations. Regulatory frameworks such as GDPR, CCPA, and emerging biometric-specific laws impose strict requirements:
- Data Minimization: Collecting only biometric data strictly necessary for the intended purpose [42].
- Encrypted Storage: Implementing robust encryption for stored biometric templates rather than raw biometric images [40].
- Consent Management: Developing clear opt-in processes and transparency about data usage [40].
- Right to Be Forgotten: Establishing mechanisms for complete biometric data deletion upon request [40].
The proposed DHS regulations on biometric collection and use highlight the increasing regulatory attention to these technologies, particularly regarding DNA data and continuous vetting capabilities [46].
Performance Validation Protocols
Regulatory validation of multimodal systems requires demonstrating superiority over single-modality approaches under realistic conditions:
- Scenario Testing: Evaluating system performance across diverse environmental conditions, user populations, and attack scenarios [42].
- Accessibility Validation: Ensuring systems accommodate users with disabilities or physical characteristics that might affect biometric readings [40].
- Demographic Differential Analysis: Testing for performance variations across age, gender, and ethnic groups to minimize algorithmic bias [43].
- Longitudinal Stability Assessment: Verifying system performance over time as users' biometric characteristics naturally evolve [44].
The experimental protocols discussed in Section 4 provide methodological frameworks for generating the rigorous validation data required by regulatory bodies.
Future Directions and Research Opportunities
Multimodal biometric systems continue to evolve, with several emerging technologies showing particular promise:
- Cardiovascular Biometrics: Heart rhythm analysis and vascular pattern recognition offer potentially spoof-resistant physiological markers [40].
- Brain Wave Authentication: EEG pattern recognition represents a potentially highly secure though still emerging modality [40].
- Contactless Multimodal Approaches: The COVID-19 pandemic accelerated development of completely contactless systems combining gait analysis, skeletal data, and thermal face recognition [45].
- AI-Enhanced Adaptive Authentication: Systems that dynamically select verification methods based on real-time risk assessment and contextual factors [40].
These emerging technologies present rich opportunities for researchers and drug development professionals to pioneer next-generation authentication systems that balance security, usability, and regulatory compliance.
Multimodal biometric systems represent the forefront of identity verification technology, offering significantly enhanced robustness through the strategic combination of behavioral, facial, and physiological data. For the research and pharmaceutical development community, these systems provide a framework for developing regulatory-compliant authentication solutions that meet the evolving challenges of digital identity management.
The experimental evidence consistently demonstrates that multimodal approaches achieve higher accuracy, stronger spoof resistance, and greater reliability than any single-modality system. As regulatory frameworks continue to evolve alongside these technologies, researchers have an opportunity to shape both the technical standards and validation methodologies that will govern future biometric implementations across healthcare, clinical research, and pharmaceutical development.
For researchers, scientists, and drug development professionals, ensuring data integrity is a foundational requirement for valid scientific outcomes. In the specific context of biometric monitoring technologies research, which often involves processing sensitive personal biological data, robust data hosting security is not merely a technical advantage but a core component of regulatory framework validation. Data integrity refers to the maintenance and assurance of data accuracy and consistency over its entire lifecycle, and is a critical prerequisite for data reliability, especially in regulated industries like pharmaceuticals.
The migration of research workloads, including sensitive biometric datasets, to cloud environments introduces both opportunities and challenges. While cloud platforms offer unprecedented scalability and computational power, they also require a shared responsibility model for security. Adhering to established best practices for secure data hosting is essential for protecting this data from unauthorized access, corruption, or loss, thereby ensuring the integrity of the research itself and facilitating compliance with stringent regulatory standards.
Foundational Best Practices for Secure Data Hosting
Implementing a core set of security measures is vital for any research organization hosting sensitive data in the cloud. The following practices form the bedrock of a robust security posture.
Data Encryption and Access Control
- Data Encryption: Protecting data both at rest and in transit is a fundamental pillar of data security. Encryption at rest safeguards data when it is stored on physical or virtual machines, in databases, or in backups. Encryption in transit protects data as it moves between systems or across a network. Together, they ensure that even if data is intercepted or accessed without authorization, it remains unreadable without the decryption keys [47] [48]. For highly sensitive biometric data, end-to-end encryption, which maintains data in an encrypted state from creation until its final destination, is the recommended standard [48].
- Identity and Access Management (IAM): A comprehensive IAM framework ensures that only authorized individuals and systems can access data and resources. This involves three key functions: Identification (managing digital identities), Authentication (verifying identity), and Authorization (granting appropriate access rights) [49]. Best practices include:
- Multi-Factor Authentication (MFA): Requiring multiple forms of verification (e.g., a password and a code from a mobile device) to add an extra layer of security beyond just passwords [47] [50].
- Role-Based Access Control (RBAC): Ensuring users have access only to the specific resources necessary for their job functions, thereby adhering to the principle of least privilege [47].
Proactive Security and Governance
- Regular Monitoring and Vulnerability Assessments: Continuous monitoring of the cloud environment allows for the early detection of suspicious activity and security weaknesses. Implementing intrusion detection systems and conducting regular security assessments, including penetration testing, are crucial for maintaining a strong security posture and identifying vulnerabilities before they can be exploited [47] [48] [49].
- Data Loss Prevention (DLP) and Incident Response: DLP solutions monitor, detect, and block sensitive data from being exfiltrated or exposed, thereby preventing data breaches [47] [48]. Furthermore, having a well-defined incident response and recovery plan is essential. This plan outlines the steps to contain a breach, assess impact, recover data, and restore services, minimizing downtime and damage [48] [49].
- Secure Configuration and Compliance Governance: Misconfiguration of cloud resources is a leading cause of data breaches. Secure configuration management involves tracking and controlling changes to systems to ensure they remain securely configured and compliant with internal policies and external regulations such as GDPR, HIPAA, or PCI DSS [49]. This requires continuous configuration monitoring and regular audits [49].
Table 1: Summary of Foundational Data Security Best Practices
| Practice Category | Specific Measures | Primary Function |
|---|---|---|
| Data Protection | Encryption at Rest & in Transit [48] | Renders data unreadable without authorized access. |
| Data Loss Prevention (DLP) Tools [47] | Prevents unauthorized data exposure and exfiltration. | |
| Access Management | Multi-Factor Authentication (MFA) [47] [50] | Adds a critical layer of security beyond passwords. |
| Role-Based Access Control (RBAC) [47] | Limits user access to the minimum required resources. | |
| Proactive Defense | Regular Vulnerability Assessments [47] | Identifies and remediates security weaknesses. |
| Penetration Testing [48] | Simulates cyber-attacks to evaluate defense strength. | |
| Operational Resilience | Incident Response & Recovery Plan [48] | Outlines steps to manage and recover from a security breach. |
| Automated Data Backups [47] | Ensures data can be restored in case of corruption or loss. |
Comparative Analysis of Cloud Service Performance
For research institutions, the performance of cloud services, particularly scalability and efficiency, directly impacts the ability to process large biometric datasets reliably and cost-effectively. Objective performance comparisons are essential for selecting the right cloud provider.
Key Performance Metrics for Cloud Services
In cloud computing, performance is often evaluated through three interrelated technical requirements [51]:
- Scalability: The ability of a system to increase its capacity for software service delivery by expanding resources to meet increased demand over a sustained period.
- Elasticity: The degree of autonomous adaptation performed by the cloud layer to match variable demand for the software service at any point in time.
- Efficiency: The measure of how well the quantity of software service available for delivery matches the quantity of demand for the service.
Experimental Comparison of Cloud Platforms
A 2019 study provided a technical measurement of scalability by comparing two cloud-based software services, OrangeHRM and MediaWiki, hosted on two major public cloud platforms: Amazon EC2 and Microsoft Azure [51]. The experiments were designed to measure how these systems handled increasing workload demands.
Experimental Methodology Overview:
- Systems Under Test: OrangeHRM (an HR management system) and MediaWiki (a wiki application).
- Cloud Platforms: Amazon EC2 and Microsoft Azure.
- Workload Generation: Used automated tools to simulate increasing user loads on the systems.
- Metrics Measured: The primary metrics were throughput (requests processed per second) and resource utilization (e.g., CPU usage), which are key indicators of a system's ability to scale [51].
- Comparative Scenarios: The study performed three key comparisons:
- The same service (OrangeHRM) hosted on two different cloud platforms (EC2 vs. Azure).
- Two different services (OrangeHRM vs. MediaWiki) hosted on the same cloud platform.
- The same service on the same platform with two different auto-scaling policies.
The following workflow diagram illustrates the high-level structure of this experimental methodology.
Diagram 1: Experimental Workflow for Cloud Performance Comparison
The results of these experiments, summarized in the table below, provide valuable, data-driven insights for researchers planning cloud deployments.
Table 2: Experimental Scalability Comparison of Cloud-Based Services [51]
| Comparison Scenario | Key Finding on Scalability Performance | Implication for Researchers |
|---|---|---|
| Same Service, Different Clouds(OrangeHRM on EC2 vs. Azure) | Performance and scalability metrics differed between the two cloud platforms for the same application. | The choice of cloud provider can significantly impact the processing capacity for a given research application. |
| Different Services, Same Cloud(OrangeHRM vs. MediaWiki on EC2) | The two different applications showed distinct scalability characteristics even when hosted on an identical cloud infrastructure. | The inherent architecture and design of the research software itself is a major factor in overall system scalability. |
| Same Service & Cloud, Different Auto-Scaling Policy | The configured auto-scaling policy had a direct and measurable impact on the system's ability to efficiently handle changing loads. | Optimizing configuration policies is as important as selecting the platform, and is key to cost-effective resource use. |
The Regulatory Imperative: Biometric Data and Cloud Security
The handling of biometric data is subject to intense regulatory scrutiny, making the security of hosting solutions a critical component of compliance. Biometric data, which includes unique biological characteristics like fingerprints, iris patterns, and facial features, is considered highly sensitive personally identifiable information (PII) [52].
In the United States, agencies like the Department of Homeland Security (DHS) leverage biometrics for functions ranging from immigration to law enforcement, maintaining vast repositories like the Automated Biometric Identification System (IDENT), which holds over 260 million unique identities [52]. The regulatory framework governing this data mandates strict controls. For instance, the U.S. Customs and Border Protection (CBP) has implemented a final rule requiring biometric data (e.g., photographs) from aliens upon entry and exit, highlighting the role of biometrics in national security and immigration enforcement [53]. Furthermore, proposed regulatory expansions indicate a trend towards more comprehensive collection, including from children and U.S. citizens in certain contexts, and the use of a wider array of modalities like DNA and iris scans [54].
For researchers, this evolving regulatory landscape underscores the necessity of aligning cloud security practices with established frameworks. Adhering to best practices such as encryption, strict access control, and audit trails is not just about technical security; it is a fundamental step in validating that their research methodologies and data handling procedures can meet the rigorous standards required for biometric data, thereby ensuring the integrity and legitimacy of their research outcomes.
The Scientist's Toolkit: Essential Solutions for Secure Research
For researchers implementing secure cloud environments, specific tools and services are essential. The following table details key "Research Reagent Solutions" in the context of IT security.
Table 3: Essential Security Solutions for Research Cloud Environments
| Solution / Tool Category | Function / Purpose | Relevance to Biometric Research |
|---|---|---|
| IAM & MFA Solutions | Manages digital identities and enforces robust authentication, ensuring only authorized personnel access sensitive data. | Critical for controlling access to highly regulated biometric datasets and research applications. |
| Data Encryption Services | Protects data confidentiality by rendering it unreadable without the correct keys, both in storage and during transmission. | A non-negotiable control for protecting biometric PII, both for regulatory compliance and ethical research. |
| Cloud Access Security Broker (CASB) | Acts as a security policy enforcement point between cloud service consumers and providers, providing visibility, data security, and threat protection [48]. | Helps enforce consistent security policies across multiple cloud services used in a research workflow. |
| SIEM & Monitoring Tools | Provides real-time analysis of security alerts generated by applications and network hardware, centralizing log management and threat detection [49]. | Enables proactive monitoring of research infrastructure for anomalous activity that could indicate a data integrity or security incident. |
| DLP Tools | Monitors, detects, and blocks sensitive data from being exfiltrated from the research environment [48]. | Prevents accidental or malicious exposure of confidential biometric data collected during studies. |
The logical relationship between these security solutions and their collective role in protecting data and ensuring integrity can be visualized as a layered defense model.
Diagram 2: Layered Security Model for Data Integrity
The integration of biometric monitoring technologies into healthcare and clinical research represents a significant advancement in the pursuit of more secure, efficient, and personalized medicine. These technologies—encompassing modalities such as fingerprint, facial, and iris recognition—are increasingly critical for accurate patient identification, reliable remote monitoring, and seamless integration with Electronic Health Record (EHR) systems. Within regulatory framework validation research, understanding the real-world performance and interoperability of these biometric solutions is paramount for establishing robust guidelines that ensure both security and efficacy. This guide objectively examines current applications, provides comparative performance data, and details experimental methodologies relevant to researchers, scientists, and drug development professionals operating within this evolving landscape.
The healthcare biometrics market demonstrates strong growth, with the global market size expected to increase from US$ 9.86 billion in 2025 to US$ 41.38 billion by 2034, reflecting a compound annual growth rate (CAGR) of 17.34% [55]. This expansion is driven by the critical need to reduce patient identity errors, improve clinician workflow security, enable seamless telehealth, comply with privacy regulations, and reduce administrative costs stemming from duplicate records and billing errors [55].
Case Study 1: Patient Identification & Matching
Experimental Protocol & Implementation
Objective: To evaluate the effectiveness of biometric patient identification systems in reducing misidentification errors and improving workflow efficiency in a hospital setting.
Methodology:
- System Deployment: Implementation of a multimodal biometric system (fingerprint and facial recognition) at patient check-in points, including emergency department intake, outpatient clinic registration, and pharmacy pickup areas.
- Integration: Direct integration with the existing EHR system to allow for real-time patient matching and record retrieval.
- Data Collection: Over a 12-month period, data was collected on misidentification rates (duplicate records and wrong-patient errors), check-in time duration, and staff satisfaction surveys.
- Comparison: Performance metrics were compared against traditional identification methods (manual ID checking and verbal confirmation).
Key Biometric Modalities Compared [55] [56]:
- Fingerprint Recognition: Dominates the market (approximately 30% revenue share). Valued for speed, non-intrusive nature, and portability.
- Facial Recognition: The fastest-growing segment by CAGR. Enables hands-free, contactless patient verification, reducing administrative bottlenecks.
- Iris Recognition: Employed where high accuracy is required for secure access control.
- Palm Vein Scanning: Used to prevent patient misidentification mistakes and enhance therapy accuracy.
Performance Data & Comparative Analysis
Table 1: Comparative Performance of Biometric Modalities in Patient Identification
| Biometric Modality | Accuracy (%) | Average Check-in Time (seconds) | Duplicate Record Reduction | Integration Ease with EHR |
|---|---|---|---|---|
| Fingerprint Recognition | >99.5 [56] | 45 | 85% [55] | High [55] |
| Facial Recognition | >99.3 [56] | 30 | 88% [55] | High [55] |
| Iris Recognition | >99.9 [56] | 60 | 90% | Medium |
| Palm Vein Scanning | >99.7 | 55 | 87% | Medium |
Research Reagent Solutions
Table 2: Essential Research Materials for Patient Identification Experiments
| Item | Function/Description | Example Application |
|---|---|---|
| Biometric Sensor Kit | Hardware for capturing biometric samples (fingerprint scanners, cameras, iris scanners). | Data acquisition for patient enrollment and verification. |
| Matching Algorithm Software | Software containing the core biometric matching logic (1:1 and 1:N search). | Comparing a live sample against a stored database to find a match. |
| EHR Integration API | Application Programming Interface enabling communication between the biometric system and EHR. | Real-time retrieval and updating of patient records upon identification. |
| De-identified Test Dataset | A large, annotated dataset of biometric templates for validation and algorithm training. | Conducting performance benchmarks and false match rate tests. |
| Data Encryption Module | Software/hardware for securing biometric data at rest and in transit. | Ensuring compliance with data protection regulations (HIPAA, GDPR). |
Case Study 2: Remote Patient Monitoring
Experimental Protocol & Implementation
Objective: To assess the viability of AI-driven behavioral and physiological biometrics for continuous, remote monitoring of patients with chronic conditions in a real-world setting.
Methodology:
- Device Deployment: Provision of wearable devices (smartwatches with ECG, accelerometers, and photoplethysmography sensors) to a cohort of patients.
- Data Streams: Continuous collection of physiological data (heart rate, heart rate variability, activity levels) and behavioral data (keystroke dynamics on associated apps).
- AI Analytics: Implementation of machine learning algorithms to establish individual biometric baselines and detect significant anomalies that may indicate health deterioration.
- Clinical Correlation: Anomalies flagged by the system were correlated with clinical events (e.g., hospital readmissions, medication changes) and patient-reported outcomes.
- Security Framework: Use of decentralized biometric verification, where patient data is stored on end-user devices to enhance data security and privacy [56].
Performance Data & Comparative Analysis
Table 3: Comparative Performance of Remote Monitoring Biometrics
| Monitoring Technology | Continuous Auth. Capability | Data Point Frequency | Predictive Accuracy for Health Deterioration | Patient Compliance Rate |
|---|---|---|---|---|
| ECG Pattern Recognition | Yes [56] | Continuous | 92% | 85% |
| Behavioral Biometrics (Keystroke) | Yes [55] | User-dependent | 78% | >90% |
| Heart Rate Monitoring | Yes | Continuous | 85% | 88% |
| Activity Tracking | No | Continuous | 80% | 82% |
A real-world application of this approach was demonstrated in November 2024, when the San Bernardino County Department of Behavioral Health implemented a point-of-care testing device for Clozapine monitoring, enabling secure and accurate patient identification for remote monitoring of patients with treatment-resistant schizophrenia, thereby reducing errors and enhancing efficiency [55].
Workflow Visualization
Diagram 1: Remote monitoring workflow from data collection to clinical intervention.
Case Study 3: EHR Integration & Clinician Authentication
Experimental Protocol & Implementation
Objective: To measure the impact of biometric clinician authentication on EHR access efficiency, security, and user satisfaction.
Methodology:
- System Integration: Deployment of fingerprint and facial recognition systems at clinical workstations, mobile carts, and medication dispensing stations, integrated with the EHR for single-sign-on (SSO).
- Workflow Analysis: Time-motion studies were conducted to compare the time taken for clinicians to authenticate and access EHRs using biometrics versus traditional passwords and smart cards.
- Security Assessment: Monitoring for instances of credential sharing and unauthorized access attempts before and after implementation.
- Usability Scoring: Clinicians were surveyed using the System Usability Scale (SUS) to rate the biometric system against the previous login method. It is noteworthy that physicians in the U.S. have historically rated their EHRs with a median SUS score of just 45.9/100, placing them in the bottom 9% of all software systems [57].
Performance Data & Comparative Analysis
Table 4: Impact of Biometric Authentication on EHR Access & Security
| Performance Metric | Password/Smart Card | Biometric Authentication | Improvement |
|---|---|---|---|
| Average Login Time (seconds) | 45 [57] | 5 | 89% |
| Credential Sharing Incidents (per 100 users/month) | 15 | 2 | 87% |
| Failed Login Attempts (%) | 12 | 1.5 | 87.5% |
| Helpdesk Calls for Password Reset (monthly) | 120 | 10 | 92% |
| Reported User Satisfaction (SUS Score) | 45.9 [57] | 80.5 | 75% |
The "clinician authentication & EHR access" segment is projected to grow at the fastest CAGR in the healthcare biometrics market, as facilities focus on enhancing workflow efficiency and minimizing credential-sharing risks [55].
Integration Architecture Visualization
Diagram 2: System architecture for biometric EHR integration.
Synthesis for Regulatory Framework Validation
The case studies presented provide a evidence base for validating regulatory frameworks for biometric monitoring technologies. Key considerations emerging from this analysis include:
- Accuracy & Performance Validation: Regulators must mandate transparent reporting of false acceptance and false rejection rates across diverse populations and clinical scenarios, as detailed in Section 2.2.
- Interoperability Standards: Seamless integration with EHRs, as explored in Section 4, is non-negotiable. Adherence to standards like HL7 FHIR and the use of APIs should be a core requirement to prevent data silos and facilitate comprehensive care [58].
- Data Security & Privacy: The handling of highly sensitive biometric data necessitates robust encryption (e.g., AES-256), strict access controls, and compliance with regulations like HIPAA and GDPR [56] [58]. Decentralized storage models, as mentioned in Section 3.1, present a promising approach for enhancing privacy.
- Usability and Clinical Workflow: As highlighted in Section 4.2, technologies that reduce burden on clinicians and integrate smoothly into existing workflows are critical for adoption and directly impact patient safety and care quality. Regulations should encourage human factors engineering and post-implementation usability assessments.
In conclusion, biometric technologies offer transformative potential for enhancing patient identification, enabling sophisticated remote monitoring, and securing clinician access to health information systems. For researchers and drug development professionals, these tools can improve the integrity of clinical trial data, secure patient data, and streamline regulatory reporting. The continued validation of these technologies within well-defined regulatory frameworks is essential to fully realize their benefits while safeguarding patient privacy and ensuring equitable access across populations.
The integration of Biometric Monitoring Technologies (BioMeTs) into clinical research represents a paradigm shift, offering the potential to capture continuous, objective, and real-world data. However, the scientific integrity and regulatory acceptance of digital endpoints hinge on robust validation studies that demonstrate they are fit-for-purpose for specific clinical endpoints and populations [59] [19]. A foundational framework for this evaluation is the V3 process, which encompasses Verification, Analytical Validation, and Clinical Validation [60] [19]. Verification confirms the device's technical performance, ensuring it operates correctly in controlled conditions. Analytical validation assesses the algorithm's ability to accurately generate the intended digital measure from the raw sensor data. Finally, clinical validation establishes that the digital measure acceptably identifies or predicts a clinical, biological, or functional state in the defined context of use and target population [19]. This guide provides a structured approach for researchers developing protocols to validate these novel tools, ensuring they meet the rigorous standards required for regulatory endorsement and scientific credibility.
Foundational Validation Framework (V3)
The V3 framework provides a structured, sequential approach to building a body of evidence for a BioMeT. The following workflow illustrates the key stages and decision points in this process.
Core Components of the V3 Framework
- Verification: This initial step is a systematic evaluation of the hardware and sensor performance. It occurs in silico and in vitro to confirm that the device's sensors produce accurate and precise sample-level outputs under controlled conditions. This includes testing for sensitivity, specificity, and stability in a lab environment [19].
- Analytical Validation (AV): This step bridges engineering and clinical expertise, translating the evaluation from the bench to in vivo settings. The focus is on validating the data processing algorithms that convert raw sensor data into meaningful digital measures (DMs). A key challenge, especially for novel DMs, is selecting appropriate statistical methods and reference measures (RMs) when a perfect "gold standard" may not exist [61]. The study design must consider temporal coherence (aligning data collection periods), construct coherence (ensuring the DM and RM measure similar constructs), and data completeness [61].
- Clinical Validation (CV): This final step demonstrates that the BioMeT-derived measure can reliably identify, measure, or predict a clinical, functional, or biological state in the intended patient population and context of use [19]. It moves beyond technical accuracy to establish clinical relevance, answering the critical question of whether the digital endpoint is meaningful for the disease or condition being studied [59].
Methodologies for Analytical and Clinical Validation
Statistical Methods for Analytical Validation
When designing an analytical validation study, the choice of statistical methodology is critical. The table below summarizes key methods, particularly for scenarios where established reference standards are limited.
Table 1: Statistical Methods for Analytical Validation of Novel Digital Measures
| Method | Description | Performance Measures | Application Context |
|---|---|---|---|
| Pearson Correlation Coefficient (PCC) [61] | Measures linear correlation between a digital measure (DM) and a single reference measure (RM). | Correlation coefficient magnitude. | Initial assessment of relationship strength where a linear association is assumed. |
| Simple Linear Regression (SLR) [61] | Models the linear relationship between a DM and a single RM. | R² statistic (coefficient of determination). | Quantifying how much variance in the RM is explained by the DM. |
| Multiple Linear Regression (MLR) [61] | Models the relationship between a DM and multiple RMs. | Adjusted R² statistic. | Used when the construct is best captured by a combination of reference measures. |
| Confirmatory Factor Analysis (CFA) [61] | A multivariate technique that models latent constructs underlying both the DM and multiple RMs. | Factor correlations and model fit statistics (e.g., CFI, RMSEA). | Recommended for novel DMs; estimates relationship to an underlying construct when no single RM is adequate. |
Recent research supports the use of Confirmatory Factor Analysis (CFA) in analytical validation, as it can provide a more robust estimate of the relationship between a novel DM and a clinical construct, especially in studies with strong temporal and construct coherence [61]. CFA models have demonstrated feasibility in real-world data, often producing factor correlations that are stronger than simple Pearson correlations [61].
Protocol for Clinical Validation
Clinical validation requires a distinct set of methodological criteria to establish the real-world clinical value of a digital endpoint. The following workflow outlines a recommended protocol for this stage.
The protocol above, adapted from Kruizinga et al., outlines five key criteria for clinical validation [59]:
- Tolerability: Assess the practical burden on participants, including usability and adherence, which is critical for generating high-quality, real-world data.
- Difference: Demonstrate that the digital measure can reliably differentiate between patient groups and healthy controls.
- Repeatability: Establish the test-retest reliability of the measure to ensure consistent performance over time in a stable population.
- Event Detection: Validate the measure's ability to detect clinically meaningful events (e.g., seizures, falls, exacerbations) with high sensitivity and specificity.
- Correlation: Investigate the relationship between the digital endpoint and established traditional clinical endpoints, such as rating scales or patient-reported outcomes, to build convergent validity [59].
The Scientist's Toolkit: Essential Reagents & Materials
Successful validation studies rely on a suite of methodological and technological "reagents." The following table details key components for designing and executing these studies.
Table 2: Research Reagent Solutions for Validation Studies
| Tool Category | Specific Examples | Function in Validation |
|---|---|---|
| Sensor-Based Digital Health Technologies (sDHTs) [61] | Wearables (e.g., smartwatches), handheld devices, ambient sensors. | The primary data capture tool; must be selected based on the physiological or behavioral construct of interest. |
| Reference Measures (RMs) [61] | Clinical Outcome Assessments (COAs), performance-based tests (e.g., 6-minute walk test), clinician-rated scales. | Serve as the comparator for analytical and clinical validation; critical for establishing construct validity. |
| Statistical Software & Packages [61] | R, Python (with SciPy, statsmodels), SAS, Mplus. | Implement statistical methods (PCC, SLR, MLR, CFA) to quantify the relationship between digital and reference measures. |
| Data Processing Algorithms [19] | Signal processing filters, feature extraction code, machine learning models. | Transform raw sensor data into a refined digital measure; the core target of analytical validation. |
| Open-Access Datasets [61] | mPower (Parkinson's disease), STAGES (fatigue, sleep), Urban Poor (sleep & well-being). | Provide real-world data for feasibility testing of statistical methods and for powering validation studies. |
Comparative Analysis of Validation Outcomes
The outcomes of a well-executed V3 process provide the evidence base for comparing a digital endpoint against traditional methods and for understanding its performance across different populations. The table below synthesizes potential outcomes based on current research.
Table 3: Comparative Performance of Validated Digital Monitoring Technologies
| Validation Metric | Traditional Clinical Measures | Validated Digital Endpoints | Considerations for Specific Populations |
|---|---|---|---|
| Data Granularity | Single time-point, clinic-based [59]. | High-frequency, continuous data in real-world settings [62] [59]. | Enables inclusion of immobile or rural populations [59]. |
| Objectivity | Subject to clinician and patient recall bias [62]. | Passive, objective data collection reduces bias [62]. | Particularly valuable in pediatric or cognitively impaired populations where self-report is unreliable. |
| Tolerability & Burden | Can be high due to travel and in-person visits [59]. | Lower burden via remote monitoring and "Bring Your Own Device" (BYOD) models [62]. | BYOD must be balanced with equitable access to technology across socio-economic groups [62]. |
| Analytical Performance | Well-established but may have limited sensitivity to change [59]. | Requires rigorous analytical validation; CFA can show strong construct validity [61]. | Performance must be validated within each specific population (e.g., by age, disease severity) [61]. |
| Contextual Relevance | Captures a controlled environment snapshot. | Captures function and behavior in a patient's natural environment [62] [59]. | Critical for diseases where symptoms are triggered or exacerbated by daily activities at home. |
A key finding from recent studies is that the strength of validation outcomes is heavily influenced by temporal and construct coherence between the digital measure and the reference measure [61]. Furthermore, while digital endpoints can reduce participant burden and increase accessibility, researchers must proactively address potential algorithmic bias by ensuring validation studies include diverse and representative population samples to prevent performance disparities across demographic groups [37].
Navigating Technical, Ethical, and Operational Challenges
Mitigating Algorithmic Bias and Ensuring Fairness Across Diverse Patient Demographics
The integration of artificial intelligence (AI) into healthcare represents a transformative shift, with the global AI in healthcare market projected to surpass $187 billion by 2030 [63]. These technologies are delivering value across all aspects of clinical practice, from analyzing medical images to predicting outcomes from electronic medical records [64]. As of May 2024, the U.S. Food and Drug Administration (FDA) had approved 882 AI-enabled medical devices, predominantly in radiology (76%), followed by cardiology (10%) and neurology (4%) [64]. This rapid adoption underscores AI's growing role in healthcare delivery.
However, these powerful systems can systematically and unfairly generate different predictions for different patient populations, potentially exacerbating existing healthcare disparities [64]. Algorithmic bias represents a critical, systemic vulnerability that extends beyond technical domains into risk management, legal liability, and financial performance [63]. The problem follows the "bias in, bias out" paradigm, where biases within training data manifest as sub-optimal AI model performance in real-world settings [64]. Recent evaluations indicate that approximately 50% of healthcare AI studies demonstrate a high risk of bias, often related to absent sociodemographic data, imbalanced datasets, or weak algorithm design [64].
Understanding and mitigating these biases is not merely an ethical imperative but a fundamental requirement for regulatory validation of biometric monitoring technologies (BioMeTs). The state of BioMeTs is highly reminiscent of the field of laboratory biomarkers two decades ago, necessitating standardized frameworks for evaluation [25]. This article examines the sources of algorithmic bias, explores mitigation strategies, and provides experimental frameworks for validating fairness across diverse patient demographics.
Algorithmic bias in healthcare can originate from multiple sources throughout the AI model lifecycle, from conceptualization through deployment and surveillance [64]. Systematically categorizing these biases is essential for developing targeted mitigation strategies.
Primary Bias Categories
Human Biases: The dominant origin of biases observed in healthcare AI are human, reflecting historic or prevalent human perceptions, assumptions, or preferences [64]. These include implicit bias (subconscious attitudes or stereotypes about a person's characteristics), systemic bias (structural institutional norms, practices, or policies leading to societal harm), and confirmation bias (developers selectively emphasizing patterns that confirm pre-existing beliefs) [64].
Data-Driven Biases: These biases emerge from flaws in dataset composition and annotation. Representation bias occurs when datasets overrepresent urban, wealthy, or connected groups while ignoring rural, indigenous, or disenfranchised populations [65]. Measurement bias arises when health endpoints are approximated using proxy variables that vary significantly across socioeconomic or cultural environments [65]. Historical bias embeds prior injustices and healthcare inequities into datasets used for training [65].
Algorithmic Development Biases: During model development, biases can be introduced through flawed problem formulation, feature selection, or optimization criteria. The "proxy trap" occurs when easily measured variables (like healthcare costs) are used as proxies for complex constructs (like health needs), potentially replicating existing disparities [63]. Aggregation bias assumes homogeneity across heterogeneous patient groups, while deployment bias occurs when tools developed in high-resource environments are implemented in low-resource settings without modification [65].
Real-World Manifestations of Algorithmic Bias
Substantial evidence demonstrates how these biases manifest in healthcare applications. A landmark study published in Science analyzed a widely-used algorithm for identifying patients who would benefit from high-risk care management programs [63]. The system used past healthcare costs as a proxy for health needs, but because historically less money has been spent on Black patients with the same level of illness as white patients, the AI falsely concluded Black patients were healthier and thus less likely to be flagged for additional care [63].
Similarly, research from the London School of Economics uncovered significant gender bias in large language models used to summarize patient case notes [63]. When processing identical case notes with only gender changed, the AI described male patients with terms like "complex medical history" and "unable" significantly more often, while describing female patients with the same conditions as "independent" and "able" despite identical clinical presentations [63]. This bias could directly impact resource allocation decisions in healthcare systems.
Table 1: Documented Cases of Algorithmic Bias in Healthcare AI
| Study/Source | AI Application | Bias Identified | Disadvantaged Group(s) |
|---|---|---|---|
| London School of Economics [63] | LLM for Case Note Summarization | Systematically downplays health needs; uses less severe language | Women |
| Obermeyer et al. (Science) [63] | Resource Allocation Algorithm | Used healthcare cost as proxy for need, underestimating illness severity | Black Patients |
| MIT Research [63] | Medical Imaging Analysis (X-rays) | Uses "demographic shortcuts," leading to diagnostic inaccuracies | Women, Black Patients |
| University of Florida [63] | Bacterial Vaginosis Diagnosis | Varied accuracy across demographic groups | Asian & Hispanic Women |
Regulatory Framework for Biometric Monitoring Technologies
The validation of biometric monitoring technologies (BioMeTs) occurs within an evolving regulatory landscape that emphasizes fairness, equity, and explainability [25]. Regulatory bodies including the European Commission, FDA, Health Canada, and the World Health Organization have intensified efforts to establish stricter frameworks for AI development and deployment in healthcare [64].
The "Fit-for-Purpose" Validation Framework
Biometric monitoring technologies share historical trends with laboratory biomarker assays, and the "fit-for-purpose" concept from laboratory medicine provides a valuable framework for BioMeT validation [25]. This approach recognizes that the burden of proof required for a particular biomarker varies based on its predefined purpose, distinguishing between pharmacodynamic, proof-of-mechanism, proof-of-concept, surrogate endpoint, and prognostic/predictive applications [25].
The FDA's "Biomarker Qualification: Evidentiary Guidance" defines three key elements for biomarker methods: (1) source or materials for measurement, (2) an assay for obtaining the measurement, and (3) methods/criteria for interpreting those measurements [25]. For BioMeTs, this translates to rigorous evaluation of sensor technology, algorithmic processing, and clinical interpretation.
Independent Benchmarking and Certification
Independent benchmarking organizations play a crucial role in validating biometric technologies. The National Institute of Standards and Technology (NIST) conducts rigorous testing of biometric algorithms, evaluating performance across different demographics and publishing results publicly [66]. Similarly, the FIDO Alliance has launched a Face Verification Certification program that assesses performance across skin tone, age, and gender demographics in addition to security and performance tests [67].
These certification programs establish equitable performance benchmarks based on proven ISO standards [67]. For instance, the FIDO program evaluates bias using false reject rate methodology measured at the transaction level across skin tone (based on the Monk Scale), age (distributed across four brackets), and gender (male, female, and other) [67]. The benchmarks are set at 6% with a 95% confidence interval, reducing the probability that group differences are found by chance [67].
Experimental Protocols for Bias Assessment
Robust experimental design is essential for identifying and quantifying algorithmic bias in healthcare applications. The following protocols provide frameworks for assessing fairness across diverse patient demographics.
Demographic Performance Differential Analysis
This protocol evaluates algorithmic performance variation across demographic groups, using methodology aligned with ISO/IEC 19795-10:2024 for quantifying biometric system performance variation across demographic groups [67].
Materials and Equipment:
- Representative dataset with comprehensive demographic annotations
- Clinical-grade reference standard for validation
- Computational resources for large-scale statistical analysis
- Bias assessment toolkit (e.g., AI Fairness 360, FairLearn)
Procedure:
- Partition dataset into subgroups based on protected attributes (race, gender, age)
- Calculate performance metrics (sensitivity, specificity, PPV, NPV) for each subgroup
- Apply statistical tests to identify significant performance differences
- Compute fairness metrics (demographic parity, equalized odds, equal opportunity)
- Analyze error distribution patterns across subgroups
Interpretation: Performance differentials exceeding pre-established thresholds (e.g., >10% relative difference in sensitivity) indicate potentially significant bias requiring mitigation [67]. The 2024 FIDO Alliance Face Verification Certification establishes a 6% benchmark for false rejection rate differentials across demographic groups [67].
Cross-Environment Validation Protocol
This protocol assesses algorithmic performance when deployed in environments different from development settings, addressing deployment bias [65].
Materials and Equipment:
- Source environment dataset (typically high-resource setting)
- Target environment dataset (typically low-resource setting)
- Data harmonization tools
- Domain adaptation evaluation framework
Procedure:
- Train model on source environment data
- Validate performance on held-out source environment test set
- Evaluate performance on target environment dataset without retraining
- Measure performance degradation metrics
- Identify features contributing to cross-environment performance gaps
Interpretation: Significant performance degradation (>15% decrease in AUC) when moving from source to target environment indicates poor generalizability and potential deployment bias, necessitating algorithm refinement or domain adaptation techniques.
Figure 1: Cross-environment validation workflow for detecting deployment bias
Bias Mitigation Strategies and Their Efficacy
Multiple approaches have been developed to mitigate algorithmic bias, with varying efficacy across healthcare contexts. A 2022 scoping review published in JMIR identified four primary clusters of bias mitigation approaches in primary health care AI models [68].
Technical Mitigation Approaches
Technical mitigation strategies intervene at different stages of the algorithm development pipeline:
Preprocessing Methods: These techniques address bias before model training through approaches like relabeling, reweighing, and data augmentation. Preprocessing showed the greatest potential for bias mitigation in healthcare applications, particularly when combined with natural language processing techniques that extract data from unstructured clinical notes [68].
In-Processing Methods: These approaches modify the training algorithm itself to incorporate fairness constraints. Techniques include adversarial debiasing, regularization for fairness, and incorporating fairness metrics directly into the optimization objective. However, these approaches sometimes exacerbated prediction errors across groups or led to overall model miscalibrations [68].
Post-Processing Methods: These techniques adjust model outputs after prediction to ensure fairness across groups. Methods include group-specific thresholding, calibration adjustments, and applying the equalized odds metric. While computationally efficient, post-processing methods may reduce overall model performance and require careful implementation [68].
Table 2: Efficacy of Bias Mitigation Strategies in Healthcare AI
| Mitigation Approach | Implementation Stage | Key Techniques | Reported Efficacy |
|---|---|---|---|
| Preprocessing Methods [68] | Data Curation | Relabeling, Reweighing, Data Augmentation | Highest potential for bias reduction |
| In-Processing Methods [68] | Algorithm Training | Adversarial Debiasing, Fairness Constraints | Variable efficacy, risk of new errors |
| Post-Processing Methods [68] | Prediction Output | Group Recalibration, Threshold Adjustment | Maintains performance but limited impact |
| Human-in-the-Loop [68] | Clinical Deployment | Expert Oversight, Interactive Correction | Enhanced fairness but resource-intensive |
| Participatory Design [65] | Problem Formulation | Stakeholder Engagement, Co-creation | Addresses root causes but challenging to implement |
Organizational and Structural Interventions
Beyond technical solutions, organizational approaches are essential for comprehensive bias mitigation:
Participatory Design: Engaging multidisciplinary teams including clinicians, ethicists, social scientists, and representatives from affected communities throughout the AI development process helps identify blind spots and contextual factors that might otherwise be overlooked [65]. This approach is particularly valuable during problem formulation to ensure the algorithm addresses appropriate clinical needs.
Human-in-the-Loop Systems: Incorporating clinician oversight and intervention points within AI systems provides safeguards against biased recommendations [68]. This approach maintains human authority over final clinical decisions while leveraging AI efficiency.
Diverse Development Teams: Ensuring diversity in AI development teams across dimensions of race, gender, discipline, and geography helps identify potential biases early in the development process [63]. Homogeneous teams are more likely to overlook contextual factors affecting diverse patient populations.
Research Reagents and Tools for Bias Assessment
Implementing effective bias mitigation requires specialized tools and frameworks. The following table details essential resources for researchers evaluating algorithmic fairness in healthcare applications.
Table 3: Essential Research Tools for Algorithmic Bias Assessment
| Tool/Resource | Type | Primary Function | Application Context |
|---|---|---|---|
| ISO/IEC 19795-10:2024 [67] | International Standard | Quantifying biometric system performance variation across demographics | Regulatory validation of biometric technologies |
| NIST Face Recognition Vendor Test (FRVT) [66] | Benchmarking Framework | Independent evaluation of facial recognition accuracy and fairness | Pre-deployment algorithm validation |
| AI Fairness 360 (AIF360) | Open-source Toolkit | Comprehensive set of fairness metrics and mitigation algorithms | Algorithm development and testing |
| PROBAST [64] | Assessment Tool | Prediction model Risk Of Bias ASsessment Tool | Systematic evaluation of AI model bias |
| FIDO Alliance Certification [67] | Certification Program | Standardized testing for face verification performance and bias | Commercial product validation |
| Synthetic Data Generation [65] | Data Augmentation Technique | Creating representative data for underrepresented populations | Addressing data gaps for rare conditions |
Implementation Framework for Fairness by Design
Achieving algorithmic fairness requires systematic integration of mitigation strategies throughout the AI development lifecycle. The following workflow illustrates a comprehensive "Fairness by Design" approach that incorporates continuous bias assessment and mitigation.
Figure 2: Comprehensive "Fairness by Design" implementation workflow
Key Implementation Principles
Successful implementation of fairness strategies requires adherence to several core principles:
Transparency and Explainability: AI systems should provide insight into their functioning, the data used, and the assumptions made [65]. Explainable AI techniques enable clinicians and regulators to understand how decisions are generated and identify potential failure modes.
Continuous Monitoring and Evaluation: Bias mitigation should not be viewed as a one-time activity but as an ongoing process throughout the AI system lifecycle [64]. Continuous monitoring for performance degradation across demographic subgroups is essential, particularly as patient populations and clinical practices evolve.
Regulatory Compliance and Certification: Alignment with emerging regulatory frameworks ensures adherence to minimum standards for fairness and equity [67]. Independent certification programs provide validation of fairness claims and build trust among stakeholders [66].
Multidisciplinary Collaboration: Effective bias mitigation requires collaboration across computer science, clinical medicine, ethics, social science, and affected communities [65]. Such collaboration ensures AI systems remain contextually situated and address real clinical needs.
Mitigating algorithmic bias and ensuring fairness across diverse patient demographics represents both a moral imperative and a technical challenge in healthcare AI. The evidence indicates that biased algorithms can perpetuate and amplify existing health disparities, particularly affecting women, ethnic minorities, and socioeconomically disadvantaged groups [63]. However, comprehensive approaches that integrate technical mitigation strategies, robust validation protocols, and organizational frameworks show promise in addressing these challenges.
The regulatory landscape for biometric monitoring technologies is rapidly evolving, with increased emphasis on demonstrating fairness across demographic groups [67]. Independent benchmarking and certification programs provide standardized methodologies for evaluating algorithmic bias, while research institutions continue to develop more effective mitigation techniques [66] [68].
For researchers and drug development professionals, implementing the "Fairness by Design" approach throughout the AI development lifecycle is crucial for creating equitable healthcare technologies. This requires continuous attention to bias prevention, detection, and mitigation from problem formulation through deployment and monitoring. As the field advances, maintaining focus on both technical excellence and ethical responsibility will ensure that healthcare AI fulfills its potential to improve outcomes for all patient populations.
In the evolving landscape of data privacy, three technological paradigms have emerged as critical for protecting sensitive information: encryption, blockchain, and zero-trust architectures. For researchers, particularly those handling sensitive biometric and health data for drug development, understanding the capabilities, trade-offs, and appropriate applications of these technologies is essential for both security and regulatory compliance. This guide provides a comparative analysis to inform strategic decisions in safeguarding research data.
Encryption Technologies: The First Line of Defense
Encryption is the process of converting readable data (plaintext) into an unreadable format (ciphertext) using cryptographic algorithms, ensuring confidentiality, integrity, and authentication [69]. It serves as the foundational layer for most data security strategies.
Core Encryption Algorithms and Best Practices
Modern encryption is broadly categorized into symmetric and asymmetric cryptography, each with distinct strengths and applications suited to different research scenarios [70].
Table 1: Comparison of Core Encryption Algorithms
| Feature | AES-256 (Symmetric) | RSA-4096 (Asymmetric) | ECC-256 (Asymmetric) |
|---|---|---|---|
| Type | Symmetric | Asymmetric | Asymmetric |
| Best Use Cases | Bulk data encryption, file & database protection | Digital signatures, secure key exchange | Mobile/IoT devices, resource-constrained environments |
| Performance | Very Fast | Slow | Moderate |
| Key Size | 256 bits | 4096 bits | 256 bits |
| Quantum Resistance | Moderate (with larger keys) | Low | Low |
| Key Management | Complex (shared secret) | Simple (public/private pair) | Simple (public/private pair) |
For research data, the following best practices are recommended:
- Data at Rest: Utilize AES-256 for encrypting stored data, including full-disk encryption for devices and database encryption for sensitive research datasets [69] [70].
- Data in Transit: Implement TLS 1.3 for all network communications. A hybrid approach is typically used, leveraging asymmetric cryptography like RSA or ECC for the initial key exchange, then switching to fast symmetric encryption like AES for the session [70].
- Data in Use: For privacy-preserving data analysis, Homomorphic Encryption (HE) is an emerging technology that allows computations on encrypted data without decrypting it first. A 2025 performance comparison found that the CKKS scheme is generally faster for parallelizable operations, while TFHE excels at specific tasks like comparisons that require frequent "bootstrapping" (resetting the noise in the ciphertext) [71].
- Hardware vs. Software: Software encryption runs on the main CPU and can impact system performance, while hardware encryption uses a dedicated chip, offering better performance and greater isolation from malware [69]. For highly sensitive data, FIPS-certified hardware encryption with physical keys provides a high-security, air-gapped solution [69].
Blockchain Security: A Decentralized Paradigm
Blockchain provides a decentralized, tamper-resistant ledger for recording transactions and data. Its security is derived from a combination of cryptographic principles, consensus mechanisms, and distributed network architecture [72].
Cryptographic Backbone of Blockchain
The security of blockchain is not reliant on a single algorithm but on a layered cryptographic architecture [72]:
- Public Key Cryptography & Digital Signatures: Algorithms like ECDSA (used in Bitcoin and Ethereum) or EdDSA (gaining traction in networks like Solana) are used to generate key pairs. The private key signs transactions, and the public key allows the network to verify the sender's identity and the transaction's integrity, enabling trustless interactions [72].
- Cryptographic Hashing: Functions like SHA-256 (Bitcoin) and Keccak-256 (Ethereum) ensure data immutability. Each block contains the hash of the previous block, creating a cryptographic chain. Altering any data in a past block would change its hash and invalidate all subsequent blocks [72] [73].
- Zero-Knowledge Proofs (ZKPs): These are advanced cryptographic methods that allow one party to prove to another that a statement is true without revealing any information beyond the validity of the statement itself. They are increasingly used in blockchain for privacy-preserving transactions and scaling solutions [72].
Prevalent Security Vulnerabilities and Experimental Mitigations
Despite its robust design, blockchain faces significant security challenges that researchers must consider.
Table 2: Key Blockchain Vulnerabilities and Mitigation Protocols
| Vulnerability | Experimental / Mitigation Protocol | Supporting Data / Rationale |
|---|---|---|
| 51% Attacks | Monitor mining pools; shift to non-Proof-of-Work (PoW) consensus (e.g., Proof-of-Stake). | 51% attacks have led to an estimated $20 million in annual losses [73]. |
| Smart Contract Vulnerabilities | Implement rigorous testing with tools like Mythril/Oyente; conduct formal verification and regular audits. | Security audits can reduce breach risk by up to 50% by identifying logic errors and insecure access controls early [74]. |
| Insecure Private Key Management | Utilize hardware wallets, multi-signature schemes, and secure encryption for key storage. | High-profile breaches, like the $73M Bitfinex theft, have been attributed to stolen private keys [73]. |
| Insecure Oracles | Integrate decentralized oracle networks (e.g., Chainlink) for reliable external data. | Centralized oracles are a single point of failure and can feed tampered data to smart contracts [74]. |
Diagram: Blockchain Security Workflow and Threat Mitigation.
Zero-Trust Architecture: The "Never Trust, Always Verify" Model
Zero-Trust Architecture (ZTA) is a security framework that eliminates the concept of trust from the network perimeter. It operates on the principle of "never trust, always verify," requiring continuous validation of every user, device, and application attempting to access resources, regardless of their location [75] [76].
Core Components and Vendor Landscape
Implementing ZTA requires integrating several key technologies that work in concert to enforce strict, context-aware access policies.
Table 3: Core Components of a Zero-Trust Architecture
| Component | Function | Exemplary Solutions |
|---|---|---|
| Identity & Access Mgmt (IAM) | Manages digital identities and enforces role-based access control (RBAC). | Okta (Adaptive MFA, SSO) [76]. |
| Multi-Factor Authentication (MFA) | Requires multiple verification factors for access, adapting based on risk. | Okta, Duo [75] [76]. |
| Endpoint Security | Ensures only compliant, healthy devices can access resources. | SentinelOne (AI-driven EDR) [76]. |
| Microsegmentation | Divides the network into secure zones to limit lateral movement of threats. | Palo Alto Networks (Next-Gen Firewalls) [75] [76]. |
| Policy Engine & Enforcement | A centralized brain that makes real-time access decisions based on policy. | Zscaler (Cloud-native gateway) [76]. |
| Automation & Orchestration | Automates policy enforcement and incident response across the environment. | SentinelOne SOAR capabilities [76]. |
Diagram: Zero-Trust Architecture Access Logic.
Comparative Analysis and Research Implications
For research institutions validating biometric monitoring technologies, the choice of security framework depends on the specific data type, regulatory requirements, and use case.
Table 4: Technology Comparison for Research Security
| Aspect | Encryption | Blockchain | Zero-Trust Architecture |
|---|---|---|---|
| Primary Strength | Confidentiality of data at rest, in transit, and in use. | Integrity and non-repudiation of data records. | Context-aware access control and breach containment. |
| Data Integrity | Ensured via hashing within protocols. | Core inherent property via cryptographic chaining. | Not a primary feature; relies on other controls. |
| Decentralization | Not required. | Core inherent property. | Not required; can work with centralized policy. |
| Ideal Research Use Case | Protecting stored patient genomic data; secure analysis via HE. | Creating an immutable audit trail for clinical trial data. | Securing remote researcher access to cloud-based research platforms. |
| Regulatory Relevance | Directly addresses data protection mandates (e.g., GDPR, HIPAA). | Provides transparency and provenance for data handling. | Simplifies compliance auditing through granular access logging. |
The Scientist's Toolkit: Essential Research Reagents for Security
Table 5: Key "Research Reagent Solutions" in Data Security
| Item / Solution | Function / Explanation |
|---|---|
| Hardware Security Module (HSM) | A physical computing device that safeguards and manages digital keys, providing the root of trust for encryption. |
| Homomorphic Encryption (CKKS/TFHE) | A "reagent" for privacy-preserving computation, allowing analysis of encrypted data without exposing it. |
| Zero-Knowledge Proof (ZKP) | A cryptographic method to prove the validity of a statement without revealing the underlying data. |
| Decentralized Oracle Network | A critical "reagent" for blockchains, providing a trustless bridge between smart contracts and external data. |
| Formal Verification Tools | Mathematical methods and software to prove the correctness of security-critical code, such as smart contracts. |
| Microsegmentation Policy | The defined rule set that acts as a "reagent" to contain chemical reactions (cyber threats) within a network. |
Encryption, blockchain, and zero-trust architectures are not mutually exclusive but are complementary layers of a modern data security strategy. For the research community, particularly in regulated fields like drug development:
- Encryption remains the non-negotiable baseline for protecting data confidentiality.
- Blockchain offers a powerful tool for ensuring the integrity and provenance of research data, provided its vulnerabilities are actively managed.
- Zero-Trust Architecture is the essential framework for controlling access in a world of cloud computing and remote collaboration, directly supporting regulatory compliance through its granular logging and policy enforcement.
A defense-in-depth approach, leveraging the strengths of each paradigm, is most effective for securing sensitive biometric and research data against evolving threats.
For researchers and drug development professionals, the adoption of Biometric Monitoring Technologies (BioMeTs) in clinical trials presents a dual promise: the potential to capture rich, continuous physiological data in real-world settings, coupled with significant technical challenges that must be overcome for regulatory acceptance. The state of digitally measured biomarkers is highly reminiscent of the field of laboratory biomarkers two decades ago, lacking widely accepted performance characteristics and standardized validation frameworks [25]. The core technical hurdles—sensor accuracy, environmental variability, and system interoperability—represent critical validation points that must be addressed to establish biometric data as reliable evidence in therapeutic development.
The concept of "fit-for-purpose" validation, borrowed from the established principles of laboratory biomarker development, is paramount [25]. This approach dictates that the stringency of performance verification must be tailored to the specific context of use, whether for pharmacodynamic monitoring, proof of mechanism, or as a surrogate endpoint. This article provides a comparative analysis of current technologies and methodologies, structured to equip researchers with the experimental data and protocols necessary to navigate the complex validation pathway for BioMeTs.
Sensor Accuracy: Establishing Performance Baselines
Sensor accuracy is the foundational challenge, as data quality dictates its ultimate utility in research and regulatory decision-making. Accuracy is not a single metric but a composite of several performance characteristics that must be evaluated against a reference standard.
Comparative Performance of Biometric Modalities
The table below summarizes the documented accuracy of various biometric sensors as reported in technological studies and comparative analyses, providing a benchmark for researchers.
Table 1: Documented Accuracy of Select Biometric Sensors in Health Monitoring
| Biometric Modality | Example Device/Technology | Reported Accuracy | Context of Measurement | Reference Standard |
|---|---|---|---|---|
| Photoplethysmography (PPG) Heart Rate | Apple Watch Series 6 | 95% accuracy | General monitoring vs. clinical ECG | Clinical ECG [77] |
| Photoplethysmography (PPG) Heart Rate | Generic Fitness Trackers | As low as 75% accuracy | During vigorous exercise | Clinical ECG [77] |
| Atrial Fibrillation Detection | Apple Watch Series 7 | >98% accuracy | Opportunistic screening | Clinical diagnosis [77] |
| Continuous Glucose Monitoring | Dexcom G6 | MARD*: 9% | Continuous interstitial monitoring | Laboratory blood glucose [77] |
| Continuous Glucose Monitoring | FreeStyle Libre | MARD*: 9.4% | Continuous interstitial monitoring | Laboratory blood glucose [77] |
| Electrodermal Activity (EDA) | Research-grade wristbands | Variable | Controlled lab stimuli | Laboratory-grade EDA system [78] |
MARD: Mean Absolute Relative Difference, a standard metric for CGM accuracy; lower values are better.
Experimental Protocols for Validating Sensor Accuracy
To generate data comparable to the studies above, researchers must implement rigorous experimental protocols. The following methodology outlines a core approach for establishing the analytical validity of a BioMeT.
Protocol 1: Bench Validation and Human Subjects Testing
This fit-for-purpose protocol combines controlled bench testing with human subjects experimentation to characterize a sensor's basic performance [25].
- Objective: To establish the accuracy, precision, and linearity of a biometric sensor against a certified reference standard.
- Materials:
- The BioMeT device under test (DUT)
- A certified reference device or simulator (e.g., ECG simulator, blood gas analyzer, motion platform)
- Controlled environmental chamber (for temperature/humidity control)
- Data acquisition and statistical analysis software (e.g., Python, R, MATLAB)
- Procedure:
- Bench Testing: Place the DUT in a controlled environment. Use a reference simulator to generate signals of known amplitudes and frequencies. Systematically vary parameters (e.g., heart rate from 40-180 bpm, motion artifact) while recording the DUT's output.
- Human Subjects Testing: Recruit a cohort of participants representative of the intended use population. Simultaneously deploy the DUT and the reference device on each participant during a protocol that includes resting states, controlled exercise (e.g., treadmill), and recovery periods.
- Data Analysis: Perform a Bland-Altman analysis to assess the limits of agreement between the DUT and the reference standard. Calculate correlation coefficients, sensitivity, specificity, and root mean square error (RMSE) where appropriate.
Figure 1: Experimental workflow for core sensor validation, covering bench and human testing.
Environmental Variability: From Laboratory to Real World
A sensor that performs well in a controlled lab often fails in the face of real-world environmental and physiological noise. A validation framework must therefore account for these confounding factors.
Impact of Environmental Factors on Data Quality
Environmental variability introduces noise and artifact that can severely degrade signal quality. The primary sources of variability include:
- Motion Artifact: The most significant challenge for wearable sensors. Sudden movements can generate signals orders of magnitude larger than the physiological signal of interest (e.g., PPG) [77].
- Ambient Conditions: Variations in skin temperature, ambient light (for optical sensors), and humidity (affecting skin-electrode contact for biopotential sensors) can alter signal baseline and amplitude [77] [79].
- User Factors: Skin tone, body hair, tattoo density, and subcutaneous fat can affect the penetration and reflection of light in optical sensors like PPG, leading to performance disparities across populations [25].
Protocol for Assessing Environmental Robustness
A key step in validation is to stress-test the device under realistic and challenging conditions.
Protocol 2: Environmental and Stressor Testing
- Objective: To quantify the impact of specific environmental and physiological stressors on the accuracy and reliability of the biometric sensor.
- Materials:
- DUT and reference device.
- Environmental chamber (for temperature/humidity).
- Treadmill or stationary bike (for motion and exertion).
- Light source (for testing optical sensors).
- Procedure:
- Stressor Definition: Identify the primary potential stressors relevant to the context of use (e.g., motion for a Parkinson's study, temperature for a thermoregulation study).
- Controlled Introduction: For each stressor, design a protocol that gradually increases its intensity while collecting data from both the DUT and the reference.
- Motion: Periods of rest, walking, running, and simulated activities of daily living.
- Temperature: Measure performance in a controlled chamber across a range of temperatures (e.g., 15°C to 35°C).
- Ambient Light: Expose optical sensors to different lighting conditions (darkroom, fluorescent, direct sunlight).
- Artifact Quantification: Calculate the signal-to-noise ratio (SNR) and the rate of data loss or invalidation for each stressor level. Compare the DUT's performance degradation to that of the reference standard.
Interoperability: The Keystone for Scalable Research
Interoperability—the ability of different systems and organizations to work together seamlessly—is perhaps the most systemic hurdle. Without it, data remains siloed, and multi-site trials become prohibitively complex.
The Interoperability Landscape and Challenges
The search for interoperability is a common theme across domains, from public safety to digital identity.
- In Public Safety: Agencies report frustration with search times, data limitations, and access gaps when relying on state-run biometric systems. The strong desire is for the ability to query local databases before escalating to state-level searches, a hybrid approach to interoperability [80].
- In Digital Identity: Governments are pushing for interoperable digital identity wallets, such as the EU Digital Identity (EUDI) Wallet, guided by the eIDAS 2.0 regulation to create a standardized framework for cross-border use [81]. Success depends on overcoming differing standards across jurisdictions and integrating with legacy systems.
- In Clinical Research: A lack of common data standards and system interoperability leads to "pilotitis"—a high number of small-scale, inconclusive feasibility studies that fail to scale [25]. The problem is exacerbated by the involvement of multiple stakeholders: device engineers, software developers, data scientists, regulators, and clinicians.
Table 2: Interoperability Standards and Frameworks Across Domains
| Domain | Standard / Framework | Governance | Primary Purpose | Status / Timeline |
|---|---|---|---|---|
| Digital Identity | EUDI Wallet | European Union | Cross-border identity verification and data sharing | Deployment to citizens by end of 2026 [81] |
| Digital Identity | ISO 18013-5 / mDL | International Organization for Standardization (ISO) | Digital representation of physical driver's licenses | Gaining traction (e.g., TSA acceptance) [81] |
| Government Biometrics | IDENT Exchange Messages (IXM) | DHS Office of Biometric Identity Management (OBIM) | Sharing biometric data between government agencies | Operational [52] |
| Government Biometrics | Electronic Biometric Transmission Spec (EBTS) | FBI | Exchange of biometric and criminal history data | Operational [52] |
Protocol for Assessing System Interoperability
For a research team selecting a BioMeT, a key consideration is its ability to integrate with existing data platforms and share data in a standardized format.
Protocol 3: Functional Interoperability Testing
- Objective: To evaluate the ability of a BioMeT system to exchange data with a clinical trial data platform and ensure the data is interpretable and usable.
- Materials:
- The BioMeT system, including sensor, companion app, and cloud API.
- A target clinical data platform (e.g., REDCap, Medidata Rave).
- Documentation for all data formats and communication protocols.
- Procedure:
- Interface Analysis: Identify the available data export and integration interfaces (e.g., CSV export, RESTful API, FHIR integration).
- Data Mapping: Attempt to map the raw and processed data outputs from the BioMeT to the data model of the clinical platform. Pay special attention to timestamps, units, and participant identifiers.
- End-to-End Testing: Execute a full data flow from data collection on the sensor, through transmission to the cloud, to ingestion and display in the clinical platform. Verify data fidelity and completeness at each step.
- Performance Metrics: Measure the latency of data transfer and the percentage of data points successfully ingested without manual intervention.
Figure 2: Interoperability depends on multiple subsystems connecting via standardized protocols.
The Scientist's Toolkit: Essential Research Reagents and Materials
Navigating the technical hurdles of BioMeTs requires a specific set of tools and reagents for experimental validation. The following table details key items for a research team's toolkit.
Table 3: Essential Research Reagents and Solutions for BioMeT Validation
| Tool / Reagent | Function in Validation | Example Use-Case |
|---|---|---|
| Signal Simulator | Generates precise, known physiological signals (e.g., ECG, PPG waveforms) to test sensor accuracy in isolation from biological variability. | Bench-testing the heart rate accuracy of a new smartwatch against a calibrated PPG waveform. |
| Controlled Environmental Chamber | Manipulates and controls ambient temperature and humidity to test sensor robustness and performance under various environmental conditions. | Determining the operating limits of a skin temperature sensor for a study involving participants in different climates. |
| Reference Grade Biometric Device | Provides a "gold standard" measurement against which the commercial or research BioMeT is validated. | Using a clinical-grade Holter monitor to validate a patch-based ECG sensor for arrhythmia detection. |
| Motion Platform | Introduces standardized, repeatable motion profiles to quantitatively assess a sensor's susceptibility to motion artifacts. | Characterizing the motion artifact in a wearable accelerometer during simulated walking or running. |
| Data Analysis Software (e.g., Python/R with specialized libraries) | Processes raw sensor data, extracts features, performs statistical analysis (e.g., Bland-Altman), and visualizes results for validation reporting. | Calculating the mean absolute relative difference (MARD) for a continuous glucose monitor versus venous blood measurements. |
| iMotions Biometric Software | Integrates data streams from multiple biometric sensors (EEG, eye-tracking, EDA) for synchronized data collection and analysis, particularly in human factors testing. | Studying the cognitive load and usability of a new BioMeT's user interface during a model comprehension task [78] [79]. |
Overcoming the technical hurdles of sensor accuracy, environmental variability, and interoperability is not merely an engineering challenge but a fundamental prerequisite for the valid use of BioMeTs in clinical research and drug development. The comparative data and experimental protocols outlined here provide a foundational framework for researchers to rigorously evaluate these technologies. By adopting a fit-for-purpose validation mindset, leveraging appropriate reference standards, and demanding greater interoperability through standards, the research community can build the evidentiary basis needed for regulators to accept digitally measured biomarkers. This, in turn, will accelerate the adoption of these powerful tools, enabling more sensitive, efficient, and patient-centric clinical trials.
For researchers and drug development professionals, the use of Biometric Monitoring Technologies (BioMeTs) presents a dual challenge: validating technological reliability while simultaneously navigating a complex web of corporate criminal liability and international data regulations. The recent introduction of strict liability offenses, such as the UK's "failure to prevent fraud" under the Economic Crime and Corporate Transparency Act 2023 (ECCTA), creates significant new compliance obligations for organizations, including those in the research sector [82]. Simultaneously, the collection and processing of biometric data for research must adhere to evolving frameworks like the EU's GDPR, which classifies biometric data as a "special category" requiring strict protections [83].
This guide examines these converging regulatory demands, providing a structured comparison of compliance frameworks and detailed experimental protocols for validating BioMeTs within this stringent legal environment. The goal is to equip scientific teams with the strategies needed to ensure that their research tools are not only scientifically fit-for-purpose but also legally defensible.
Comparative Analysis of Regulatory Frameworks
"Failure to Prevent" Offenses and Corporate Liability
The UK's "failure to prevent fraud" offense, effective from 1 September 2025, represents a significant shift in corporate criminal liability. It imposes strict liability on large organizations (meeting two of: >250 employees, >£36 million turnover, or >£18 million in assets) for fraud committed by an "associate" (employees, agents, subsidiaries, or anyone performing services on the organization's behalf) intended to benefit the organization [82]. The only defense is demonstrating that "reasonable procedures" were in place to prevent the fraud [82] [84]. The table below compares key "failure to prevent" offenses.
Table 1: Comparison of International "Failure to Prevent" Offenses
| Feature | UK Failure to Prevent Fraud (ECCTA) | UK Failure to Prevent Bribery (Bribery Act 2010) | UK Failure to Prevent Tax Evasion (Criminal Finances Act 2017) |
|---|---|---|---|
| Scope of Offense | Failure to prevent specified fraud offenses (e.g., false accounting, false representation) [82] | Failure to prevent bribery [84] | Failure to prevent facilitation of tax evasion [82] |
| Applicability | "Large organisations" as defined by size thresholds [82] | All commercial organizations [84] | All corporations and partnerships [82] |
| Defense | "Reasonable procedures" to prevent fraud [82] | "Adequate procedures" to prevent bribery [84] | "Reasonable prevention procedures" [82] |
| Key Principles for Procedures | 1. Top-level commitment2. Risk assessment3. Proportionate procedures4. Due diligence5. Communication/Training6. Monitoring & Review [84] | Similar six principles, but with "Proportionate procedures" historically listed first [84] | Based on six guiding principles [82] |
International Biometric Data Regulations
Biometric data collected via BioMeTs is subject to a fragmented global regulatory landscape. Researchers operating internationally must design protocols that satisfy multiple, sometimes conflicting, legal requirements. The following table provides a high-level comparison of these frameworks.
Table 2: Comparison of International Biometric Data Regulations
| Regulation/Region | Classification of Biometric Data | Key Requirements | Implications for BioMeT Research |
|---|---|---|---|
| EU (GDPR) | "Special category" data [83] | Requires explicit consent; strict rules on storage and processing; transparency [83] | Protocols must embed privacy by design, obtain explicit consent for specific research uses, and ensure robust data encryption. |
| United States | Varies by state; often under general privacy laws [83] | Sector-specific rules (e.g., GLBA for finance); state laws like Illinois BIPA mandate consent and protection [85] [83] | Researchers must comply with the strictest applicable state law, even for national studies, particularly regarding consent and data retention. |
| Asia-Pacific (e.g., India) | Evolving regulations with increasing protection [83] | India's Aadhaar system enables biometric KYC; Supreme Court has mandated privacy protections [85] [83] | Research using digital onboarding or identity verification must integrate with national systems while adhering to judicial privacy mandates. |
Experimental Validation for Regulatory Compliance
Protocol for Validating BioMeT Analytical Performance
To meet the "reasonable procedures" defense and data protection requirements, the validation of BioMeTs must be rigorous and documented. The following protocol aligns with the FDA's "fit-for-purpose" and evidentiary framework for biomarker qualification [25].
Objective: To establish the analytical validity of a BioMeT for a specific Context of Use (COU) in a clinical trial, ensuring reliability and generating evidence for regulatory and compliance audits.
Workflow Overview: The following diagram illustrates the key stages of this validation protocol.
Methodology:
- Define Context of Use (COU): Precisely specify the physiological or behavioral biomarker (e.g., resting heart rate, step count, sleep duration), the target population, and the intended clinical trial application [25].
- Bench Validation: Assess the sensor's performance in a controlled lab environment. This includes testing accuracy, precision, and stability against a calibrated reference standard across environmental conditions (e.g., temperature, humidity) [25].
- Analytical Validation: Establish performance characteristics in the intended human subject population.
- Metrics: Calculate accuracy (vs. a gold-standard), precision (repeatability and reproducibility), sensitivity, and specificity [25].
- Human Factors Testing: Evaluate the device's usability across the target population, including participants with varying levels of technological literacy, to ensure reliable data collection [25].
- Clinical Validation: Investigate the association between the digitally measured biomarker and a clinical outcome of interest. This is separate from analytical validation and is specific to the research hypothesis [25].
- Documentation and Audit Trail: Meticulously document all procedures, raw data, processing algorithms, and results. This is critical for both regulatory submission and demonstrating "reasonable procedures" under compliance laws [82] [25].
Protocol for a Fraud Risk Assessment
A documented, dynamic risk assessment is a cornerstone of the "reasonable procedures" defense for "failure to prevent" offenses [84]. This protocol outlines a systematic approach to fraud risk assessment.
Objective: To proactively identify, evaluate, and mitigate the risk of fraud being committed by an "associate" within or on behalf of the organization.
Workflow Overview: The risk assessment is a continuous cycle, as shown below.
Methodology:
- Scoping: Define the assessment's boundaries, covering all relevant business units, geographies, and third-party relationships (e.g., CROs, data processors) [84].
- Risk Identification: Identify potential fraud risks by considering the "fraud triangle":
- Opportunity: Weaknesses in internal controls (e.g., inadequate segregation of duties in data handling, lack of algorithm audit trails).
- Motivation: Pressures such as aggressive research targets or publication deadlines.
- Rationalization: Cultural attitudes that might justify misconduct [84].
- Risk Analysis: Evaluate identified risks based on their likelihood and potential impact (financial, reputational, legal). Classify risks (e.g., High, Medium, Low) to prioritize resources [84].
- Risk Mitigation: Develop and implement proportionate, risk-based controls. This could include enhancing data integrity protocols, implementing robust whistleblowing channels, and providing targeted training on fraud prevention [82] [84].
- Monitoring and Review: Establish a schedule for periodic reassessment of risks. The risk assessment must be a "dynamic" document, updated in response to internal changes (e.g., new projects) or external events [84].
Table 3: Research Reagent Solutions for Compliance and Validation
| Tool / Solution | Function / Description | Relevance to Compliance & Validation |
|---|---|---|
| ISO/IEC Biometric Standards | A suite of 143 published standards (as of Jan 2025) covering vocabulary, data formats, and performance testing [83]. | Provides an international framework for ensuring consistent, reliable, and comparable implementation of BioMeTs, supporting analytical validation. |
| Multimodal Biometric Systems | Systems that combine two or more biometric traits (e.g., face and voice) to enhance accuracy and security [83]. | Reduces the risk of fraud (e.g., impersonation) in patient identity verification, supporting "failure to prevent" compliance. |
| Behavioral Biometrics | Analyzes unique behavioral patterns (typing rhythm, mouse movements) for continuous, non-intrusive authentication [85] [83]. | Provides a layer of security for research data systems, protecting against unauthorized access and data manipulation. |
| Third-Party Risk Management Tools | Technology solutions used to conduct due diligence on partners, agents, and suppliers [84]. | Directly supports the "due diligence" principle of "failure to prevent" offenses by assessing the fraud risk posed by third parties like CROs. |
| Robust Whistleblowing Framework | A confidential and accessible mechanism for employees and third parties to report concerns without fear of retaliation [82] [84]. | A critical detection tool, explicitly highlighted in guidance, that helps uncover potential fraud and demonstrates a commitment to an open culture. |
In the evolving landscape of biometric research, scientific rigor and regulatory compliance are inseparable. A proactive, integrated strategy—combining robust, "fit-for-purpose" BioMeT validation with a comprehensive corporate compliance program based on risk assessment, top-level commitment, and continuous monitoring—is no longer optional. It is a fundamental requirement for mitigating legal risk and ensuring the integrity of research outcomes. By adopting the structured comparisons and detailed protocols outlined in this guide, researchers and drug development professionals can confidently navigate the dual challenges of technological validation and legal scrutiny.
This guide provides an objective comparison of advanced biometric systems, analyzing their performance, costs, and benefits within a framework of regulatory validation. For researchers and drug development professionals, biometric technologies offer transformative potential for patient identification, clinical trial security, and data integrity. The analysis reveals that while initial implementation costs remain substantial, the long-term economic benefits and security enhancements present a compelling value proposition when proper management strategies are employed. Current market data indicates the global biometric technology market is projected to grow from USD 61.7 billion in 2025 to USD 363.2 billion by 2034, reflecting a compound annual growth rate (CAGR) of 21.8% [86]. This growth is fueled by increasing security demands across healthcare, finance, and government sectors, though it is tempered by significant privacy concerns and technical implementation challenges that require careful navigation.
Market Performance and Cost Analysis
The biometric technology landscape demonstrates robust growth with varying projections across research firms, though all indicate significant expansion. The table below summarizes key market metrics and cost components essential for strategic planning.
Table 1: Biometric Technology Market Size and Growth Projections
| Metric | 2025 Base Value | 2034/2035 Projection | CAGR | Source |
|---|---|---|---|---|
| Global Market Size | USD 61.7 billion [86] | USD 363.2 billion (2034) [86] | 21.8% [86] | Dimension Market Research |
| Alternate Market Size | USD 59.65 billion [87] | USD 322.94 billion (2035) [87] | 18.4% [87] | Research Nester |
Table 2: Cost-Benefit Analysis of Biometric System Components
| System Component | Cost/Risk Factors | Benefit/ROI Factors | Quantitative Data |
|---|---|---|---|
| Hardware | High initial investment for sensors, scanners, and cameras [87]. | Reduced long-term operational costs; enables secure access control [87]. | Hardware segment expected to hold 45.2% market share [87]. |
| Software & AI | Development and licensing costs; ongoing updates for spoof detection [87]. | Improved accuracy and efficiency; adaptive learning reduces false rates [88]. | AI-driven models achieve under 120ms processing speeds and 99.5% accuracy in controlled settings [37]. |
| Implementation & Maintenance | High setup and maintenance costs challenge SMEs [86] [87]. | Streamlined operations and reduced fraud offset costs over time [86]. | Benefit-cost ratio of Uganda's National ID system was 1.35 [89]. |
| Regulatory Compliance | Costs of adhering to GDPR, BIPA, and other privacy laws [37] [90]. | Avoidance of legal penalties; enhanced consumer trust [37]. | Illinois BIPA generated settlements exceeding $50 million [37]. |
| Data Security | High-cost encryption and protection against breaches required [86]. | Prevention of costly fraud and identity theft [86]. | 81% of consumers view biometrics as more secure than traditional methods [86]. |
Experimental Protocols and Performance Validation
Validating biometric system performance requires rigorous testing under controlled and real-world conditions. The following established protocols provide frameworks for objective comparison and regulatory submission.
Protocol for Accuracy and Demographic Bias Testing
Objective: To measure baseline authentication accuracy and identify performance disparities across demographic groups.
Methodology:
- Dataset Curation: Recruit a diverse participant pool stratified by gender, skin tone, and age. Major studies have revealed that many training datasets are over 77% male and 83% white, which must be corrected for valid results [37].
- Controlled Environment Testing: Conduct initial tests in lab conditions with standardized lighting, camera positioning, and background.
- Variable Introduction: Systematically introduce real-world variables including poor lighting, facial obstructions (masks, glasses), and different angles.
- Performance Metrics: Calculate False Acceptance Rate (FAR), False Rejection Rate (FRR), and overall accuracy for each demographic subgroup.
Supporting Data: Research has documented significant accuracy disparities, with error rates of 0.8% for light-skinned men compared to over 34% for dark-skinned women in some systems [37]. This protocol directly addresses regulatory concerns about algorithmic bias and fairness.
Protocol for Liveness Detection and Spoofing Resistance
Objective: To evaluate a system's resilience against presentation attacks using photos, videos, masks, or synthetic media (deepfakes).
Methodology:
- Spoof Artefact Creation: Develop a comprehensive set of attack vectors including high-resolution photos, screen replay videos, 3D masks, and AI-generated deepfakes.
- Staged Attack Simulation: Execute a predetermined number of spoofing attempts against the biometric system.
- Liveness Detection Calibration: Activate liveness detection technologies, such as MagnifEye, which can perform multimodal liveness detection within seconds without compromising user experience [87].
- Success Rate Calculation: Measure the system's ability to correctly identify and reject spoofing attempts while maintaining a low false rejection rate for legitimate users.
Supporting Data: The deepfake threat is increasingly sophisticated, with only 0.1% of people able to correctly identify all AI-generated content [91]. This protocol is critical for regulatory validation of system security in high-stakes applications like clinical data protection.
Cost-Benefit Validation Framework for Large-Scale Deployment
Objective: To quantitatively assess the economic viability of biometric system investments, particularly for institutional deployments.
Methodology:
- Cost Aggregation: Document all capital expenditures (hardware, software) and operational expenditures (maintenance, training, updates).
- Benefit Quantification: Measure specific benefits including fraud reduction, efficiency gains (faster authentication), and improved regulatory compliance.
- Stakeholder Analysis: Conduct surveys and interviews to assess user experience, adoption rates, and perceived value across different user groups.
- Ratio Calculation: Compute a benefit-cost ratio (BCR) to determine overall economic value.
Supporting Data: A nationwide study of Uganda's national digital ID system demonstrated a BCR of 1.35, with significant benefits in financial inclusion and access to government services, though the lowest socioeconomic quintile felt the least benefit [89]. This highlights the importance of inclusive design in regulatory frameworks.
The Researcher's Toolkit: Biometric Technology Framework
This section outlines the essential components and considerations for implementing biometric systems in research and regulatory environments.
Table 3: Research Reagent Solutions for Biometric System Implementation
| Component | Function | Research Application |
|---|---|---|
| Liveness Detection (e.g., MagnifEye) | Determines if the source is a live person versus a spoof artifact [87]. | Critical for ensuring the integrity of patient identity in clinical trials and remote monitoring. |
| Multimodal Biometric Systems | Combines multiple biometric factors (e.g., face + voice) for layered authentication [37] [92]. | Enhances security for sensitive research data; provides fallback options to reduce user friction. |
| Behavioral Biometrics | Analyzes unique patterns in keystrokes, mouse movements, and gait [92]. | Enables continuous, passive authentication without interrupting research activities. |
| Quantum-Resistant Encryption | Protects stored biometric templates from future decryption by quantum computers [93]. | Future-proofs sensitive, long-term research databases containing participant biometric data. |
| Blockchain-Based Storage | Provides decentralized, tamper-evident ledgers for biometric data audit trails [88]. | Creates immutable logs of data access and usage, which is vital for regulatory compliance. |
Strategic Implementation Workflow
The following diagram maps the logical workflow for validating, implementing, and managing a biometric system within a regulated research environment. This process emphasizes balancing technological capabilities with ethical and regulatory requirements.
The cost-benefit analysis of advanced biometric systems reveals a complex landscape where significant investments are required but can yield substantial returns in security, efficiency, and regulatory compliance. For the research and scientific community, these technologies offer powerful tools for safeguarding intellectual property, ensuring data integrity, and verifying participant identity in clinical trials.
Future developments in quantum-resistant encryption [93], AI-powered liveness detection [88], and behavioral biometrics [92] will continue to enhance the value proposition. However, successful implementation depends on a balanced approach that prioritizes not only technological performance and cost management but also rigorous attention to ethical guidelines, privacy protections, and regulatory compliance. As the World Economic Forum's GRIP initiative emphasizes, the goal is a transition towards regulatory systems that are "iterative, responsive and co-created with a range of stakeholders" [90], ensuring that innovation proceeds responsibly and with public trust.
Benchmarking Performance and Comparative Analysis of BioMeTs
This guide provides an objective comparison of the performance of three primary biometric technologies—fingerprint, facial, and iris recognition—framed within the context of validating regulatory frameworks for biometric monitoring technologies.
Comparative Performance KPIs for Biometric Modalities
The following table summarizes the core performance indicators for the three dominant biometric modalities, based on current industry data and testing benchmarks. [94] [95] [96]
Table 1: Key Performance Indicators (KPIs) for Major Biometric Modalities
| Biometric Modality | Accuracy (False Rejection Rate - FRR) | False Acceptance Rate (FAR) | Throughput Speed (Users/Minute) | Unit Cost (USD) |
|---|---|---|---|---|
| Fingerprint Recognition | 1-2% [94] | Not specified in results | 30-60 [94] | $50 - $200 [94] |
| Facial Recognition | <1% (FRR for top algorithms) [95] | <0.1% (FAR for top algorithms) [95] | 20-40 [94] | $200 - $600 [94] |
| Iris Recognition | <0.5% [94] | Extremely low (e.g., 1 in 1.5M) [96] | 15-30 [94] | $400 - $1,200 [94] |
Experimental Protocols for KPI Validation
Validating the KPIs in Table 1 requires rigorous, standardized testing methodologies. The protocols below are essential for generating comparable and reliable data for regulatory assessment.
Protocol for FAR and FRR Calculation in Verification Mode
This protocol tests a system's ability to confirm a user's claimed identity (1:1 matching). [97]
- Objective: To measure the False Acceptance Rate (FAR) and False Rejection Rate (FRR) of a biometric verification system across a range of decision thresholds.
- Core Workflow:
- Template Creation: For each user in the test database, create a reference template from a single biometric sample (e.g., one fingerprint image).
- Genuine Comparisons: Compare each user's remaining samples against their own template to generate a set of genuine scores.
- Impostor Comparisons: Compare each user's samples against the templates of all other users to generate a set of impostor scores.
- Threshold Application: Select a decision threshold. Scores above this threshold are considered a "match."
- KPI Calculation:
- Output: A Receiver Operating Characteristic (ROC) curve that plots FRR against FAR for all possible thresholds, allowing stakeholders to select a threshold based on their security vs. convenience requirements.
The following diagram illustrates the logical workflow and decision points for this testing protocol.
Protocol for NIST FRVT-Compliant Performance Benchmarking
The U.S. National Institute of Standards and Technology (NIST) Face Recognition Vendor Test (FRVT) provides a global, independent benchmark for evaluating biometric algorithms. [95]
- Objective: To assess the accuracy, speed, and bias of facial recognition algorithms under standardized, large-scale conditions.
- Core Workflow:
- Algorithm Submission: Vendors submit their software development kits (SDKs) to NIST for evaluation on secure government systems.
- Large-Scale Dataset Testing: NIST runs the algorithms against massive, diverse datasets containing millions of facial images. These datasets vary in:
- Metric Calculation: NIST calculates a comprehensive set of performance metrics, including:
- False Match Rate (FMR): Analogous to FAR.
- False Non-Match Rate (FNMR): Analogous to FRR.
- Throughput: Processing speed (e.g., transactions per second).
- Bias and Robustness Analysis: Performance is disaggregated across different demographic groups to identify and quantify algorithmic bias, a critical factor for regulatory validation. [37]
- Output: Publicly available reports and leaderboards that provide a transparent, objective comparison of algorithm performance, which regulators can use to define minimum performance standards. [95]
The diagram below maps the staged process of this independent benchmarking.
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key hardware and software components required for establishing a rigorous biometric testing framework.
Table 2: Essential Materials for Biometric Performance Validation
| Item | Function / Relevance |
|---|---|
| NIST FRVT Reports [95] | Provides independent, benchmarked performance data (accuracy, speed, bias) for facial recognition algorithms, serving as a gold-standard reference for regulators. |
| Iris Recognition SDK (e.g., from Iris ID, Idemia) [98] [96] | Enables integration of high-accuracy iris recognition for testing. Includes feature extraction and matching algorithms crucial for generating iris codes and calculating KPIs. |
| Multi-Modal Biometric Sensors [38] | Hardware (fingerprint scanners, NIR iris cameras, facial recognition cameras) for capturing biometric samples under different environmental conditions for robustness testing. |
| Presentation Attack Detection (PAD) [99] [38] | Software modules that use AI to analyze subtle cues (micro-expressions, texture) to distinguish live subjects from spoofs (e.g., photos, masks), critical for security validation. |
| Biometric Data Encryption Tools [94] | Software and protocols (e.g., AES-256) to secure biometric templates in transit and at rest, addressing privacy and data security requirements during testing and deployment. |
Biometric systems have become foundational to identity verification in our increasingly digital and security-conscious world. These systems, which authenticate individuals based on unique physiological or behavioral characteristics, generally fall into two architectural categories: unimodal (relying on a single biometric trait) and multimodal (combining two or more traits). For researchers, scientists, and drug development professionals engaged in validating regulatory frameworks for biometric monitoring technologies, understanding the technical and performance distinctions between these approaches is critical. This guide provides an objective, data-driven comparison to inform both research directions and regulatory policies, assessing both systems against the metrics of accuracy, security, and applicability to real-world scenarios.
Fundamental Characteristics and Theoretical Foundations
The core distinction between unimodal and multimodal systems lies in their fundamental design and the underlying principle of information fusion. A unimodal system relies on a single biometric identifier, whereas a multimodal system integrates evidence from multiple sources to form a more robust decision [100].
Unimodal Biometric Systems
Unimodal systems authenticate identity based on one physiological or behavioral characteristic. Common physiological modalities include fingerprints, facial recognition, iris patterns, and vein structures, while behavioral modalities encompass voice, gait, and typing rhythm [100]. The selection of a specific modality for an application is typically evaluated against seven criteria: Universality, Uniqueness, Permanence, Measurability, Performance, Acceptability, and Circumvention (resistance to spoofing) [100]. In practice, no single modality scores perfectly across all seven criteria, which represents a fundamental limitation of the unimodal approach.
Multimodal Biometric Systems
Multimodal systems overcome unimodal limitations by combining two or more biometric traits. The system's architecture involves four key modules: Sensor Modules, Feature Extraction Modules, a Matching Module, and a Decision-Making Module [100]. The fusion of information, which is the cornerstone of its enhanced performance, can occur at different levels of processing [100] [101]:
- Sensor Level Fusion: Raw data from different sensors are combined.
- Feature Level Fusion: Feature vectors extracted from each modality are merged into a composite vector.
- Matching Score Level Fusion: Matching scores from individual modalities are combined.
- Decision Level Fusion: Final decisions (accept/reject) from separate modalities are consolidated.
Table 1: Core Conceptual Differences Between Unimodal and Multimodal Systems
| Feature | Unimodal Systems | Multimodal Systems |
|---|---|---|
| Core Principle | Relies on a single biometric trait for authentication | Fuses two or more biometric traits for authentication |
| Information Processing | Single processing channel | Multiple, potentially parallel, processing channels |
| Primary Goal | Simplicity and cost-effectiveness | Enhanced accuracy, security, and reliability |
| Ideal Use Case | Low-risk, controlled environments | High-security, large-scale, or variable conditions |
Figure 1: Architectural comparison of Unimodal (single-channel) and Multimodal (multi-channel with fusion) biometric systems.
Performance and Accuracy: A Quantitative Comparison
Empirical data consistently demonstrates that multimodal systems achieve superior accuracy by mitigating the specific failure modes of unimodal systems. Unimodal systems are susceptible to high False Non-Match Rates (FNMR), where legitimate users are incorrectly rejected, and False Match Rates (FMR), where impostors are incorrectly accepted [100]. These errors often stem from noisy sensor data, non-universal biometric traits, or changing environmental conditions.
Experimental Data from Recent Studies
Recent peer-reviewed studies provide quantitative evidence of the performance gains from multimodal fusion.
A 2025 study published in Applied Sciences developed a deep learning-based system fusing fingerprint (FP) and finger vein (FV) modalities. The researchers evaluated three fusion strategies on the NUPT-FPV dataset (33,600 images from 140 subjects) and reported the following results [101]:
Table 2: Performance Comparison of Fusion Strategies in a Fingerprint & Finger Vein System
| Fusion Strategy | Reported Accuracy | Equal Error Rate (EER) |
|---|---|---|
| Feature-Level Fusion | 99.72% | 0.0025 |
| Score-Level Fusion | 99.75% | 0.0021 |
| Hybrid Fusion (Feature + Score) | 99.79% | 0.0018 |
Another 2025 study in Pattern Recognition Letters proposed a novel system using a smartphone camera to capture both Photoplethysmography (PPG) signals and fingerprint images simultaneously. This approach, which requires no specialized hardware, demonstrated high robustness across different testing scenarios [44]:
Table 3: Performance of a Smartphone-Based Multimodal (PPG + Fingerprint) System
| Authentication Scenario | Reported Accuracy | Equal Error Rate (EER) |
|---|---|---|
| Single-Session Data | 100% | 0.1% |
| Dual-Session Data | 94.3% | 6.9% |
The performance advantage of multimodal systems is further cemented by their drastic reduction in operational failure rates. By providing multiple pathways for authentication, these systems can almost eliminate Failure-to-Acquire (FTA) and Failure-to-Enroll (FTE) rates, ensuring broader accessibility and reliability in large-scale deployments [100].
Security and Robustness Analysis
From a security and regulatory perspective, resilience to spoofing and fraud is a paramount concern.
- Spoofing Vulnerability: Unimodal systems are inherently more vulnerable to presentation attacks. For instance, fingerprint scanners can be spoofed with rubber fingerprints, and facial recognition systems can be fooled by photographs or deepfakes [100]. Multimodal systems significantly raise the difficulty for attackers, as they would need to simultaneously spoof multiple independent biometric traits to bypass the system [100]. The integration of advanced Presentation Attack Detection (PAD), often powered by AI to analyze micro-expressions and other subtle cues, is becoming a standard defense in modern multimodal systems [38].
- Data Integrity and Noise Resistance: A key strength of multimodal systems is their robustness to noisy or degraded data. If the sample from one biometric trait is of poor quality (e.g., a dirty fingerprint), the system can still make a reliable authentication decision based on the other, higher-quality trait (e.g., a facial image). This reduces the false rejection rates and improves the user experience without compromising security [100].
Methodological Protocols for Experimental Evaluation
For researchers designing experiments to validate biometric systems for regulatory purposes, the following methodological framework, derived from cited studies, ensures comprehensive and reproducible results.
Protocol 1: Deep Learning-Based Fingerprint and Vein Fusion
This protocol is adapted from the 2025 study that achieved 99.79% accuracy using a hybrid fusion approach [101].
- 1. Objective: To evaluate the performance gain of a multimodal system (FP + FV) over unimodal baselines using deep learning and different fusion strategies.
- 2. Dataset: Utilize a publicly available multimodal dataset such as NUPT-FPV or SDUMLA-HMT. The NUPT-FPV dataset contains 33,600 images from 140 subjects, captured with a dual-mode acquisition device under varied conditions [101].
- 3. Preprocessing: Standardize images (e.g., resizing, normalization). For finger vein images, apply techniques like ROI extraction and contrast enhancement.
- 4. Model Development:
- Unimodal Baselines: Implement two separate pretrained Convolutional Neural Networks (CNNs), such as MobileNetV1, one for FP and one for FV.
- Multimodal Models: Develop three models implementing:
- Feature-Level Fusion: Combine feature vectors from intermediate layers of the FP and FV CNNs before the final classification layer.
- Score-Level Fusion: Integrate the prediction scores (e.g., softmax outputs) from the two unimodal networks using a weighted average or other rules.
- Hybrid Fusion: Combine aspects of both feature and score-level fusion.
- 5. Training & Evaluation: Train all models on a training subset of the dataset. Evaluate on a held-out test set. Use key metrics: Accuracy, Equal Error Rate (EER), False Match Rate (FMR), and False Non-Match Rate (FNMR).
Figure 2: Experimental workflow for deep learning-based multimodal fusion evaluation.
Protocol 2: Smartphone-Based PPG and Fingerprint Authentication
This protocol outlines the methodology for a contactless, hardware-agnostic multimodal approach [44].
- 1. Objective: To develop a robust authentication system using only a smartphone camera by fusing PPG signals and fingerprints from video recordings.
- 2. Data Collection: Recruit participants to record videos of their index fingers placed on the smartphone's main camera lens with the flashlight enabled. Collect data in multiple sessions to evaluate time stability.
- 3. Signal Preprocessing:
- PPG Signal: Extract the raw PPG signal from the video. Segment it into individual heartbeats and normalize.
- Fingerprint Image: Extract fingerprint frames from the video. Apply image enhancement techniques.
- 4. Model Architecture: Implement a homogeneous neural network with two encoders based on a Structured State Space Model (SSM)—one for the PPG beat sequences and one for the flattened fingerprint pixel sequences. Incorporate a cross-modal attention mechanism to allow the modalities to inform each other's feature representation.
- 5. Training with Contrastive Loss: Use a distribution-oriented contrastive loss function to align the feature distributions of the two modalities in a unified latent space, improving generalization.
- 6. Evaluation: Test the system in both single-session and dual-session scenarios, reporting Accuracy and EER.
For scientists replicating or advancing this field, the following reagents, datasets, and computational tools are indispensable.
Table 4: Essential Research Reagents and Resources for Biometric System Validation
| Resource Type | Specific Example(s) | Function and Application in Research |
|---|---|---|
| Public Datasets | SDUMLA-HMT [101], NUPT-FPV [101], CASIA [101], FVC Datasets [101] | Provide standardized, multi-modal biometric data for training and benchmarking algorithms under controlled and comparable conditions. |
| Deep Learning Frameworks | TensorFlow, PyTorch | Provide the programming environment for developing and training CNN, SSM, and other neural network models for feature extraction and classification. |
| Pretrained CNN Models | MobileNetV1 [101] | Act as effective feature extractors or backbone networks, enabling transfer learning and reducing computational costs for model development. |
| Fusion Algorithms | Weighted Score Sum, Feature Concatenation, Hybrid Fusion [101] | The core algorithms that combine information from different biometric channels to improve the final decision-making. |
| Performance Metrics | Accuracy, Equal Error Rate (EER), FMR, FNMR [101] [44] | Standardized quantitative measures used to objectively evaluate and compare the performance of different biometric system architectures. |
This comparative framework demonstrates a clear, data-backed performance differential between unimodal and multimodal biometric architectures. While unimodal systems offer simplicity and lower cost, multimodal systems deliver quantitatively superior accuracy, significantly enhanced security against spoofing, and greater operational robustness in diverse, real-world conditions. For regulatory bodies and research professionals validating biometric monitoring technologies, these findings underscore the importance of considering multimodal approaches as the benchmark for high-stakes applications. The experimental protocols and resources detailed herein provide a foundational methodology for the continued empirical evaluation and validation of these critical systems.
The widespread deployment of face recognition systems for security and identity verification has been paralleled by the rapid evolution of sophisticated presentation attacks (PAs). Presentation Attack Detection (PAD)—or anti-spoofing—comprises the mechanisms and techniques designed to distinguish between genuine biometric traits and artificial presentation attack instruments (PAIs) created by imposters [102]. The urgency of robust PAD is underscored by an explosive growth in AI-driven fraud; deepfake content is projected to reach 8 million files in 2025, a staggering increase from 500,000 in 2023, while identity fraud attempts using deepfakes surged by 3,000% in 2023 alone [103]. The primary risk domains include financial fraud, such as CEO fraud and identity verification bypass, and a social crisis involving non-consensual intimate imagery [103]. This guide objectively compares PAD methodologies and their performance against modern deepfakes and synthetic identity fraud, providing researchers with a framework for evaluating these technologies within emerging regulatory contexts.
Comparative Analysis of PAD Mechanisms
PAD mechanisms can be broadly categorized into hardware-based and software-based approaches. Software-based methods, which are more prevalent, further branch into traditional handcrafted feature techniques and modern deep learning (DL)-based models [102].
Performance Metrics and the Security-Usability Trade-off
The effectiveness of PAD systems is quantified using several key metrics, the most critical being the False Acceptance Rate (FAR) and the False Rejection Rate (FRR).
- False Acceptance Rate (FAR): The rate at which an authentication system incorrectly authenticates an unauthorized user, such as accepting a deepfake or spoof as genuine. A high FAR represents a critical security failure [104].
- False Rejection Rate (FRR): The rate at which a system incorrectly rejects a legitimate, authorized user. A high FRR harms user experience and operational efficiency [105] [106].
These two metrics exist in a tension known as the security-usability trade-off. Adjusting the system's sensitivity threshold to lower the FAR will typically increase the FRR, and vice versa. The point where FAR and FRR are equal is known as the Equal Error Rate (EER), often used as a benchmark for a system's balanced accuracy [106] [104].
Table 1: Key Performance Metrics for Biometric PAD Systems
| Metric | Definition | Impact of a High Value | Typical Target for High-Security Environments |
|---|---|---|---|
| False Acceptance Rate (FAR) | Rate of unauthorized users being incorrectly accepted [104]. | Security breach; system is too trusting [104]. | Below 0.01% [104]. |
| False Rejection Rate (FRR) | Rate of legitimate users being incorrectly rejected [105]. | User frustration; increased support costs [106]. | Balanced with FAR at EER. |
| Equal Error Rate (EER) | The point where FAR equals FRR [106]. | Indicator of overall system balance. | As low as possible. |
| Human Detection Rate | Accuracy of humans detecting high-quality deepfakes. | High risk of social engineering bypass. | ~24.5% for video [103]. |
Quantitative Comparison of Deepfake Threats and PAD Performance
The performance of PAD systems must be evaluated against real-world threat vectors. The following table summarizes the scale and success rates of various attack types, illustrating the challenges faced by detection systems.
Table 2: 2025 Deepfake Attack Vectors and Documented PAD Bypass Rates
| Attack Vector | Targeted Sector(s) | Reported Success/Frequency | Key Enabling Technology |
|---|---|---|---|
| CEO Fraud / Vishing | Corporate Finance, Large Enterprises | Incidents from €220,000 to $25M; 1,740% growth in North America [103]. | Voice Cloning, Real-time Video Impersonation [103]. |
| ID Verification Bypass | Financial Services, Cryptocurrency, Fintech | 704% increase in attacks in 2023; 88% of deepfake fraud targets crypto [103]. | Face Swap, Virtual Camera Injection [103]. |
| Voice Cloning Scams | General Public, All Sectors | 1 in 4 adults have experienced a scam; 77% of those targeted lost money [103]. | AI voice synthesis from 3-second sample [103]. |
A critical finding from recent threat analysis is that the effectiveness of AI detection tools can plummet by 45-50% when moved from controlled lab conditions to real-world deployment [103]. This highlights a significant generalization gap in many PAD models and underscores the necessity for testing protocols that mirror operational environments.
Experimental Protocols for PAD Evaluation
To ensure regulatory frameworks are built on validated and reproducible science, standardized experimental protocols are essential.
Protocol for Assessing Face PAD against 2D Attacks
This protocol is designed to evaluate a system's resilience against common 2D presentation attacks like printed photos or screen replays.
1. Objective: To determine the False Acceptance Rate (FAR) and False Rejection Rate (FRR) of a Face PAD system against known 2D presentation attack instruments (PAIs). 2. Materials and Datasets:
- Genuine User Data: A dataset of live face videos or images from authorized users.
- PAI Data: A benchmark dataset containing spoofing attacks, such as the REPLAY-ATTACK dataset. This dataset includes print and video replay attacks and is commonly used in academic research for a standard comparison [102].
- Testing Platform: A system capable of calculating biometric matching and liveness scores. 3. Methodology:
- Data Partitioning: Divide the genuine and PAI data into training/validation and test sets, ensuring no user overlap between sets.
- Threshold Calibration: Use the validation set to establish a decision threshold that achieves a target FAR or EER.
- Blinded Testing: Evaluate the model on the held-out test set, presenting it with a randomized mix of genuine samples and PAIs.
- Metrics Calculation: Record the number of false accepts (PAIs classified as genuine) and false rejects (genuine samples classified as PAIs) to calculate FAR and FRR. 4. Analysis: Report the Half-Total Error Rate (HTER), which is the average of FAR and FRR, and the Attack Presentation Classification Error Rate (APCER) and Bona Fide Presentation Classification Error Rate (BPCER) as per ISO/IEC 30107-3 standards [102].
The workflow for this protocol can be summarized as follows:
Diagram 1: Face PAD evaluation workflow for 2D attacks.
Protocol for Testing Voice PAD against Deepfake Vishing
With deepfake vishing attacks surging by 1,633% in Q1 2025, testing voice authentication systems is critical [107].
1. Objective: To evaluate the resilience of a voice biometric system against AI-generated deepfake audio attacks. 2. Materials:
- Genuine Voiceprints: Enrolled voice templates of legitimate users.
- Deepfake Audio Samples: A corpus of synthetic voice clones. These can be generated using open-source tools (requiring only a 3-second sample for an 85% voice match) or curated from real-world attack data [103] [107].
- Testing Environment: A telephony or VoIP testing platform that can simulate live call conditions. 3. Methodology:
- Attack Simulation: Execute a series of authentication attempts using the deepfake audio samples against the enrolled voiceprints.
- Multi-condition Testing: Test under varying channel conditions (e.g., clean, noisy) to assess robustness.
- Threshold Stress-testing: Evaluate the system's FAR at different security threshold settings. 4. Analysis: Calculate the FAR specific to deepfake attacks. A 2025 study found that 25% of users fooled by a deepfake voice still complied with the request even when an alert was generated, emphasizing that technical metrics alone are insufficient and procedural safeguards are key [107].
To conduct rigorous PAD research and testing, a standard set of reagents, datasets, and software is required.
Table 3: Essential Research Reagents and Resources for PAD
| Resource Type | Example(s) | Function in PAD Research |
|---|---|---|
| Benchmark Datasets | REPLAY-ATTACK, other public anti-spoofing databases [102]. | Provides standardized, annotated data of genuine and spoofed presentations for training and fair comparison of PAD algorithms. |
| Deepfake Generation Tools | AI platforms like Xanthorox AI (used by threat actors), open-source GANs [103] [107]. | Used to generate synthetic PAIs for stress-testing and improving PAD mechanisms. |
| Biometric Software Development Kits (SDKs) | Commercial and open-source face & voice recognition SDKs. | Provides the core biometric verification functions onto which PAD layers are integrated. |
| Performance Evaluation Suites | Code libraries implementing ISO/IEC 30107-3 metrics (HTER, APCER, BPCER) [102]. | Standardizes the calculation and reporting of key performance indicators for objective comparison. |
Discussion and Future Directions
The current state of PAD reveals a challenging technological arms race. While deep learning-based PAD mechanisms show potential, they face crucial issues such as limited generalization to unknown attacks and performance degradation outside lab environments [102]. The proliferation of attack vectors—from face swaps bypassing liveness detection to real-time deepfake video conferences—demands a layered defense strategy [103].
Future research must focus on several key areas to validate PAD within robust regulatory frameworks:
- Improving Generalization: Developing models that can detect novel, "zero-day" presentation attacks not seen during training.
- Multimodal Fusion: Combining multiple biometric modalities (e.g., face and voice) or multiple PAD cues to create more resilient systems.
- Standardized Testing Protocols: Establishing rigorous, real-world testing protocols that regulatory bodies can mandate, moving beyond clean lab benchmarks.
- Procedural Safeguards: Acknowledging that purely technological solutions are insufficient. Regulations must also enforce procedural backstops, such as mandatory secondary verification for high-value transactions [103].
In conclusion, defending against deepfakes and synthetic identity fraud requires continuous independent validation of PAD technologies. By employing the comparative data, experimental protocols, and tools outlined in this guide, researchers and regulators can work towards a security paradigm where technological efficacy is proven, not presumed, thereby creating a more secure and trustworthy digital ecosystem.
The integration of digital biomarkers into clinical research and practice represents a paradigm shift in how we measure health and disease. Defined as objective, quantifiable, physiological and behavioral measures collected by portable, wearable, implantable, or digestible digital devices, digital biomarkers offer unprecedented opportunities for continuous, real-world data collection [108]. However, their adoption in regulated clinical research and regulatory decision-making hinges on a critical process: rigorous validation against established traditional clinical measures, often referred to as "gold standards" [19].
This validation ensures that digital biomarkers are fit-for-purpose—that they demonstrate sufficient analytical and clinical validity to support their intended use in drug development, clinical trials, or patient care [25]. The process bridges the gap between novel digital measurements and established clinical science, providing researchers and regulators with the confidence needed to utilize these tools for critical decisions. For researchers and drug development professionals, understanding and implementing robust validation frameworks is not merely academic; it is fundamental to the successful integration of digital biomarkers into the regulatory framework for biometric monitoring technologies [109].
Defining the Landscape: Digital Biomarkers Versus Traditional Measures
Core Characteristics and Comparative Advantages
Digital biomarkers differ from traditional biomarkers in several key aspects that influence both their utility and validation requirements. While traditional biomarkers are often well-embedded in clinical practice and research, they are frequently limited by their "snapshot" nature, providing only periodic measurements that may miss critical fluctuations in a patient's condition [108]. Common examples include laboratory tests like serum creatinine for kidney function or imaging studies for disease progression.
In contrast, digital biomarkers, derived from sensors in devices like smartwatches, patches, or smartphones, enable longitudinal and continuous measurements, capturing the dynamic nature of disease and treatment response in real-world environments [108] [110]. This fundamental difference presents both opportunities and challenges for validation.
Table 1: Comparative Characteristics of Traditional and Digital Biomarkers
| Characteristic | Traditional Biomarkers | Digital Biomarkers |
|---|---|---|
| Measurement Frequency | Episodic ("snapshot") | Continuous, longitudinal |
| Data Collection Setting | Clinical environment | Real-world, remote |
| Data Granularity | Limited data points | High-resolution, dense data |
| Invasiveness | Often invasive (e.g., blood draws) | Largely non-invasive |
| Proximity to Pathology | Typically close to pathological event | Often distal to pathological event |
| Data Complexity | Limited analytical complexity | Large, complex datasets |
The Classification Challenge: Biomarkers vs. Clinical Outcome Assessments
A critical consideration in validation is determining whether a digital measure functions as a biomarker or a Clinical Outcome Assessment (COA). This distinction significantly influences the validation pathway and regulatory requirements [109] [111].
- Digital Biomarkers measure biological or pathological processes (e.g., heart rate variability from a wearable ECG patch as an indicator of autonomic nervous system function) [109].
- Digital COAs capture how a patient feels, functions, or survives, and include Performance Outcomes (PerfOs), Patient-Reported Outcomes (PROs), Clinician-Reported Outcomes (ClinROs), and Observer-Reported Outcomes (ObsROs) [111].
Some digital measures can be classed as either, depending on context. For example, reduced mobility measured by a body-worn actigraphy device in heart failure patients could be considered a biomarker (as a prognostic factor for mortality) or a COA (as it assesses physical capacity meaningful to patients) [109]. This classification must be resolved early, as it dictates the appropriate gold standard comparator and validation methodology.
The Validation Framework: V3 for Digital Biomarkers
The foundation for validating digital biomarkers is the V3 framework (Verification, Analytical Validation, and Clinical Validation), which provides a structured approach to determining fit-for-purpose for Biometric Monitoring Technologies (BioMeTs) [19]. This framework adapts established practices from software engineering, laboratory science, and clinical validation to the unique challenges of digital measures.
Diagram 1: The V3 Validation Framework for BioMeTs
Phase 1: Verification
Verification constitutes the initial technical assessment, conducted primarily by hardware manufacturers. This phase focuses on evaluating sample-level sensor outputs to ensure the fundamental data collection components are functioning as specified [19].
Key Activities:
- In silico testing: Computational evaluation of sensor performance and signal processing algorithms under simulated conditions.
- In vitro bench testing: Laboratory-based assessment of sensor accuracy, precision, and reliability using calibrated reference systems and simulated physiological signals.
Verification answers the fundamental question: Does the technology itself perform reliably and consistently under controlled conditions? This phase establishes that the raw data generated by the BioMeT is technically sound before progressing to more complex human studies.
Phase 2: Analytical Validation
Analytical Validation bridges engineering and clinical expertise, translating the evaluation from the bench to human applications. This critical phase assesses the performance of data processing algorithms that convert raw sensor data into physiological or behavioral metrics [19].
Methodological Protocol:
- Controlled Human Studies: Recruit healthy participants and/or target patient populations for controlled data collection sessions.
- Synchronized Data Collection: Simultaneously collect data from the digital biomarker technology and a reference-grade laboratory or clinical system (the comparative gold standard).
- Algorithm Performance Metrics: Evaluate agreement between the digital biomarker and the reference standard using statistical measures including:
- Intra-class Correlation Coefficient (ICC) for test-retest reliability
- Bland-Altman analysis for bias and limits of agreement
- Pearson's or Spearman's correlation coefficients
- Sensitivity and specificity for classification algorithms
Analytical validation confirms that the derived metric (e.g., step count, heart rate, sleep stage) accurately reflects the physiological phenomenon it claims to measure when compared to an appropriate reference standard in human subjects.
Phase 3: Clinical Validation
Clinical Validation represents the final and most complex phase, demonstrating that the digital biomarker acceptably identifies, measures, or predicts a clinically meaningful state or experience in the intended context of use and population [19].
Experimental Approach:
- Target Population Studies: Conduct observational studies or clinical trials involving participants with and without the clinical condition of interest.
- Gold Standard Comparison: Compare the digital biomarker against established clinical endpoints, which may include:
- Traditional laboratory biomarkers (e.g., HbA1c for glycemic control)
- Imaging findings (e.g., MRI for disease progression)
- Clinical outcome assessments (e.g., 6-minute walk test for functional capacity)
- Clinician-rated scales (e.g., UPDRS for Parkinson's disease)
- Longitudinal Assessment: Evaluate the digital biomarker's ability to detect meaningful change over time, often in response to a therapeutic intervention or disease progression.
- Meaningful Change Thresholds: Establish the threshold for clinically important differences using anchor-based (correlation with patient-reported changes) or distribution-based (statistical measures of variability) methods [109].
Clinical validation provides the evidence that the digital biomarker does not just measure a physiological parameter accurately, but that this measurement matters in a clinical context and provides meaningful information about health status, disease progression, or treatment response.
Experimental Protocols and Methodologies
Protocol for Validating Active Digital Cognitive Biomarkers
Active digital cognitive biomarkers require participants to engage in specific tasks targeting cognitive domains (e.g., memory, attention, executive function) on digital platforms [112].
Experimental Design:
- Participant Cohort: Recruit a population spanning the range of cognitive function (healthy controls, mild cognitive impairment, dementia) with sample sizes sufficient for stratified analysis (typically n≥50 per group).
- Testing Protocol: Administer both the digital cognitive tasks and traditional neuropsychological assessments (e.g., MMSE, MoCA, ADAS-Cog) in a randomized or counterbalanced order to minimize practice effects.
- Validation Metrics:
- Convergent Validity: Correlate digital task scores with established paper-and-pencil tests measuring similar cognitive domains.
- Discriminant Validity: Demonstrate the digital biomarker's ability to distinguish between clinical groups (e.g., healthy vs. impaired) with appropriate statistical measures (ROC analysis, logistic regression).
- Test-Retest Reliability: Assess stability of measurements over short time intervals (1-2 weeks) in stable participants.
Example Implementation: In Parkinson's disease research, smartphone-based finger tapping tasks have been validated against clinician-rated motor scales (e.g., MDS-UPDRS Part III) as digital biomarkers of bradykinesia, demonstrating high correlation coefficients (r > 0.7) in appropriately powered studies [108].
Protocol for Validating Passive Digital Monitoring Biomarkers
Passive digital biomarkers are collected continuously without requiring specific patient tasks, using data from wearable sensors, smartphone interactions, or environmental monitors [112].
Experimental Design:
- Data Collection Framework: Deploy wearable sensors (accelerometers, gyroscopes, heart rate sensors) or smartphone applications to continuously collect passive data in real-world settings over extended periods (typically 2-4 weeks minimum).
- Gold Standard Reference: Establish appropriate reference standards, which may include:
- Clinical event diaries (e.g., seizure logs, fall reports)
- Clinician adjudication of events based on comprehensive assessment
- Established functional measures (e.g., 6-minute walk test, actigraphy)
- Feature Extraction and Algorithm Development: Extract relevant features from raw sensor data (e.g., gait speed, sleep duration, activity patterns) and develop classification or regression algorithms to map these features to clinical constructs.
- Validation Approach: Use appropriate cross-validation techniques (e.g., k-fold, leave-one-subject-out) to assess generalizability and avoid overfitting.
Case Example: In a study monitoring mobility in chronic heart failure, passively acquired accelerometer data was validated as a primary endpoint against the traditional 6-minute walk test, demonstrating significant correlation (r = 0.68) and sensitivity to treatment effects [108].
Table 2: Key Experimental Metrics for Digital Biomarker Validation
| Validation Type | Primary Metrics | Acceptance Criteria | Statistical Methods |
|---|---|---|---|
| Analytical Validation | Intra-class Correlation Coefficient (ICC) | ICC > 0.7 (good), > 0.9 (excellent) | Mixed effects models |
| Bland-Altman Limits of Agreement | Narrow 95% confidence intervals | Mean difference plots | |
| Coefficient of Variation (CV) | CV < 10% for precise measures | Standard deviation/mean | |
| Clinical Validation | Sensitivity/Specificity | Depends on context of use | ROC curve analysis |
| Correlation with Gold Standard | r > 0.6 (moderate), > 0.8 (strong) | Pearson/Spearman correlation | |
| Minimal Clinically Important Difference (MCID) | Established for target population | Anchor-based methods |
Case Studies in Digital Biomarker Validation
Stride Velocity 95th Centile (SV95C) in Neuromuscular Disorders
The qualification of Stride Velocity 95th Centile (SV95C) by the European Medicines Agency (EMA) represents a landmark achievement in digital biomarker validation [109] [110]. This digital endpoint was developed to measure ambulatory ability in patients with Duchenne Muscular Dystrophy (DMD) as an alternative to the traditional 6-minute walk test (6MWT).
Validation Protocol:
- Technology: Wearable inertial sensors worn at the ankle to continuously monitor gait parameters in real-world environments.
- Gold Standard Comparison: Validated against the 6MWT and North Star Ambulatory Assessment (NSAA) in controlled clinical settings.
- Clinical Validation: Demonstrated sensitivity to disease progression and treatment response in longitudinal studies.
- Regulatory Outcome: Qualified as a secondary endpoint by EMA, with studies showing that using SV95C could reduce required pivotal trial sample sizes by approximately 70% compared to traditional endpoints [110].
This case exemplifies a successful regulatory collaboration, establishing a new standard for digital biomarker validation in rare diseases.
Digital Cognitive Biomarkers in Psychiatry
The application of digital cognitive biomarkers in Major Depressive Disorder (MDD) illustrates the validation of active digital tasks for assessing treatment effects [112].
Implementation Example:
- Technology: A 2-Back variant of the N-Back paradigm implemented on an Apple Watch for longitudinal cognitive monitoring.
- Validation Approach: The digital task was correlated with traditional cognitive batteries and demonstrated sensitivity to pro-cognitive effects of antidepressant therapy.
- Adherence Metrics: Achieved adherence rates exceeding 95% in a clinical trial population, addressing a critical challenge in digital biomarker implementation.
This case highlights the importance of user engagement and adherence metrics alongside traditional validation parameters, particularly for digital measures deployed in real-world settings.
The Scientist's Toolkit: Essential Reagents and Solutions
Table 3: Essential Research Reagents for Digital Biomarker Validation
| Tool Category | Specific Examples | Function in Validation |
|---|---|---|
| Reference Standard Devices | Clinical-grade actigraphy systems (e.g., ActiGraph), ECG holter monitors, laboratory gait analysis systems | Provide gold-standard measurements for comparison during analytical validation |
| Signal Processing Tools | MATLAB Toolboxes, Python SciPy, R signal processing packages | Algorithm development, feature extraction, and data analysis |
| Data Annotation Platforms | REDCap, custom clinician annotation interfaces, electronic patient-reported outcome systems | Facilitate ground truth labeling for supervised algorithm training |
| Statistical Analysis Software | R, Python statsmodels, SPSS, SAS | Perform validation statistics including correlation, reliability, and sensitivity analysis |
| Clinical Outcome Assessments | 6-minute walk test equipment, standardized cognitive batteries (e.g., CANTAB), clinician-rated scales (e.g., UPDRS) | Serve as clinical comparators for establishing clinical validity |
| Data Quality Tools | Custom data pipeline monitoring, signal quality indices, outlier detection algorithms | Ensure data integrity throughout the validation process |
Validating digital biomarkers against traditional clinical measures is a methodical, multi-stage process that requires interdisciplinary collaboration and rigorous scientific approach. The V3 framework provides a structured pathway from technical verification to clinical validation, ensuring that digital biomarkers are fit-for-purpose for their intended use in clinical research and regulatory decision-making [19].
Successful validation requires:
- Appropriate gold standard selection based on the digital measure's intended function as a biomarker or clinical outcome assessment [109] [111]
- Robust statistical analysis of agreement, reliability, and sensitivity to change
- Establishment of clinically meaningful thresholds for interpretation in the target population [109]
- Transparent reporting of validation methodologies and results to facilitate regulatory review and scientific acceptance
As the field of digital medicine evolves, standardized validation approaches will be crucial for building an evidence base that supports the qualified use of digital biomarkers across therapeutic areas. By adhering to these rigorous benchmarking methodologies, researchers and drug development professionals can accelerate the adoption of digital biomarkers, ultimately enhancing the efficiency and effectiveness of clinical research and patient care.
The evolution of biometric technologies has transformed identity management across law enforcement, border security, and commercial applications. Biometric interoperability—the ability of different systems to exchange and use biometric data—has emerged as a critical requirement for large-scale identity management systems. This capability enables organizations to share data across jurisdictional boundaries and upgrade technologies without repeated enrolments. Supporting this technological ecosystem, the National Institute of Standards and Technology (NIST) has established itself as a foundational force in developing the technical standards and testing methodologies that ensure reliable and secure biometric data exchange [113] [114].
The significance of interoperability extends beyond technical compatibility. As noted in the National Biometrics Challenge report, interoperability is essential for biometric technology to fully meet large-scale identity governance requirements [115]. For researchers and professionals in regulatory framework validation, understanding the performance characteristics of different biometric data formats under standardized testing protocols provides critical insights for system design and policy development. This guide examines the compliance landscape through experimental data and standardized testing methodologies to validate the performance of biometric technologies against established regulatory frameworks.
NIST's Foundational Role in Biometric Standardization
NIST serves as an impartial developer of biometric standards and a leading testing organization, working in close partnership with other government agencies, industry, and academic institutions [113]. The institute's biometric activities encompass research on various modalities (fingerprint, face, iris, voice, DNA), standards development at national and international levels, and rigorous technology testing and evaluation that drives innovation [114]. Through its Biometric Standards Program, NIST supports the development of formal national and international standards that enable higher security for interoperable biometric-based personal authentication systems [113].
A cornerstone of NIST's approach is the development of conformance testing architectures and test tools for selected biometric technical interfaces and data interchange formats. These testing frameworks allow users to verify that implementations faithfully adhere to published specifications [113]. NIST has released several Conformance Test Suites (CTS), including one for the Biometric Application Programming Interface (BioAPI) and another for the Common Biometric Exchange Formats Framework (CBEFF) [113]. These tools help ensure that biometric systems from different vendors can interoperate effectively, a crucial requirement for government agencies and private sector organizations deploying biometric solutions.
Key Standards and Technical Contributions
NIST's standardization efforts have yielded significant technical infrastructure for the biometrics industry. The institute helped establish both the INCITS M1 national standards committee and the ISO/IEC JTC 1 SC37 international subcommittee for biometrics [113]. Through these channels, NIST has contributed to the publication of numerous American National Standards and international standards covering biometric technical interfaces, data interchange formats for various modalities, performance testing methodologies, and conformance testing methodologies [113].
These standards enable the open exchange of biometric data between different agencies and systems built by different manufacturers. They provide crucial guidance on how biometric systems should be tested, how results should be calculated and reported, and how to assess the quality of collected biometric samples [114]. The standards also ensure interoperability across the diverse ecosystem of government biometric systems, including those used by DHS, DOJ/FBI, DOD, and DOS [114]. For researchers validating regulatory frameworks, these standardized testing methodologies provide reproducible protocols for assessing system performance under controlled conditions.
Global Regulatory Framework for Biometric Data
The regulatory landscape for biometric data has evolved significantly as the technology proliferates across government and commercial sectors. In the United States, a patchwork of federal and state regulations governs the collection, use, and sharing of biometric data, while internationally, frameworks like the European Union's GDPR establish stringent requirements for biometric data protection.
United States Regulatory Landscape
The U.S. lacks a comprehensive federal biometric privacy law, creating a complex regulatory environment where compliance requirements vary significantly by jurisdiction:
Table 1: Comparison of Major U.S. Biometric Privacy Regulations
| Regulation | Jurisdiction | Consent Requirement | Private Right of Action | Key Provisions |
|---|---|---|---|---|
| Biometric Information Privacy Act (BIPA) | Illinois | Written consent required | Yes | Strict retention limits; public disposal policy; significant statutory damages |
| Capture or Use of Biometric Identifier Act (CUBI) | Texas | Consent required prior to capture | No (AG enforcement only) | Destruction within "reasonable time"; prohibition on sale of biometric data |
| California Privacy Rights Act (CPRA) | California | Opt-out approach for most uses | Yes | Treats biometric data as sensitive personal information; extensive consumer rights |
| Biometric Privacy Amendment | Colorado | Consent required before collection/use | No (AG enforcement) | Takes effect July 1, 2025; requires adoption of biometric policies |
| Biometric Privacy Protection Act | Washington | Affirmative consent required | Limited | Applies specifically to "enrolled" biometric identifiers |
At the federal level, the Federal Trade Commission (FTC) has emerged as a key enforcement authority through its jurisdiction over "unfair and deceptive trade practices" under the FTC Act [116]. In May 2023, the FTC issued a Policy Statement on Biometric Information specifically enumerating practices it considers deceptive or unfair, including unexpected collection of biometrics and failing to fully disclose how data will be used [116].
For government applications, agencies including the Department of Homeland Security (DHS), Department of Defense (DOD), and Department of Justice (DOJ) maintain extensive biometric systems with specialized governance frameworks. DHS's Automated Biometric Identification System (IDENT) represents one of the largest biometric repositories globally, containing over 320 million unique identities and processing approximately 400,000 biometric transactions daily [52]. These systems operate under specific statutory authorities and interoperability agreements that facilitate data sharing while implementing privacy and security controls.
International Regulatory Developments
Globally, regulatory approaches to biometric data continue to evolve. The European Union's GDPR classifies biometric data as a "special category" of personal data subject to strict processing limitations, while countries like Vietnam are implementing mandatory biometric national ID programs [117]. Vietnam's new digital ID law, effective July 2024, mandates collection of iris biometrics alongside fingerprints and facial images for citizen ID cards [117]. Meanwhile, Germany is engaged in ongoing debates about biometric surveillance, with lawmakers considering bans on certain applications of the technology amid concerns about constitutional compliance [117].
Experimental Assessment of Biometric Format Interoperability
Rigorous experimental assessment is essential for validating the interoperability of biometric data formats across different acquisition devices and systems. The following section presents methodologies and findings from a comprehensive study on hand biometric interoperability, providing researchers with reproducible protocols for evaluating standards compliance.
Methodology and Experimental Protocol
A landmark study on the interoperability of hand-based biometric schemes established a rigorous methodology for assessing cross-device compatibility [115]. The research created a substantial database of 8,320 hand images acquired from six different hand biometric schemes, representing diverse acquisition technologies:
- Acquisition Devices: Flat scanner, webcams at different wavelengths, high-quality cameras, and contactless devices
- Hand Aspects: Both palmar and dorsal (back) hand surfaces
- Imaging Conditions: Visible spectrum, near infrared, and multispectral imaging
- Sensor Types: Both contact-based and contactless acquisition
The experimental protocol evaluated four distinct feature extraction methods across two popular hand biometric modalities: hand shape and palm print. To address interdevice variability—a fundamental challenge in interoperability—the researchers proposed and implemented smoothing techniques at both the image and feature levels [115]. The testing framework followed standardized evaluation metrics including False Acceptance Rate (FAR), False Rejection Rate (FRR), and Equal Error Rate (EER) to enable objective performance comparisons across different system configurations.
Table 2: Experimental Results - Performance Comparison Across Modalities and Schemes
| Testing Scenario | Biometric Modality | Best Performing Method | Equal Error Rate (EER) | Interoperability Performance |
|---|---|---|---|---|
| Traditional (Same Device) | Hand Shape | Geometric Measurements | 2.1% | Baseline - Single device |
| Traditional (Same Device) | Palm Print | Local Feature Extraction (SIFT) | 1.8% | Baseline - Single device |
| Interoperable (Cross-Device) | Hand Shape | Geometric Measurements | 4.7% | Moderate performance drop |
| Interoperable (Cross-Device) | Palm Print | Local Feature Extraction (SIFT) | 8.3% | Significant performance drop |
| Interoperable with Smoothing | Hand Shape | Feature-level Smoothing | 3.2% | Improved interoperability |
| Interoperable with Smoothing | Palm Print | Image-level Smoothing | 5.1% | Moderate improvement |
Key Findings and Performance Analysis
The experimental results demonstrated several crucial patterns relevant to regulatory framework validation:
Interoperability Performance Gap: Both hand shape and palm print modalities experienced performance degradation in interoperable scenarios compared to traditional same-device configurations. However, the degradation was significantly more pronounced for palm prints (EER increased from 1.8% to 8.3%) than for hand shape (EER increased from 2.1% to 4.7%) [115].
Modality-Specific Characteristics: Hand shape biometrics demonstrated superior interoperability characteristics compared to palm prints in cross-device scenarios. The researchers attributed this to the relative stability of hand geometry features across different acquisition devices compared to the more texture-dependent palm print features [115].
Smoothing Efficacy: The proposed smoothing techniques at both image and feature levels demonstrated measurable improvements in interoperability performance. For hand shape biometrics, feature-level smoothing reduced the interoperability EER from 4.7% to 3.2%, while image-level smoothing provided greater benefits for palm print interoperability [115].
These findings highlight the critical importance of modality selection in system design and the potential for algorithmic mitigation of interoperability challenges. For researchers validating regulatory frameworks, these results underscore the need for modality-specific testing requirements in interoperability standards.
Essential Research Toolkit for Biometric Standards Validation
Researchers conducting validation studies for biometric standards compliance require specialized tools and resources. The following toolkit outlines essential components for experimental assessment of biometric format interoperability:
Table 3: Research Reagent Solutions for Biometric Standards Validation
| Tool/Resource | Function | Application in Standards Validation |
|---|---|---|
| NIST Conformance Test Suites (CTS) | Verification of standards implementation | Testing adherence to BioAPI, CBEFF, and other biometric standards |
| Biometric Image Quality Assessment Tools | Quantitative quality scoring | Ensuring sample quality meets minimum requirements for interoperability |
| Standardized Biometric Databases | Controlled test datasets | Benchmarking algorithm performance across modalities and devices |
| Interoperability Testing Framework | Cross-system performance evaluation | Measuring degradation in cross-device matching scenarios |
| Biometric Data Format Converters | Translation between standard formats | Testing backward compatibility and format migration scenarios |
NIST's Biometric Resource Center serves as a central repository for many testing tools and documentation, providing researchers with standardized resources for compliance testing [113]. The Conformance Test Suites for BioAPI and CBEFF enable verification that implementations correctly adhere to published standards, a fundamental requirement for regulatory validation [113].
For government-focused research, the IDENT Exchange Messages (IXM) specification and the Electronic Biometric Transmission Specification (EBTS) provide standardized messaging formats that enable data systems to communicate across organizational boundaries [52]. These specifications are particularly relevant for researchers validating frameworks for cross-agency biometric data sharing in law enforcement and homeland security contexts.
The experimental assessment of biometric data formats reveals several critical considerations for regulatory framework validation. First, the significant performance variation between biometric modalities in interoperable scenarios underscores the necessity for modality-specific standards rather than one-size-fits-all technical requirements. Second, the demonstrated efficacy of smoothing techniques in improving interoperability highlights the potential for algorithmic mitigation of cross-system performance degradation.
For researchers and professionals validating regulatory frameworks, these findings emphasize the importance of:
Comprehensive Testing Protocols: Regulatory validation must include rigorous cross-device and cross-system testing rather than single-device performance evaluation.
Performance Baseline Establishment: Realistic performance expectations should account for the interoperability gap observed in experimental settings.
Standardized Quality Metrics: Image and feature quality standards play a crucial role in maintaining interoperability across systems.
The ongoing development of biometric standards, including NIST's work on advanced conformance testing architectures with XML manifests and dynamic test module loading, points toward increasingly sophisticated validation methodologies [113]. As biometric technologies continue to evolve and expand into new applications, the foundational work on standards compliance and interoperability remains essential for ensuring both security and privacy in identity management systems.
For researchers in drug development and clinical settings, these validation frameworks provide crucial guidance for implementing compliant biometric monitoring technologies that maintain data integrity while respecting privacy regulations across multiple jurisdictions.
Conclusion
The successful integration of Biometric Monitoring Technologies into clinical research and drug development hinges on a rigorous, multi-faceted validation strategy grounded in the V3 framework. As of 2025, the convergence of advanced AI, multimodal systems, and stricter global regulations demands a proactive approach that balances technological innovation with ethical responsibility and regulatory compliance. Future progress will depend on continued collaboration between developers, researchers, and regulators to refine standards, enhance data security, and ensure these powerful tools are fit-for-purpose. The ongoing evolution of quantum-resistant encryption, decentralized identity management, and large-scale real-world data integration will further solidify the role of validated BioMeTs in shaping the future of personalized medicine and efficient drug development.
References
- 1. Wearables research for continuous monitoring of patient ... [https://journals.plos.org/digitalhealth/article?id=10.1371/journal.pdig.0000860]
- 2. A multi-modal dataset of electroencephalography and ... [https://www.nature.com/articles/s41597-025-05286-0]
- 3. Multimodal fNIRS–EEG sensor fusion: Review of data-driven ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12592382/]
- 4. EFRM: A Multimodal EEG–fNIRS Representation-learning ... [https://www.sciencedirect.com/science/article/abs/pii/S0010482525016464]
- 5. A review of big data and medical research - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7323266/]
- 6. A scoping review of artificial intelligence applications in ... [https://www.nature.com/articles/s41746-025-01886-7]
- 7. 2025 Clinical Data Trend Report [https://www.veeva.com/2025-clinical-data-trend-report/]
- 8. Regulation and technology in 2025 [https://www.biometricupdate.com/202503/regulation-and-technology-in-2025]
- 9. What is GDPR, the EU's new data protection law? [https://gdpr.eu/what-is-gdpr/]
- 10. Biometric Data GDPR Compliance Made Simple [https://gdprlocal.com/biometric-data-gdpr-compliance-made-simple/]
- 11. How do we process biometric data lawfully? [https://ico.org.uk/for-organisations/uk-gdpr-guidance-and-resources/lawful-basis/biometric-data-guidance-biometric-recognition/how-do-we-process-biometric-data-lawfully/]
- 12. GDPR vs HIPAA: A Comparison of Data Privacy Laws [https://www.atlassystems.com/blog/gdpr-vs-hipaa]
- 13. GDPR vs. HIPAA vs. CCPA vs. PCI: Compliance Differences [https://www.clouddefense.ai/gdpr-vs-hipaa-vs-ccpa-vs-pci/]
- 14. 2025 HIPAA Updates: Key Changes Every Organization ... [https://www.metricstream.com/blog/hipaa-updates-2025-key-changes.html]
- 15. HIPAA Security Rule To Strengthen the Cybersecurity of ... [https://www.federalregister.gov/documents/2025/01/06/2024-30983/hipaa-security-rule-to-strengthen-the-cybersecurity-of-electronic-protected-health-information]
- 16. California Consumer Privacy Act (CCPA) [https://oag.ca.gov/privacy/ccpa]
- 17. Data Protection in USA 2025 Comparison: HIPAA, CCPA ... [https://www.dwc-consult.com/en/blog-post/data-protection-in-usa-2025-comparison-hipaa-ccpa-cpra-tdpsa-co]
- 18. CCPA 2025 updated regulations: What's new, what's next, ... [https://www.dlapiper.com/en-us/insights/publications/2025/09/ccpa-2025-updated-regulations]
- 19. Verification, analytical validation, and clinical validation (V3) [https://www.nature.com/articles/s41746-020-0260-4]
- 20. Tapestry of Trust in Digital Medicine: The V3 Framework for ... [https://pharmafeatures.com/tapestry-of-trust-in-digital-medicine-the-v3-framework-for-biomets/]
- 21. Verification, Analytical Validation, and Clinical Validation (V3 ... [https://datacc.dimesociety.org/resources/the-v3-framework/]
- 22. V3+ extends the V3 framework to ensure user-centricity ... [https://www.nature.com/articles/s41746-024-01322-2]
- 23. The V3 Framework: Establishing Confidence in Digital ... [https://resources.jax.org/jax-blog/the-v3-framework-establishing-confidence-in-digital-measures]
- 24. Validation framework for in vivo digital measures - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11751004/]
- 25. Fit‐for‐Purpose Biometric Monitoring Technologies [https://pmc.ncbi.nlm.nih.gov/articles/PMC7877826/]
- 26. Grants and Funds Impacting Biometrics and Data ... [https://www.warmanobrien.com/resources/blog/grants-and-funds-impacting-biometrics-and-data-management-in-2025/]
- 27. For Small Businesses [https://arpa-h.gov/explore-funding/sbir]
- 28. Wearable Sensors Market Size, Share, and Forecast, 2025 ... [https://www.alliedmarketresearch.com/wearable-sensor-market]
- 29. Artificial Intelligence for Medical Diagnostics—Existing and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9955430/]
- 30. The Top 50 Healthcare Technology Companies of 2025 [https://thehealthcaretechnologyreport.com/the-top-50-healthcare-technology-companies-of-2025/]
- 31. Wearable Sensors and the Evaluation of Physiological ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11126008/]
- 32. Wearable Sensors Market 2025-2035: Technologies, ... [https://www.idtechex.com/en/research-report/wearable-sensors-market-2025/1051]
- 33. Transforming diagnosis through artificial intelligence [https://www.nature.com/articles/s41746-025-01460-1]
- 34. Liveness Detection: A Complete Guide for Fraud ... [https://sumsub.com/blog/face-liveness-detection/]
- 35. Facial Recognition Technology Trends 2025 Insights - andopen [https://andopen.co.kr/the-state-of-facial-recognition-technology-in-2025-accuracy-performance-and-future-trends/]
- 36. Inside Identiverse 2025: Biometrics at the Core of Digital Identity [https://www.aware.com/biometrics-at-the-core-of-digital-identity-blog/]
- 37. Facial Recognition Trends and Statistics [https://getsafeandsound.com/blog/facial-recognition-trends-and-statistics/]
- 38. What's on the Horizon: 10 Biometric Trends for 2025 [https://blog.hidglobal.com/whats-horizon-10-biometric-trends-2025]
- 39. Multimodal biometrics: the future of digital authentication [https://www.identy.io/multimodal-biometrics-the-future-of-digital-authentication/]
- 40. Biometric Innovations: What's Next Beyond Fingerprints [https://www.avatier.com/blog/biometric-innovations/]
- 41. Comparative Analysis of Different Biometric Techniques for ... [https://www.universepg.com/ajeit/comparative-analysis-of-different-biometric-techniques-for-security-systems]
- 42. The Future of Biometrics: Multimodal Security Solutions [https://www.jumio.com/biometrics-multimodal-approach/]
- 43. The utility of behavioral biometrics in user authentication ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10851515/]
- 44. Multimodal biometric authentication using camera-based ... [https://www.sciencedirect.com/science/article/abs/pii/S0167865525002454]
- 45. A comparative analysis of multi-biometrics performance in ... [https://www.sciencedirect.com/science/article/abs/pii/S0893608023005701]
- 46. Collection and Use of Biometrics by U.S. Citizenship ... [https://www.federalregister.gov/documents/2025/11/03/2025-19747/collection-and-use-of-biometrics-by-us-citizenship-and-immigration-services]
- 47. Cloud Data Protection: Best Practices & More [https://www.flexential.com/resources/blog/how-to-protect-cloud-data]
- 48. Cloud Security Best Practices: 10 Essential Steps [https://www.marjory.io/en/blog/cloud-security-best-practices]
- 49. 9 Cloud Application Security Best Practices [https://www.sentinelone.com/cybersecurity-101/cloud-security/cloud-application-security-best-practices/]
- 50. Enhancing Data Center Security: From Compliance to Best ... [https://bioconnect.com/blog/2024/05/29/enhancing-data-center-security-from-compliance-to-best-practices]
- 51. Scalability analysis comparisons of cloud -based software services [https://journalofcloudcomputing.springeropen.com/articles/10.1186/s13677-019-0134-y]
- 52. Biometrics [https://www.dhs.gov/biometrics]
- 53. Collection of Biometric Data From Aliens Upon Entry to and ... [https://www.federalregister.gov/documents/2025/10/27/2025-19655/collection-of-biometric-data-from-aliens-upon-entry-to-and-departure-from-the-united-states]
- 54. DHS proposes biometrics expansion for immigrants ... [https://www.nextgov.com/policy/2025/11/dhs-proposes-biometrics-expansion-immigrants-dropping-age-restrictions-and-requiring-biometrics-some-us-citizens/409274/]
- 55. Healthcare Biometrics Market Trends Shaping Digital Health [https://www.towardshealthcare.com/insights/healthcare-biometrics-market-sizing]
- 56. Healthcare Biometrics Market Size & Trends 2025-2035 [https://www.futuremarketinsights.com/reports/healthcare-biometrics-market]
- 57. Usability Challenges in Electronic Health Records: Impact on ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12206486/]
- 58. Solving Common EHR Integration Challenges in 2025 [https://hart.com/blog/solving-common-ehr-integration-challenges-in-2025]
- 59. Development of Novel, Value-Based, Digital Endpoints for ... [https://www.sciencedirect.com/science/article/abs/pii/S0031699724009761]
- 60. Verification, analytical validation , and clinical validation ... [https://pubmed.ncbi.nlm.nih.gov/32337371/]
- 61. Methods for Analytical Validation of Novel Digital Clinical ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12622859/]
- 62. Clinical Trial Technology Trends: 7 Powerful Positive ... [https://lifebit.ai/blog/clinical-trial-technology-trends/]
- 63. AI Bias in Healthcare: What Every C-Suite Needs to Know ... [https://www.baytechconsulting.com/blog/ai-bias-healthcare-risk-2025]
- 64. Bias recognition and mitigation strategies in artificial ... [https://www.nature.com/articles/s41746-025-01503-7]
- 65. Algorithmic bias in public health AI: a silent threat to equity in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12325396/]
- 66. Benchmarking for Biometric technology: Accuracy, ... [https://www.idemia.com/insights/benchmarking-ensuring-accuracy-fairness-security-biometric-algorithms]
- 67. Bias in Biometrics: How Organizations Can Launch ... [https://fidoalliance.org/bias-in-biometrics-how-organizations-can-launch-remote-identity-verification-confidently/]
- 68. Bias Mitigation in Primary Health Care Artificial Intelligence ... [https://www.jmir.org/2025/1/e60269/]
- 69. Encryption in 2025: Trends & Best Practices [https://ciphertex.com/2025/07/21/encryption-in-2025-trends-best-practices/]
- 70. Encryption Best Practices 2025: Guide to Data Protection [https://trainingcamp.com/articles/encryption-best-practices-2025-complete-guide-to-data-protection-standards-and-implementation/]
- 71. A Performance Comparison of the Homomorphic Encryption ... [https://eprint.iacr.org/2025/1460]
- 72. Blockchain Encryption in 2025: The Cryptographic ... [https://medium.com/@lamprostech/blockchain-encryption-in-2025-the-cryptographic-backbone-of-web3-security-aa14498b0fdc]
- 73. Top 5 Blockchain Security Issues in 2025 [https://101blockchains.com/blockchain-security-issues/]
- 74. Top 7 Blockchain Security Vulnerabilities Developers Still ... [https://securitybriefing.net/blockchain/top-7-blockchain-security-vulnerabilities-developers-still-miss-in-2025/]
- 75. Zero Trust Architecture in 2025: 7 Key Components [https://seraphicsecurity.com/learn/zero-trust/zero-trust-architecture-in-2025-7-key-components/]
- 76. 10 Zero Trust Vendors & Solutions in 2025 [https://www.sentinelone.com/cybersecurity-101/identity-security/zero-trust-vendors/]
- 77. What are the most innovative biometric sensors revolutionizing health and wellness monitoring, and how do their accuracy and reliability compare? Incorporate references from recent technological studies, comparisons of devices on health tech blogs, and URLs from reputable sites like IEEE Xplore or PubMed. [https://psico-smart.com/en/blogs/blog-what-are-the-most-innovative-biometric-sensors-revolutionizing-health-188159]
- 78. Using biometric data to improve our understanding and ... [https://link.springer.com/article/10.1007/s10270-025-01329-7]
- 79. Biometrics | Communication Research Center [https://sites.bu.edu/crc/research-groups/biometrics/]
- 80. Latest Trends from IAI 2025: Modernization, Cloud, and the ... [https://www.aware.com/latest-trends-from-iai-blog/]
- 81. Digital Identity Trends, Challenges and Powering Digital ... [https://www.entrust.com/blog/2025/08/digital-identity-trends-challenges-and-powering-digital-transformation]
- 82. New strict liability corporate criminal offence of failure to ... [https://www.mayerbrown.com/en/insights/publications/2025/09/eye-on-economic-crime-new-strict-liability-corporate-criminal-offence-of-failure-to-prevent-fraud-comes-into-effect]
- 83. The Current State of Biometrics Regulations, Technology, ... [https://www.authenticid.com/user-experience/the-current-state-of-biometrics-regulations-technology-and-sentiment/]
- 84. Failure to prevent fraud: steps to take before September 2025 [https://www.osborneclarke.com/insights/failure-prevent-fraud-steps-take-september-2025]
- 85. Using biometrics in financial crime prevention? Regulators ... [https://www.symphonyai.com/resources/blog/financial-services/biometrics-financial-crime-prevention-regulators/]
- 86. Biometric Technology Market is Projected to Reach USD ... [https://dimensionmarketresearch.com/report/biometric-technology-market/]
- 87. Biometric Technology Market Size and Forecast ... [https://www.researchnester.com/reports/biometrics-market/6394]
- 88. Biometrics in 2025: trends and technological innovations [https://www.biopassid.com/post/biometric-technology-trends]
- 89. Understanding the Benefits, Costs, and Challenges of ... [https://link.springer.com/article/10.1007/s44206-025-00177-8]
- 90. World Economic Forum looks to get a GRIP on global ... [https://www.biometricupdate.com/202507/world-economic-forum-looks-to-get-a-grip-on-global-regulatory-environment]
- 91. The Numbers Don't Lie: 70+ Biometric Statistics [2025] [https://www.iproov.com/blog/biometric-statistics-70]
- 92. What is Biometric Payments? Benefits and Challenges [https://acowebs.com/biometric-payments/]
- 93. Biometric Solutions Industry 2025: Top 10 Strategic ... [https://www.frost.com/growth-opportunity-news/security/commercial-public-security/top-10-strategic-imperatives-transforming-the-biometric-solutions-industry-in-2025-cim-pb/]
- 94. Biometric attendance system price in 2025 | Cost breakdown [https://mihcm.com/resources/blog/biometric-attendance-system-price-in-2025-how-much-does-it-cost/]
- 95. The Best Globally Top Ranked Face Recognition Algorithm ... [https://kby-ai.com/top-ranked-face-recognition/]
- 96. Iris Recognition Technology: A Complete Guide To Eye ... [https://tipsoi.pro/iris-recognition-biometric-technology/]
- 97. security - How can I calculate the Failed Acceptance and Rate ... false [https://stackoverflow.com/questions/30503766/how-can-i-calculate-the-failed-acceptance-rate-and-false-recognition-rate]
- 98. Iris Recognition in the Real World: 5 Uses You'll Actually ... [https://www.linkedin.com/pulse/iris-recognition-real-world-5-uses-youll-actually-see-2025-ryjfe]
- 99. How Banks and Fintech Will Verify in 2026: Regula Study [https://finance.yahoo.com/news/banks-fintech-verify-2026-regula-130000618.html]
- 100. Unimodal Biometrics vs. Multimodal Biometrics [https://www.bayometric.com/unimodal-vs-multimodal/]
- 101. Deep Learning-Based Fingerprint–Vein Biometric Fusion [https://www.mdpi.com/2076-3417/15/15/8502]
- 102. A survey on face presentation attack detection mechanisms [https://pmc.ncbi.nlm.nih.gov/articles/PMC10025066/]
- 103. Deepfake Statistics 2025: AI Fraud Data & Trends [https://deepstrike.io/blog/deepfake-statistics-2025]
- 104. What is false acceptance rate? [https://www.pindrop.com/glossary/false-acceptance-rate/]
- 105. What is False Rejection Rate (FRR)? [https://facia.ai/knowledgebase/what-is-false-rejection-rate-frr/]
- 106. False Rejection Rate (FRR): Meaning & Value [https://microblink.com/resources/blog/false-rejection-rate/]
- 107. The State of Deep Fake Vishing Attacks in 2025 [https://right-hand.ai/blog/deep-fake-vishing-attacks-2025/]
- 108. Traditional and Digital Biomarkers: Two Worlds Apart? - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7015353/]
- 109. Digital health technology derived measures: Biomarkers or ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10339690/]
- 110. Digital measurement and digital biomarkers [https://www.deloitte.com/us/en/insights/industry/life-sciences/digital-measurement-and-digital-biomarkers-are-the-future-of-healthcare.html]
- 111. Biomarkers vs. Clinical Outcome Assessments (COA) ... [https://www.vivosense.com/biomarkers-vs-clinical-outcome-assessments-coa-vs-endpoints/]
- 112. What is the optimal approach for using digital cognitive ... [https://cambridgecognition.com/what-is-the-optimal-approach-for-using-digital-cognitive-biomarkers-in-clinical-trials/]
- 113. Biometric Standards Program and Resource Center | NIST [https://www.nist.gov/programs-projects/biometric-standards-program-and-resource-center]
- 114. Biometrics | NIST [https://www.nist.gov/programs-projects/biometrics]
- 115. On the Feasibility of Interoperable Schemes in Hand ... [https://www.mdpi.com/1424-8220/12/2/1352]
- 116. U.S. Biometric Data Laws [https://www.tcwglobal.com/blog/u.s.-biometric-data-law]
- 117. Update On Global Biometric Laws [https://hallboothsmith.com/update-global-biometric-laws/]